An amalgam of many condition-sponsored threat teams from China may possibly have been powering a string of focused attacks against Russian federal government authorities in 2020.
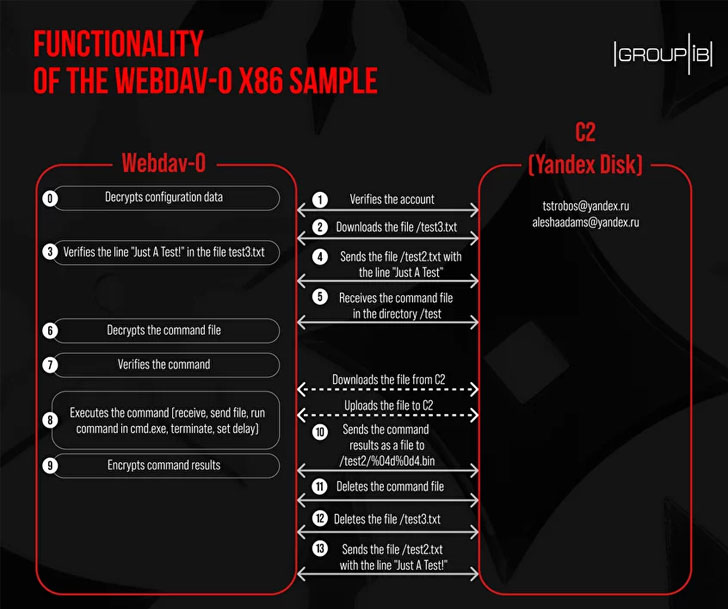
The newest investigation, revealed by Singapore-headquartered corporation Group-IB, delves into a piece of laptop virus identified as “Webdav-O” that was detected in the intrusions, with the cybersecurity agency observing similarities amongst the tool and that of well-known Trojan referred to as “BlueTraveller,” that is regarded to be linked to a Chinese menace team called TaskMasters and deployed in malicious routines with the purpose of espionage and plundering confidential documents.

“Chinese APTs are a person of the most several and aggressive hacker communities,” researchers Anastasia Tikhonova and Dmitry Kupin stated. “Hackers mainly target point out businesses, industrial facilities, military contractors, and study institutes. The key objective is espionage: attackers get accessibility to private facts and attempt to conceal their presence for as extended as doable.”
The report builds on a variety of community disclosures in May possibly from Solar JSOC and SentinelOne, both equally of which disclosed a malware identified as “Mail-O” that was also noticed in attacks against Russian federal executive authorities to accessibility the cloud services Mail.ru, with SentinelOne tying it to a variant of another properly-recognised malicious software package known as “PhantomNet” or “SManager” applied by a danger actor dubbed TA428.
“The key goal of the hackers was to fully compromise the IT infrastructure and steal confidential information, including files from closed segments and email correspondence of essential federal executive authorities,” Solar JSOC famous, including the “cybercriminals ensured them selves a superior level of secrecy by way of the use of legitimate utilities, undetectable malware, and a deep knowledge of the details of the get the job done of details defense equipment put in in govt bodies.”
Group-IB’s evaluation facilities on a Webdav-O sample that was uploaded to VirusTotal in November 2019 and the overlaps it shares with the malware sample thorough by Photo voltaic JSOC, with the scientists discovering the latter to be a newer, partly improvised model featuring included capabilities. The detected Webdav-O sample has also been connected to the BlueTraveller trojan, citing resource code similarities and the fashion in which commands are processed.

What is much more, even more investigation into TA428’s toolset has disclosed a lot of commonalities among BlueTraveller and a nascent malware strain named “Albaniiutas” that was attributed to the risk actor in December 2020, implying that not only is Albaniiutas an updated variant of BlueTraveller, but also that Webdav-O malware is a version of BlueTraveller.
“It is noteworthy that Chinese hacker teams actively exchange resources and infrastructure, but potentially it is just the scenario listed here,” the researchers explained. “This implies that one particular Trojan can be configured and modified by hackers from diverse departments with distinct ranges of teaching and with many objectives.”
“Either both Chinese hacker teams (TA428 and TaskMasters) attacked Russian federal government authorities in 2020 or that there is a person united Chinese hacker group produced up of different models.”
Uncovered this article attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to read through more exceptional material we post.
Some parts of this article are sourced from:
thehackernews.com

 The Morning After: Is this the end of the selfie camera notch?
The Morning After: Is this the end of the selfie camera notch?