While organizations typically go to great lengths to tackle security vulnerabilities that may perhaps exist inside of their IT infrastructure, an organization’s helpdesk may pose a bigger risk thanks to social engineering attacks.
Social engineering is “the art of manipulating people today so they give up confidential information,” according to Webroot. There are lots of diverse forms of social engineering techniques but a single is area of vulnerability is how social engineering could be utilized from a helpdesk technician to steal a user’s credentials.
The Method of Gaining Access With Social Engineering
The to start with action in these kinds of an attack is normally for the attacker to get data about the firm that they are concentrating on. The attacker may commence by employing information that is freely accessible on the Internet to figure out who inside the organization is most likely to have elevated permissions or accessibility to sensitive info. An attacker can generally get this info as a result of a straightforward Google lookup or by querying business-oriented social networks these as LinkedIn.
After an attacker identifies a person whose credentials they want to steal, they want to know the user’s login title. There are any variety of approaches that an attacker could figure out a login name. A single process might simply be to consider to authenticate into the organization’s Lively Directory environment. Some more mature Lively Listing purchasers will explain to you if you have entered a lousy username or an incorrect password.
An simpler strategy is for the attacker to question on the web databases of leaked qualifications. The attacker will not always require to track down the qualifications for the account that they are attacking. They have to have only to obtain qualifications for anyone at that firm. That will reveal the username structure that the group takes advantage of. For example, the organization may well make usernames primarily based on firstname.lastname or potentially a 1st original adopted by a last title.
With this sort of data in hand, the attacker could possibly make a phone phone to the organization’s helpdesk and ask for a password reset. The purpose behind this phone get in touch with isn’t to get the password reset, but instead to obtain out what forms of protocols the firm has in put. For case in point, the helpdesk technician could possibly check with the attacker (who is posing as a legitimate personnel) a security dilemma such as, “what is your staff ID number”. The attacker can then notify the technician that they you should not have their personnel ID quantity useful and will contact back later on when they have it in entrance of them.
At this issue, the attacker has quite a few critical pieces of data in their possession. They know the victim’s identify, the victim’s login title, and the security problem that the helpdesk technician is going question prior to granting a password reset.
Combatting Social Engineering Attack With Security Concerns
Regrettably, security questions are mostly ineffective. An professional attacker can effortlessly acquire the responses to security thoughts from any selection of distinctive sources. The Dark Web for instance, consists of overall databases of responses to prospective security thoughts and we know conclude-buyers usually divulge way far too a lot own information and facts on social media.
In addition to security thoughts, some companies have traditionally utilised caller ID information and facts as a tool for verifying a user’s identity. Having said that, this strategy is also unreliable since cloud-dependent PBX units make it straightforward for an attacker to spoof caller ID info.
The critical matter to recall is that social engineering attacks are not theoretical attack vectors, they occur in the real environment. Previously this yr, Electronic Arts was infiltrated by hackers who stole a big amount of info (which include resource code for the company’s FIFA 21 soccer activity). The hacker attained entry by tricking the company’s IT assist staff members into providing them accessibility to the company’s network.
So, if security thoughts and other common id verification mechanisms are no longer successful, how can an group protect by itself against this sort of attack?
Onus on the Helpdesk Technician
The critical to avoiding social engineering assaults towards the helpdesk is to make it unachievable for a helpdesk technician to knowingly or unknowingly support in this kind of an attack. The technician is, for all useful functions, the weak website link in the security chain.
Think about the earlier case in point in which an attacker contacts an organization’s helpdesk pretending to be an worker who needs their password reset. A number of items could conceivably happen for the duration of that dialogue. Some attainable results consist of:
- The attacker responses the security query applying stollen information and facts sourced from social media or from the Dark Web
- The attacker attempts to achieve the technician’s belief through pleasant dialogue to acquire favor with the technician. The attacker hopes that the technician will neglect the regulations and go in advance and reset the password, even in the absence of the needed security details. In some scenarios, the attacker could possibly also attempt to make the helpdesk technician experience sorry for them.
- The attacker may possibly attempt to intimidate the helpdesk technician by posing as a CEO who is extremely upset that they are unable to log in. When the helpdesk technician asks a security dilemma, the attacker may scream that they do not have time to response a bunch of stupid inquiries, and demand that the password be reset correct now (this procedure has succeeded lots of occasions in the authentic environment).
In the end, the technician’s discretion is the only point that establishes no matter whether the requested password reset is heading to come about. There is nothing in just the indigenous Energetic Directory applications that will stop a technician from being ready to reset a user’s password if the technician fails to prove the user’s identity sufficiently. As such, the Energetic Listing instruments can be believed of as one more weak url in the security chain.
The Safe Solution to Socially Engineered Cyber Attack
The best way to reduce the probability that the firm will be breached by these types of assaults is to prevent the helpdesk employees from utilizing the Energetic Listing Buyers and Computers console or equivalent tools for password resets. In its place, it is better to use a 3rd-party solution this sort of as Specops Safe Provider Desk, that will physically stop a technician from resetting a password except certain MFA necessities have been satisfied.
To see how the Secure Services Desk eradicates the risks involved with password resets, consider a condition in which a reputable consumer requests a password reset. The helpdesk technician can deliver a six-digit code to the user’s mobile unit (which has been preregistered and is acknowledged to belong to the consumer). The technician simply cannot see this code and does not know what code was sent. When the person receives the code, they must study it to the technician, who then enters the code into the Specops application.
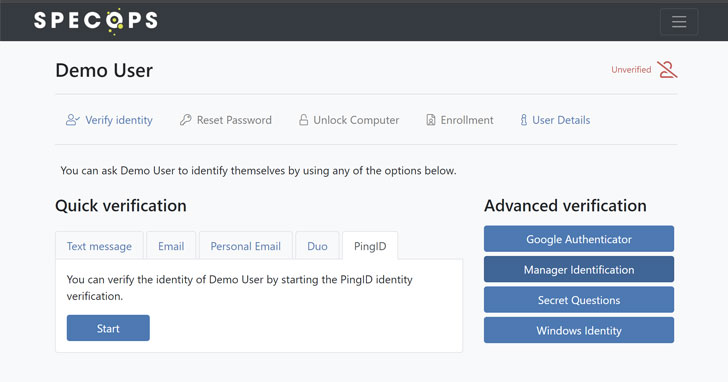 The admin see of an active helpdesk user verification applying Specops Protected Support Desk
The admin see of an active helpdesk user verification applying Specops Protected Support Desk
Only then is the technician allowed to reset the user’s password. This would make it difficult for the technician to skirt the principles and grant a password reset to anyone who has failed to fulfill the security prerequisites.
Examination out Specops Secure Assistance Desk in your Advertisement atmosphere for cost-free to see how it works.
Uncovered this posting fascinating? Stick to THN on Facebook, Twitter and LinkedIn to study far more exceptional material we put up.
Some parts of this article are sourced from:
thehackernews.com

 Ransomware Intrusion Group FIN12 Ramps-Up in Europe
Ransomware Intrusion Group FIN12 Ramps-Up in Europe