The U.S. Nationwide Security Company (NSA) on Friday explained DNS in excess of HTTPS (DoH) — if configured properly in company environments — can support protect against “quite a few” preliminary accessibility, command-and-control, and exfiltration techniques made use of by danger actors.
“DNS around Hypertext Transfer Protocol more than Transport Layer Security (HTTPS), normally referred to as DNS about HTTPS (DoH), encrypts DNS requests by making use of HTTPS to give privacy, integrity, and ‘last mile’ supply authentication with a client’s DNS resolver,” according to the NSA’s new advice.
Proposed in 2018, DoH is a protocol for performing distant Area Title Method resolution by means of the HTTPS protocol.
One of the main shortcomings with recent DNS lookups is that even when somebody visits a website that utilizes HTTPS, the DNS query and its response is despatched above an unencrypted link, so permitting 3rd-occasion eavesdropping on the network to keep track of each web page a consumer is traveling to.
Even worse, the set up is ripe for carrying out male-in-the-center (MiTM) attacks simply by shifting the DNS responses to redirect unsuspecting website visitors to a malware-laced web page of the adversary’s choice.
Consequently by making use of HTTPS to encrypt the facts amongst the DoH customer and the DoH-primarily based DNS resolver, DoH aims to raise user privateness and security by stopping eavesdropping and manipulation of DNS knowledge by MiTM attacks.
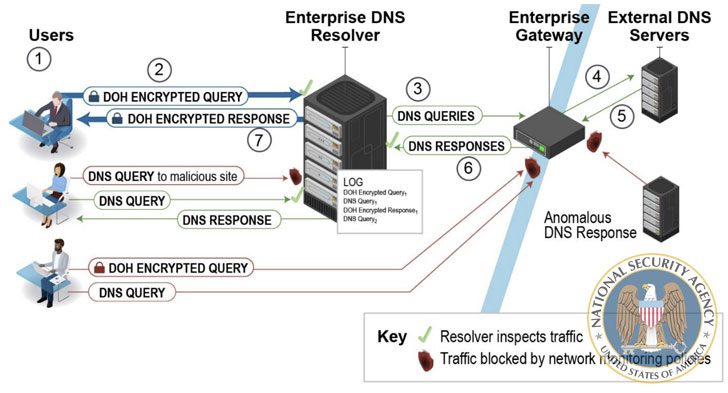
To that outcome, the NSA recommends utilizing only designated organization DNS resolvers to achieve the wished-for cybersecurity protection, when noting that such resolvers will be bypassed completely when a shopper has DoH enabled and is configured to use a DoH resolver not specified by the business.
The gateway, which is employed to ahead the question to exterior authoritative DNS servers in the party the organization DNS resolver does not have the DNS response cached, should really be created to block DNS, DoH, and DNS over TLS (DoT) requests to external resolvers and DNS servers that are not from the business resolver, the company extra.
Though DoH protects DNS transactions from unauthorized modification, the NSA cautioned of a “fake perception of security.”
“DoH does not assurance safety from cyber menace actors and their potential to see the place a client is going on the web,” it said. “DoH is particularly developed to encrypt only the DNS transaction among the consumer and resolver, not any other website traffic that comes about after the question is happy.”
“Enterprises that allow DoH devoid of a strategic and thorough tactic can conclusion up interfering with network monitoring resources, stopping them from detecting destructive risk action within the network, and allowing for cyber risk actors and malware to bypass the specified business DNS resolvers.”
What’s extra, the encryption does very little to stop the DNS service provider from seeing equally the lookup requests as effectively as the IP handle of the shopper earning them, efficiently undermining privacy protections and generating it attainable for a DNS supplier to produce detailed profiles dependent on users’ searching behavior.
Oblivious DNS-over-HTTPS (ODoH), announced past thirty day period by engineers at Apple, Cloudflare, and Fastly, aims to deal with this issue. It stops the DoH resolver from being aware of which shopper requested what domain names bypassing all requests by means of a proxy that separates the IP addresses from the queries, “so that no solitary entity can see equally at the exact time.”
Set differently, this means the proxy does not know the contents of queries and responses, and the resolver does not know the IP addresses of the shoppers.
Next, the use of DoH also would not negate the risk that resolvers that talk with destructive servers upstream could however be prone to DNS cache poisoning.
“DNSSEC should be made use of to secure the upstream responses, but the DoH resolver may possibly not validate DNSSEC,” the NSA mentioned. “Enterprises that do not know which areas of the DNS course of action are vulnerable could tumble into a false perception of security.”
Discovered this posting attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to study more special material we post.
Some parts of this article are sourced from:
thehackernews.com

 Honor V40 5G appears in hands-on video, launch postponed to January 22
Honor V40 5G appears in hands-on video, launch postponed to January 22