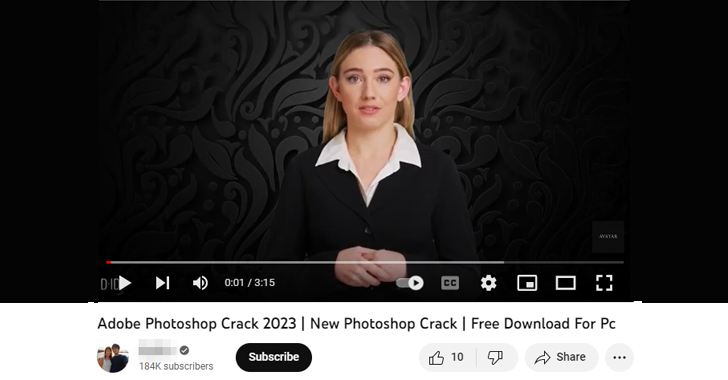
Danger actors have been ever more observed working with AI-generated YouTube Videos to unfold a assortment of stealer malware these kinds of as Raccoon, RedLine, and Vidar.
“The films entice end users by pretending to be tutorials on how to download cracked variations of application such as Photoshop, Premiere Pro, Autodesk 3ds Max, AutoCAD, and other products and solutions that are accredited items available only to paid users,” CloudSEK researcher Pavan Karthick M said.
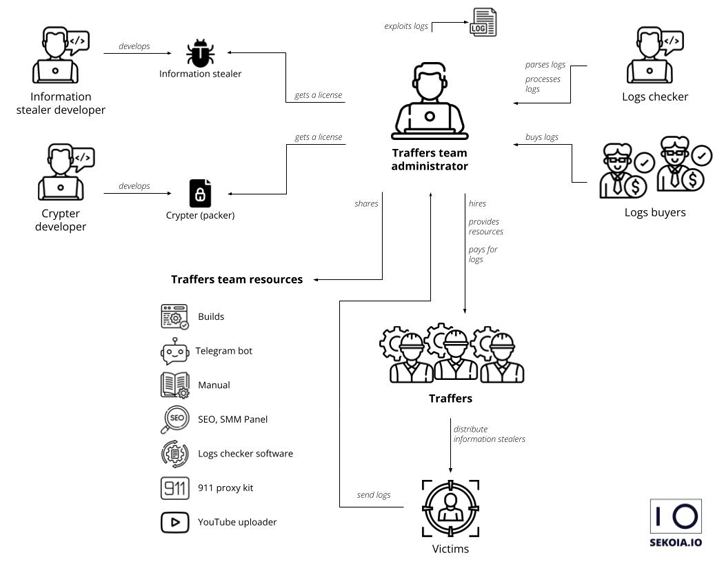
Just as the ransomware landscape contains main builders and affiliates who are in charge of pinpointing prospective targets and really carrying out the attacks, the data stealer ecosystem also is made up of menace actors acknowledged as traffers who are recruited to unfold the malware applying various strategies.
1 of the well known malware distribution channels is YouTube, with CloudSEK witnessing a 200-300% month-above-thirty day period raise in videos containing links to stealer malware in the description section.
These one-way links are generally obfuscated applying URL shorteners like Bitly and Cuttly, or alternatively hosted on MediaFire, Google Push, Discord, GitHub, and Telegram’s Telegra.ph.
In numerous scenarios, danger actors leverage data leaks and social engineering to hijack respectable YouTube accounts and push malware, typically targeting common accounts to arrive at a significant audience in a limited span of time.
“Uploading to these accounts lends movie legitimacy as effectively,” Karthick spelled out. “However, these types of Youtubers will report their account taker to YouTube and obtain access again to their accounts inside a couple hours. But in a several hours, hundreds of buyers could have fallen prey.”
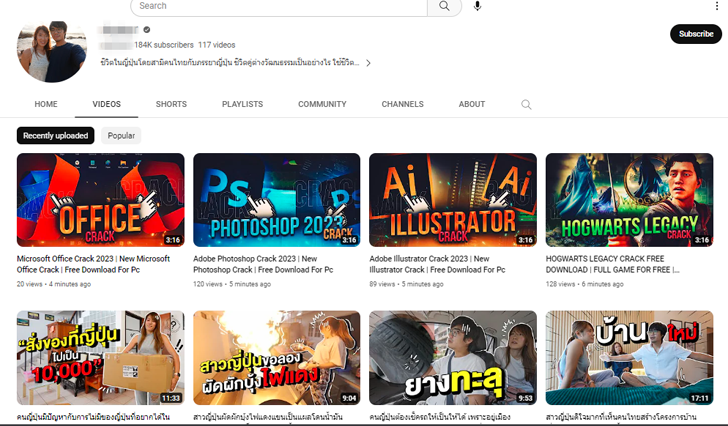
Additional ominously, everywhere amongst five to 10 crack obtain video clips are uploaded to the online video system each hour, with the danger actors using lookup engine optimization (Search engine optimization) poisoning techniques to make the videos look at the leading of the checklist.
Menace actors have also been observed to include faux comments to the uploaded films to more mislead and entice buyers into downloading the cracked computer software.
WEBINARDiscover the Concealed Risks of 3rd-Party SaaS Apps
Are you conscious of the challenges related with 3rd-bash app obtain to your company’s SaaS apps? Be a part of our webinar to master about the forms of permissions currently being granted and how to lower risk.
RESERVE YOUR SEAT
The enhancement will come amid a surge in new details stealer variants like SYS01stealer, S1deload, Stealc, Titan, ImBetter, WhiteSnake, and Lumma that are available for sale and arrive with capabilities to plunder sensitive info beneath the guise of well-known apps and solutions.
The findings also comply with the discovery of a ready-to-use toolkit named R3NIN Sniffer that can help menace actors to siphon payment card details from compromised e-commerce web-sites.
To mitigate challenges posed by stealer malware, buyers are advisable to allow multi-issue authentication, refrain from clicking on not known backlinks, and stay away from downloading or utilizing pirated application.
Discovered this article appealing? Observe us on Twitter and LinkedIn to examine additional exceptional articles we article.
Some parts of this article are sourced from:
thehackernews.com

 Final Three Sentenced in £70m Money Laundering Case
Final Three Sentenced in £70m Money Laundering Case