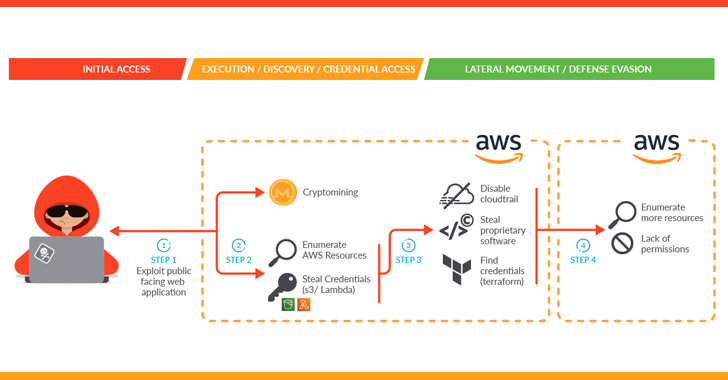
A innovative attack marketing campaign dubbed SCARLETEEL is focusing on containerized environments to perpetrate theft of proprietary info and application.
“The attacker exploited a containerized workload and then leveraged it to complete privilege escalation into an AWS account in buy to steal proprietary software program and qualifications,” Sysdig mentioned in a new report.
The highly developed cloud attack also entailed the deployment of crypto miner software, which the cybersecurity company said is both an try to generate illicit gains or a ploy to distract defenders and throw them off the path.
The original an infection vector banked on exploiting a susceptible general public-dealing with support in a self-managed Kubernetes cluster hosted on Amazon Web Products and services (AWS).
On attaining a thriving foothold, an XMRig crypto miner was launched and a bash script was utilised to get credentials that could be used to more burrow into the AWS cloud infrastructure and exfiltrate sensitive knowledge.
“Either crypto mining was the attacker’s preliminary purpose and the aim changed when they accessed the victim’s surroundings, or crypto mining was made use of as a decoy to evade the detection of knowledge exfiltration,” the corporation reported.

The intrusion notably also disabled CloudTrail logs to decrease the digital footprint, avoiding Sysdig from accessing additional evidence. In all, it allowed the threat actor to access more than 1TB of facts, like consumer scripts, troubleshooting resources, and logging data files.
“They also tried to pivot utilizing a Terraform condition file to other related AWS accounts to distribute their get to through the business,” the organization stated. This, nonetheless, proved to be unsuccessful thanks to lack of permissions.
The conclusions come months after Sysdig also in-depth another cryptojacking marketing campaign mounted by the 8220 Gang concerning November 2022 and January 2023 focusing on exploitable Apache web server and Oracle Weblogic programs.
Identified this article fascinating? Follow us on Twitter and LinkedIn to examine more unique articles we write-up.
Some parts of this article are sourced from:
thehackernews.com

 WH Smith Discloses Cyber-Attack, Company Data Theft
WH Smith Discloses Cyber-Attack, Company Data Theft