Law enforcement businesses from as several as 8 international locations dismantled the infrastructure of Emotet, a infamous email-centered Windows malware driving many botnet-driven spam strategies and ransomware assaults about the past decade.
The coordinated takedown of the botnet on Tuesday — dubbed “Procedure Ladybird” — is the end result of a joint work between authorities in the Netherlands, Germany, the U.S., the U.K., France, Lithuania, Canada, and Ukraine to get handle of servers utilized to run and command the malware network.
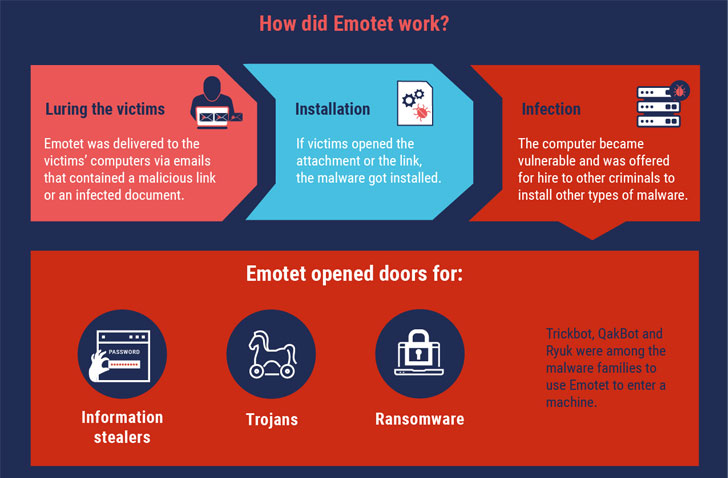
“The Emotet infrastructure effectively acted as a key door opener for laptop systems on a global scale,” Europol stated. “What manufactured Emotet so dangerous is that the malware was provided for retain the services of to other cybercriminals to set up other forms of malware, this sort of as banking Trojans or ransomware, onto a victim’s laptop.”
Far more Than a Malware
Due to the fact its very first identification in 2014, Emotet has advanced from its original roots as a credential stealer and banking Trojan to a potent “Swiss Military knife” that can serve as a downloader, information stealer, and spambot based on how it can be deployed.

Regarded for becoming consistently less than enhancement, cybercrime support updates by itself routinely to increase stealthiness, persistence, and insert new spying capabilities by means of a broad assortment of modules, together with a Wi-Fi spreader to discover and compromise fresh new victims linked to close by Wi-Fi networks.
Very last 12 months, the malware was linked to various botnet-pushed spam strategies and even able of providing far more risky payloads these as TrickBot and Ryuk ransomware by leasing its botnet of compromised devices to other malware teams.
“The Emotet group managed to get e-mail as an attack vector to a upcoming stage,” Europol said.
700 Emotet Servers Seized
The U.K.’s National Crime Agency (NCA) reported the procedure took just about two many years to map the infrastructure of Emotet, with various qualities in the Ukrainian city of Kharkiv raided to confiscate personal computer machines made use of by the hackers.
The Ukrainian Cyberpolice Department also arrested two persons allegedly involved in the botnet’s infrastructure upkeep, the two of whom are facing 12 yrs in prison if discovered guilty.
“Assessment of accounts made use of by the team at the rear of Emotet showed $10.5 million staying moved above a two-year interval on just just one Virtual Currency system,” the NCA said, incorporating “pretty much $500,000 experienced been used by the team above the exact period of time to manage its criminal infrastructure.”
Globally, Emotet-connected damages are reported to have price tag about $2.5 billion, Ukrainian authorities mentioned.
With at least 700 servers operated by Emotet throughout the planet now having been taken down from the inside, machines contaminated by the malware are now directed to this law enforcement-infrastructure, so protecting against even more exploitation.
In addition, the Dutch Nationwide Law enforcement has introduced a software to check out for prospective compromise, dependent on a dataset containing 600,000 e-mail addresses, usernames, and passwords that had been determined all through the procedure.
Emotet to Be Wiped En Masse on April 25, 2021
The Dutch police, which seized two central servers located in the nation, explained it has deployed a computer software update to neutralize the risk posed by Emotet proficiently.
“All infected computer systems will mechanically retrieve the update there, soon after which the Emotet an infection will be quarantined,” the agency claimed. In accordance to a tweet from a security researcher who goes by the Twitter handle milkream, Emotet is predicted to be wiped on April 25, 2021, at 12:00 regional time from all compromised machines.
Given the nature of the takedown procedure, it stays to be seen if Emotet can phase a comeback. If it does, it wouldn’t be the first time a botnet survived key disruption attempts.
As of writing, Abuse.ch’s Feodo Tracker reveals at least 20 Emotet servers are however online.
“A blend of each up to date cybersecurity equipment (antivirus and operating techniques) and cybersecurity recognition is necessary to steer clear of slipping sufferer to complex botnets like Emotet,” Europol cautioned.
“Buyers should very carefully check out their e-mail and prevent opening messages and in particular attachments from unknown senders. If a message appears far too excellent to be accurate, it very likely is and e-mails that implore a perception of urgency should be prevented at all expenditures.”
Observed this article intriguing? Comply with THN on Facebook, Twitter and LinkedIn to study extra exceptional articles we post.
Some parts of this article are sourced from:
thehackernews.com


 Xiaomi working on two phones supporting 67W wireless charging
Xiaomi working on two phones supporting 67W wireless charging