Cybersecurity researchers are calling notice to a absolutely free-to-use browser automation framework which is getting ever more utilized by menace actors as component of their attack strategies.
“The framework contains various capabilities which we assess may well be utilized in the enablement of destructive activities,” scientists from Crew Cymru said in a new report released Wednesday.
“The specialized entry bar for the framework is purposefully held minimal, which has served to develop an lively local community of content material builders and contributors, with actors in the underground financial system advertising their time for the generation of bespoke tooling.”

The U.S. cybersecurity company reported it noticed command-and-management (C2) IP addresses affiliated with malware these kinds of as Bumblebee, BlackGuard, and RedLine Stealer creating connections to the downloads subdomain of Bablosoft (“downloads.bablosoft[.]com”), the maker of the Browser Automation Studio (BAS).
Bablosoft was beforehand documented by cloud security and software supply organization F5 in February 2021, pointing to the framework’s capability to automate jobs in Google’s Chrome browser in a method similar to reputable developer instruments like Puppeteer and Selenium.
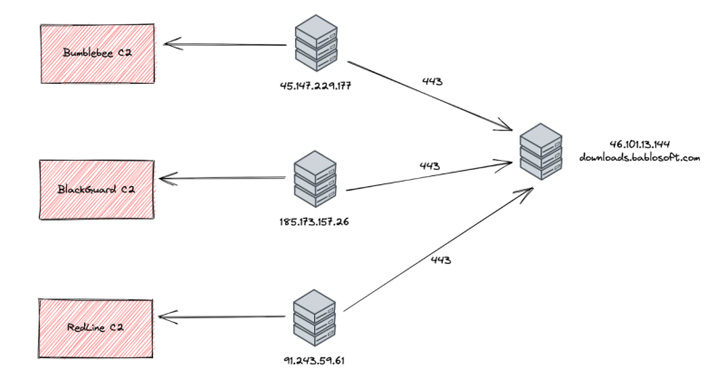
Threat telemetry for the subdomain’s IP handle — 46.101.13[.]144 — demonstrates that a wide the greater part of activity is originating from destinations in Russia and Ukraine, with open up source intelligence indicating that Bablosoft’s owner is allegedly based in the Ukrainian cash city of Kyiv.
It can be getting suspected that the operators of the malware campaigns connected to the Bablosoft subdomain for functions of downloading additional instruments for use as part of write-up-exploitation actions.
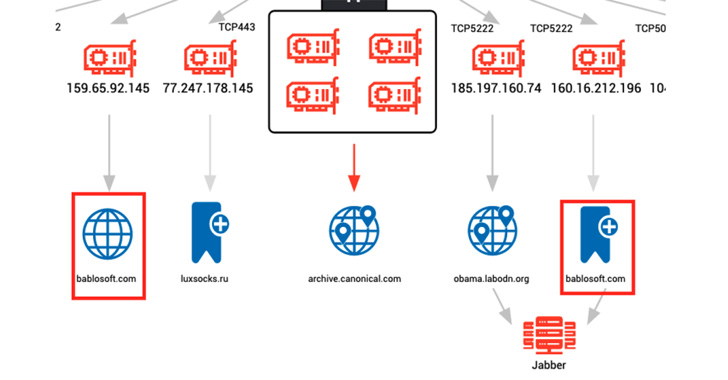
Also discovered are many hosts connected with cryptojacking malware like XMRig and Tofsee communicating with a 2nd subdomain named “fingerprints.bablosoft[.]com” to use a provider that will help the mining malware conceal its conduct.
“Primarily based on the quantity of actors now employing instruments presented on the Bablosoft web site, we can only be expecting to see BAS getting a extra common ingredient of the danger actor’s toolkit,” the researchers said.
Observed this article attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to go through far more exceptional material we submit.
Some parts of this article are sourced from:
thehackernews.com