Cryptocurrency companies are getting targeted as aspect of a new marketing campaign that provides a remote access trojan known as Parallax RAT.
The malware “employs injection approaches to cover inside of respectable processes, building it hard to detect,” Uptycs reported in a new report. “At the time it has been correctly injected, attackers can interact with their target via Windows Notepad that probably serves as a conversation channel.”
Parallax RAT grants attackers distant obtain to sufferer devices. It comes with characteristics to upload and down load files as effectively as file keystrokes and monitor captures.
It has been put to use due to the fact early 2020 and was earlier delivered via COVID-19-themed lures. In February 2022, Proofpoint thorough a cybercrime threat actor dubbed TA2541 concentrating on aviation, aerospace, transportation, production, and defense industries applying different RATs, including Parallax.
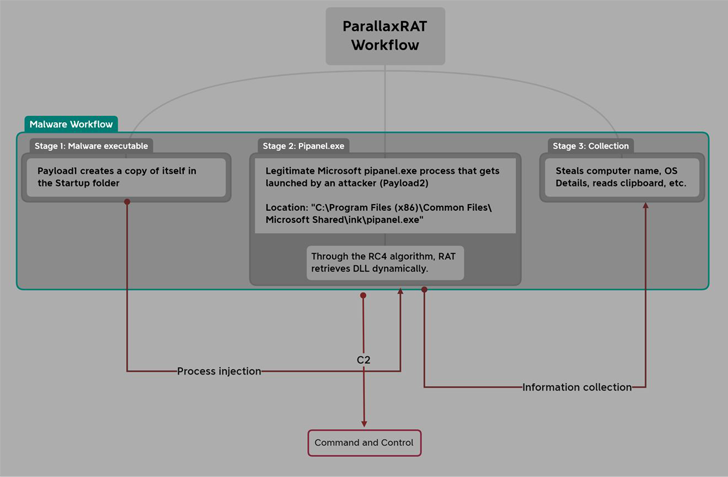
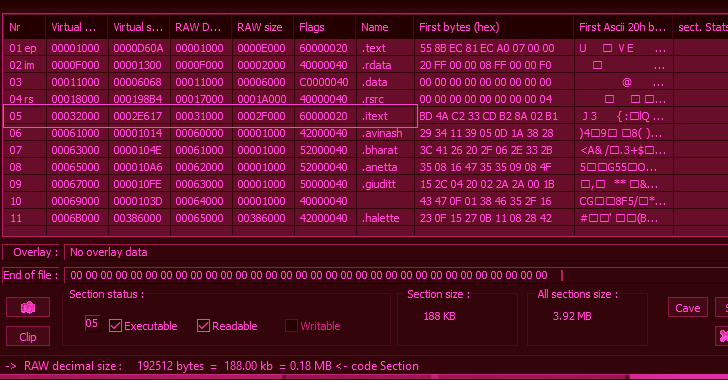
The very first payload is a Visible C++ malware that employs the approach hollowing system to inject Parallax RAT into a respectable Windows component termed pipanel.exe.
Parallax RAT, besides collecting technique metadata, is also able of accessing info saved in the clipboard and even remotely rebooting or shutting down the compromised device.
Just one notable part of the attacks is the use of the Notepad utility to initiate discussions with the victims and instructing them to join to an actor-controlled Telegram channel.
Uptycs’ investigation of the Telegram chat reveals that the risk actor has an desire in crypto providers these kinds of as investment decision firms, exchanges, and wallet services suppliers.
The modus operandi involves browsing community resources like DNSdumpster for determining mail servers belonging to the focused corporations through their mail exchanger (MX) records and sending phishing emails bearing the Parallax RAT malware.
The improvement will come as Telegram is ever more turning out to be a hub for criminal pursuits, enabling danger actors to arrange their operations, distribute malware, and aid the sale of stolen information, and other unlawful products in element owing to the platform’s lax moderation efforts.
“A single reason why Telegram is interesting to cybercriminals is its alleged constructed-in encryption and the skill to produce channels and substantial, private teams,” KELA disclosed in an exhaustive analysis released last thirty day period.
“These options make it tricky for regulation enforcement and security researchers to monitor and observe legal exercise on the platform. In addition, cybercriminals generally use coded language and alternative spellings to talk on Telegram, generating it even far more demanding to decipher their conversations.”
Uncovered this article attention-grabbing? Abide by us on Twitter and LinkedIn to study far more distinctive content we post.
Some parts of this article are sourced from:
thehackernews.com

 Scientists make major breakthrough in developing practical quantum computers that can solve big challenges of our time
Scientists make major breakthrough in developing practical quantum computers that can solve big challenges of our time