A beforehand undocumented Chinese-talking highly developed persistent menace (APT) actor dubbed Aoqin Dragon has been linked to a string of espionage-oriented assaults aimed at governing administration, education, and telecom entities mainly in Southeast Asia and Australia dating as significantly back again as 2013.
“Aoqin Dragon seeks preliminary access principally by means of document exploits and the use of pretend removable gadgets,” SentinelOne researcher Joey Chen stated in a report shared with The Hacker Information. “Other approaches the attacker has been observed using contain DLL hijacking, Themida-packed files, and DNS tunneling to evade submit-compromise detection.”
The team is said to have some amount of affiliation with yet another risk actor recognized as Naikon (aka Override Panda), with campaigns generally directed towards targets in Australia, Cambodia, Hong Kong, Singapore, and Vietnam.
Infections chains mounted by Aoqin Dragon have banked on Asia-Pacific political affairs and pornographic-themed document lures as very well as USB shortcut approaches to trigger the deployment of a single of two backdoors: Mongall and a modified variation of the open-resource Heyoka task.
This associated leveraging old and unpatched security vulnerabilities (CVE-2012-0158 and CVE-2010-3333), with the decoy paperwork engaging targets into opening the files. More than the several years, the menace actor also utilized executable droppers masquerading as antivirus computer software to deploy the implant and connect to a remote server.
“While executable data files with faux file icons have been in use by a range of actors, it continues to be an productive resource primarily for APT targets,” Chen discussed. “Put together with ‘interesting’ email information and a catchy file identify, people can be socially engineered into clicking on the file.”
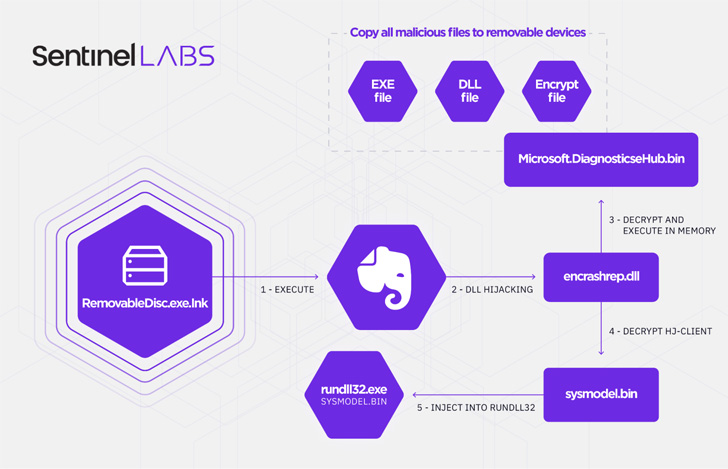
That said, Aoqin Dragon’s latest original obtain vector of preference since 2018 has been its use of a fake removable device shortcut file (.LNK), which , when clicked, runs an executable (“RemovableDisc.exe”) that athletics the icon for the popular note-having application Evernote but is engineered to functionality as a loader for two different payloads.
One of the factors in the an infection chain is a spreader that copies all malicious files to other detachable products and the second module is an encrypted backdoor that injects alone into rundll32’s memory, a indigenous Windows system made use of to load and operate DLL files.

Recognised to be applied since at least 2013, Mongall (“HJ-client.dll”) is explained as a not-so “significantly function wealthy” implant but one that packs adequate options to develop a distant shell and add and download arbitrary information to and from the attacker-management server.
Also made use of by the adversary is a reworked variant of Heyoka (“srvdll.dll”), a evidence-of-thought (PoC) exfiltration device “which employs spoofed DNS requests to generate a bidirectional tunnel.” The modified Heyoka backdoor is far more strong, equipped with capabilities to make, delete, and research for information, create and terminate procedures, and collect process details on a compromised host.
“Aoqin Dragon is an active cyber espionage group that has been functioning for almost a decade,” Chen said, adding, “it is likely they will also proceed to progress their tradecraft, locating new procedures of evading detection and stay extended in their focus on network.”
Observed this write-up intriguing? Stick to THN on Facebook, Twitter and LinkedIn to go through much more exceptional material we article.
Some parts of this article are sourced from:
thehackernews.com


 Apple's Mac Mini falls back to an all-time low of $570
Apple's Mac Mini falls back to an all-time low of $570