Destructive actors can acquire gain of “inadequate” forensic visibility into Google Cloud System (GCP) to exfiltrate delicate data, a new investigation has found.
“Unfortunately, GCP does not deliver the level of visibility in its storage logs that is wanted to permit any effective forensic investigation, generating companies blind to possible knowledge exfiltration attacks,” cloud incident response agency Mitiga mentioned in a report.
The attack banks on the prerequisite that the adversary is in a position to acquire control of an id and obtain administration (IAM) entity in the targeted group by techniques like social engineering to accessibility the GCP atmosphere.
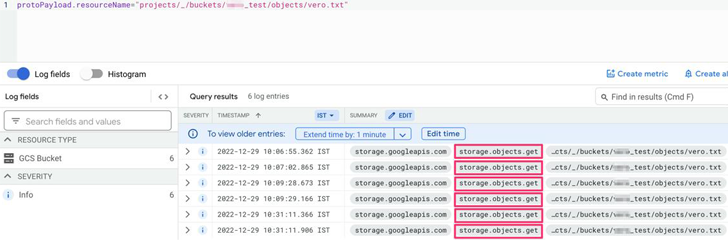
The crux of the trouble is that GCP’s storage access logs do not provide adequate transparency with regards to potential file access and examine functions, instead grouping them all as a single “Object Get” exercise.
“The similar party is made use of for a large wide range of forms of accessibility, like: Reading through a file, downloading a file, copying a file to an external server, [and] reading through the metadata of the file,” Mitiga researcher Veronica Marinov mentioned.
This absence of distinction could allow an attacker to harvest delicate info with no staying detected, largely for the reason that there is no way to differentiate between destructive and legit consumer action.
In a hypothetical attack, a risk actor can use Google’s command line interface (gsutil) to transfer useful details from the victim organization’s storage buckets to an exterior storage bucket inside of the attacker corporation.
Learn the Most current Malware Evasion Strategies and Prevention Procedures
Completely ready to bust the 9 most perilous myths about file-primarily based attacks? Be a part of our upcoming webinar and become a hero in the battle towards affected person zero bacterial infections and zero-day security gatherings!
RESERVE YOUR SEAT
Google has because delivered mitigation recommendations, which array from Virtual Non-public Cloud (VPC) Services Controls to working with organization restriction headers to restrict cloud resource requests.
The disclosure comes as Sysdig unearthed a subtle attack marketing campaign dubbed SCARLETEEL which is targeting containerized environments to perpetrate theft of proprietary details and program.
Uncovered this report interesting? Follow us on Twitter and LinkedIn to go through additional special material we write-up.
Some parts of this article are sourced from:
thehackernews.com


 UK Government Plans Skills Boost for Public Sector Fraud Fight
UK Government Plans Skills Boost for Public Sector Fraud Fight