A new variant of the Android banking trojan named Xenomorph has surfaced in the wild, the most current conclusions from ThreatFabric reveal.
Named “Xenomorph 3rd technology” by the Hadoken Security Group, the danger actor driving the operation, the updated variation comes with new features that let it to execute money fraud in a seamless method.
“This new model of the malware provides quite a few new capabilities to an now function-prosperous Android banker, most notably the introduction of a incredibly considerable runtime motor run by Accessibility companies, which is employed by actors to put into action a comprehensive ATS framework,” the Dutch security company said in a report shared with The Hacker News.
Xenomorph very first arrived to mild a calendar year in the past in February 2022, when it was uncovered to focus on 56 European banking companies through dropper apps published on the Google Participate in Retail outlet.
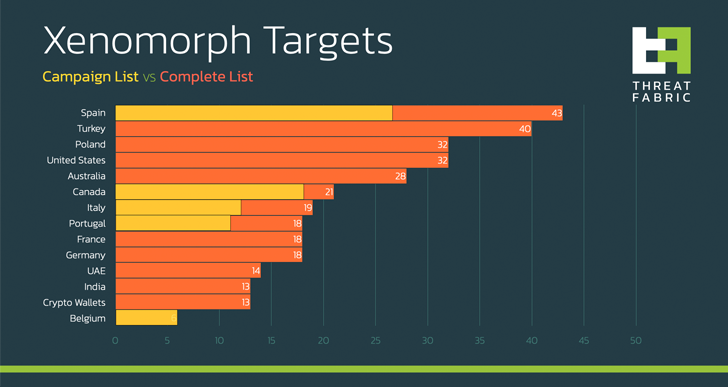
In contrast, the hottest iteration of the banker – which has a focused site promoting its capabilities – is developed to concentrate on more than 400 banking and economical institutions, like many cryptocurrency wallets.
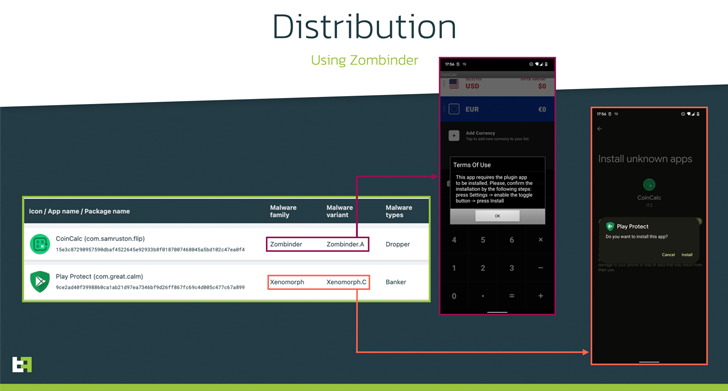
ThreatFabric mentioned it detected samples dispersed through Discord’s Written content Shipping and delivery Network (CDN), a system that has witnessed a surge because 2020. Two of the Xenomorph-laced applications are outlined below –
- Participate in Safeguard (com.excellent.quiet)
- Play Guard (meritoriousness.mollah.presser)
“Xenomorph v3 is deployed by a Zombinder app ‘bound’ to a respectable forex converter, which downloads as an ‘update’ an software posing as Google Secure,” ThreatFabric spelled out.
Zombinder refers to an APK binding services marketed on the dark web considering that March 2022, whereby the malware is sent by means of trojanized variations of genuine applications. The presenting has given that been shut down.
Targets of the hottest campaign go outside of its European focus (i.e., Spain, Italy, and Portugal) to contain Belgian and Canadian economical entities.
WEBINARDiscover the Concealed Hazards of Third-Party SaaS Apps
Are you mindful of the challenges associated with third-celebration app access to your company’s SaaS applications? Be a part of our webinar to understand about the varieties of permissions currently being granted and how to lower risk.
RESERVE YOUR SEAT
Xenomorph, like banking malware, is regarded to abuse Accessibility Products and services to perform fraud by means of overlay attacks. It also packs in abilities to immediately comprehensive fraudulent transactions on infected gadgets, a strategy called Automated Transfer System (ATS).
With financial institutions moving away from SMS for two-factor authentication (2FA) to authenticator apps, the Xenomorph trojan incorporates an ATS module that makes it possible for it to start the app and extract the authenticator codes.
The Android malware even more features of cookie-stealing features, enabling the danger actors to execute account takeover assaults.
“With these new capabilities, Xenomorph is now able to completely automate the whole fraud chain, from infection to money exfiltration, creating it a single of the most advanced and risky Android Malware trojans in circulation,” the company mentioned.
Identified this report appealing? Adhere to us on Twitter and LinkedIn to read extra unique information we publish.
Some parts of this article are sourced from:
thehackernews.com

 North Korean UNC2970 Hackers Expands Operations with New Malware Families
North Korean UNC2970 Hackers Expands Operations with New Malware Families