Nowadays, the LockBit ransomware is the most active and successful cybercrime organization in the world. Attributed to a Russian Danger Actor, LockBit has stepped out from the shadows of the Conti ransomware group, who were being disbanded in early 2022.
LockBit ransomware was 1st uncovered in September 2019 and was earlier known as ABCD ransomware simply because of the “.abcd virus” extension initially noticed. LockBit operates as a Ransomware-as-a-provider (RaaS) model. In limited, this indicates that affiliates make a deposit to use the software, then split the ransom payment with the LockBit group. It has been noted that some affiliate marketers are acquiring a share as superior of 75%. LockBit’s operators have posted advertisements for their affiliate software on Russian-language prison message boards stating they will not work in Russia or any CIS international locations, nor will they operate with English-talking builders unless a Russian-speaking “guarantor” vouches for them.
First attack vectors of LockBit involve social engineering, these kinds of as phishing, spear phishing, and business enterprise email compromise (BEC), exploiting community-facing applications, choosing initial entry brokers” (IABs), and using stolen credentials to obtain legitimate accounts, this kind of as remote desktop protocol (RDP), as effectively as brute-pressure cracking attacks.
During past year’s Global Menace Forecast webinar, hosted by SecurityHQ, we determined LockBit as a substantial threat and highlighted them as a Danger Actor to shell out near consideration to throughout 2022.
LockBit Targets
LockBit has commonly centered assaults on governing administration entities and enterprises in a variety of sectors, this sort of as health care, economical expert services, and industrial goods and companies. The ransomware has been observed focusing on international locations globally, like the US, China, India, Indonesia, Ukraine, France, the British isles, and Germany.
An additional attention-grabbing function of LockBit is that it is programmed in a way that it simply cannot be made use of in attacks towards Russia or CIS nations (Commonwealth of Independent States). This is probably a precautionary measure taken by the team to avoid any prospective backlash from the Russian governing administration.
The map below reveals the locations specific by LockBit.
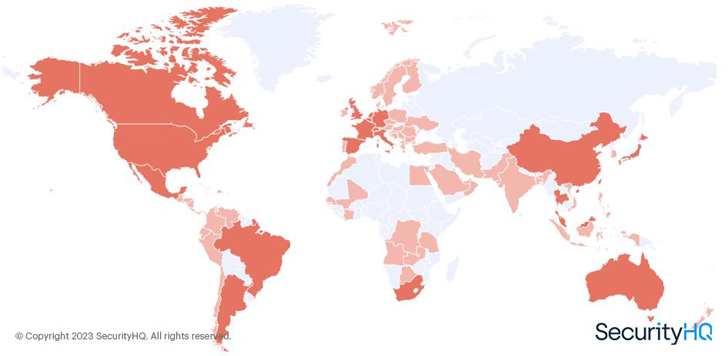 Determine 1 – SecurityHQ Analysis of LockBit Victims Per Geography
Determine 1 – SecurityHQ Analysis of LockBit Victims Per Geography
A Chaotic Year for LockBit
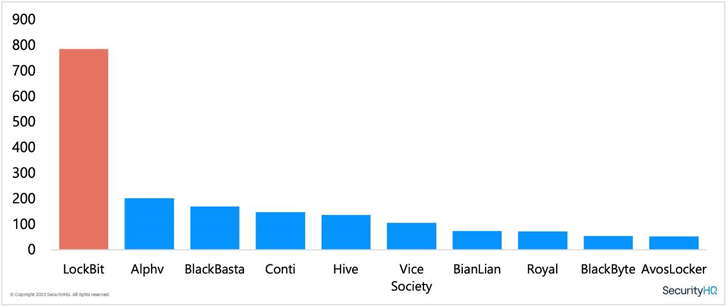
By means of investigation of leak web page data, we had been equipped to get a real photograph of how several successful attacks LockBit had designed. In 2022, the team published a lot more prosperous assaults than any other ransomware team. We have mapped the activity of LockBit throughout the year from other well-regarded ransomware groups. You can see the decrease of Conti as the team started off to shut down functions. It is now documented nonetheless, that members of the as soon as prolific Conti ransomware team are now running inside the BlackBasta, BlackByte and Karakurt ransomware teams.
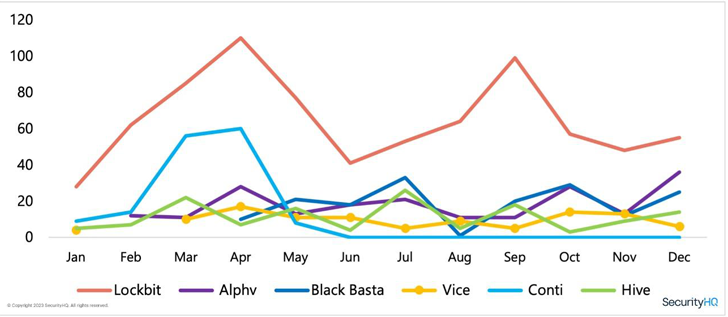
The graph underneath demonstrates how active LockBit have been in the course of 2022, as opposed to other ransomware groups.
A person of the exclusive functions of LockBit is their bug bounty method for their ransomware builders and compilers. The team delivers a $1 million reward for any one who can dox (publicly expose the identities of) their proprietors. This is a considerable sum, and it shows how really serious LockBit is about protecting their anonymity.
Lately, the group has been joined to an attack on Royal Mail in the British isles. On the other hand, LockBit has denied any involvement in the attack, stating that it was carried out by an affiliate. This is not unusual for ransomware teams, as they usually use affiliates to have out attacks in order to distance them selves from the outcomes.
Total, the LockBit ransomware team is a formidable and sophisticated cybercrime business that poses a important threat to companies and companies close to the earth. With a properly-established ransomware-as-a-support product, a bug bounty method, and a willingness to reward people who expose their identities, LockBit is a pressure to be reckoned with in the risk landscape.
What is RaaS?
Ransomware-as-a-services (RaaS) has gained popularity in current years. RaaS refers to a variety of business product where ransomware operators offer the malware and resources to other persons or organised criminal offense groups to have out ransomware assaults, in trade for a share of the ransom payment. This makes it possible for even considerably less technically competent people today to take part in ransomware assaults, raising the amount of assaults and generating it more complicated to keep track of and apprehend the attackers.
What to Do Next
To improve your security posture, it is recommended that enterprises do the following actions:
To hear to SecurityHQ authorities examine some of the best threats seen all over 2022, explore the effects of a breach, with predictions for 2023, and how to mitigate from impending cyber security threats, download this webinar recording’ World Risk Landscape 2023 Forecast’, to know much more.
Be aware: This post is by Aaron Hambleton, Director for Middle East & Africa at SecurityHQ. With over 11 decades of expertise across different sectors like Money Solutions, Retail, Coverage, Govt, and Telecommunications, Aaron is a qualified GCDA and has know-how in incident reaction, risk looking, vulnerability management, cyber security operations, danger intelligence, and consultancy.
Discovered this post interesting? Follow us on Twitter and LinkedIn to study extra distinctive articles we article.
Some parts of this article are sourced from:
thehackernews.com


 UK Crypto Firm Loses $200m in Cyber-Attack
UK Crypto Firm Loses $200m in Cyber-Attack