Adversaries are more and more abusing Telegram as a “command-and-regulate” program to distribute malware into organizations that could then be used to capture sensitive information and facts from focused programs.
“Even when Telegram is not set up or currently being used, the procedure allows hackers to ship destructive commands and functions remotely by way of the instantaneous messaging application,” stated scientists from cybersecurity agency Test Issue, who have discovered no much less than 130 attacks over the previous three months that make use of a new multi-purposeful distant entry trojan (RAT) referred to as “ToxicEye.”

The use of Telegram for facilitating destructive routines is not new. In September 2019, an info stealer dubbed Masad Stealer was located to plunder details and cryptocurrency wallet information from contaminated personal computers utilizing Telegram as an exfiltration channel. Then previous year, Magecart teams embraced the same tactic to deliver stolen payment specifics from compromised websites again to the attackers.
The tactic also pays off in a selection of means. For a begin, Telegram is not only not blocked by business antivirus engines, the messaging app also lets attackers to continue to be nameless, given the registration procedure requires only a mobile variety, thus supplying them entry to contaminated gadgets from almost any spot throughout the planet.
The latest marketing campaign noticed by Verify Place is no diverse. Unfold by means of phishing email messages embedded with a malicious Windows executable file, ToxicEye uses Telegram to converse with the command-and-regulate (C2) server and upload information to it. The malware also sports activities a vary of exploits that makes it possible for it to steal info, transfer and delete files, terminate processes, deploy a keylogger, hijack the computer’s microphone and camera to file audio and video clip, and even encrypt information for a ransom.

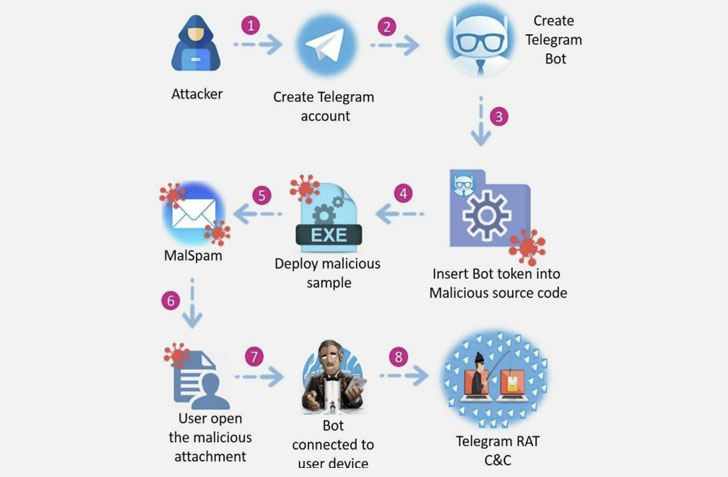
Specifically, the attack chain commences with the generation of a Telegram bot by the attacker, which is then embedded into the RAT’s configuration file, in advance of compiling it into an executable (e.g. “paypal checker by saint.exe”). This .EXE file is then injected into a decoy Term doc (“answer.doc”) that, when opened, downloads and operates the Telegram RAT (“C:UsersToxicEyerat.exe”).
“We have learned a growing craze the place malware authors are using the Telegram platform as an out-of-the-box command-and-management program for malware distribution into companies,” Look at Point R&D Team Manager Idan Sharabi stated. “We consider attackers are leveraging the reality that Telegram is made use of and permitted in almost all companies, employing this system to accomplish cyber attacks, which can bypass security restrictions.”
Found this report attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to browse more distinctive content we submit.
Some parts of this article are sourced from:
thehackernews.com


 Apple's AirTag tracks your items for $29
Apple's AirTag tracks your items for $29