Researchers warn of a spike in the cryptocurrency-mining botnet considering the reality that August 2020.
Researchers are warning of a new breathtaking uptick in the exercising of the Lemon Duck cryptocurrency-mining botnet, which targets victims’ notebook assets to mine the Monero electronic foreign exchange.
Click on on to Indication-up!
Scientists inform that Lemon Duck is “one of the additional complex” mining botnets, with quite a few interesting techniques up its sleeve. Though the botnet has been energetic looking at that at minimum the quit of December 2018, researchers noticed an boost in DNS requests linked with its command-and-manage (C2) and mining servers given that the conclusion of August, in a slew of assaults centered on Asia (collectively with types focusing on Iran, Egypt, Philippines, Vietnam and India).
“Cisco Talos has established motion in our endpoint telemetry affiliated with Lemon Duck cryptocurrency mining malware, affecting a handful of exclusive firms in the authorities, retail, and technology sectors,” pointed out researchers with Cisco Talos, in Tuesday analysis. “We seen the action spanning from late March 2020 to existing.”
Much more the most up-to-date assaults have bundled much much less-documented modules that are loaded by the crucial PowerShell element – which include a Linux department and a module permitting even more distribute by sending e-mails to victims with COVID-19 lures.
Threatpost has reached out to experts for further more details about how a whole lot of victims have been distinct and the extent to which the botnet’s operators have profited off of the cryptomining assaults.
Lemon Duck
Lemon Duck has at minimum 12 unbiased infection vectors – added than most malware. These capabilities fluctuate from Server Data Block (SMB) and Remote Desktop Protocol (RDP) password brute-forcing, sending email messages with exploit attachments or concentrating on the RDP BlueKeep flaw (CVE-2019-0708) in Windows gadgets or focusing on vulnerabilities in Redis (an open up-supply, in-memory know-how composition keep used as a databases, cache and concept broker) and YARN Hadoop (a useful resource-administration and occupation-scheduling technology) in Linux gear.
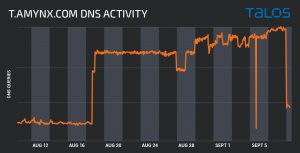
Lemon Duck botnet August exercise. Credit history: Cisco Talos
Just after the preliminary an an infection, a PowerShell loading script is downloaded, which tends to make use of the perform “bpu” to disable Windows Defender significant-time detection and established powershell.exe on the checklist of procedures excluded from scanning.
“bpu” also checks if the script is handling with administrative privileges. If it is, the payload is downloaded and run employing the Invoke-Expression cmdlet (a functionality that can be applied for getting in contact with code in just a script or setting up commands to be executed later on). If not, it leverages present plan executables to start out the upcoming phase.
“This is a top-quality starting amount for assessment and retrieval of supplemental modules,” claimed scientists. “Almost all PowerShell modules are obfuscated with four or 5 degrees of obfuscation, probably created by the Invoke-Obfuscation module. Even even though they are relatively rapid to take away, they however gradual down the examination strategy and make detection employing prevalent signatures much extra hard.”
These executable modules, which are downloaded and driven by the big module, communicates with the C2 server extra than HTTP.
Modular Functionalities
The modules include a principal loader, which checks the degree of person privileges and areas related for mining, these as the form of the easily obtainable graphic card (alongside one another with GTX, Nvidia, GeForce, AMD and Radeon). If these GPUs are not detected, the loader downloads and operates the commodity XMRig CPU-dependent mining script.
Other modules contain a most important spreading module (with what researchers say consist of “a fairly ambitious piece of code” that contains significantly far more than 10,000 traces of coding), a Python-generally centered module packaged utilizing Pyinstaller, and a killer module crafted to disable regarded competing mining botnets.
Lemon Duck also includes an email-spreading module. These unfold e-mail making use of a mix of COVID-19-similar matter strains and textual content, as very well as other emotion-pushed lures (these as an email subject subject “WTF” with the textual content material “What’s totally erroneous with you?are you out of your views!!!!!!!”). These e-mail involve an infected attachments despatched employing Outlook automation to every single call in the impacted user’s take care of reserve.
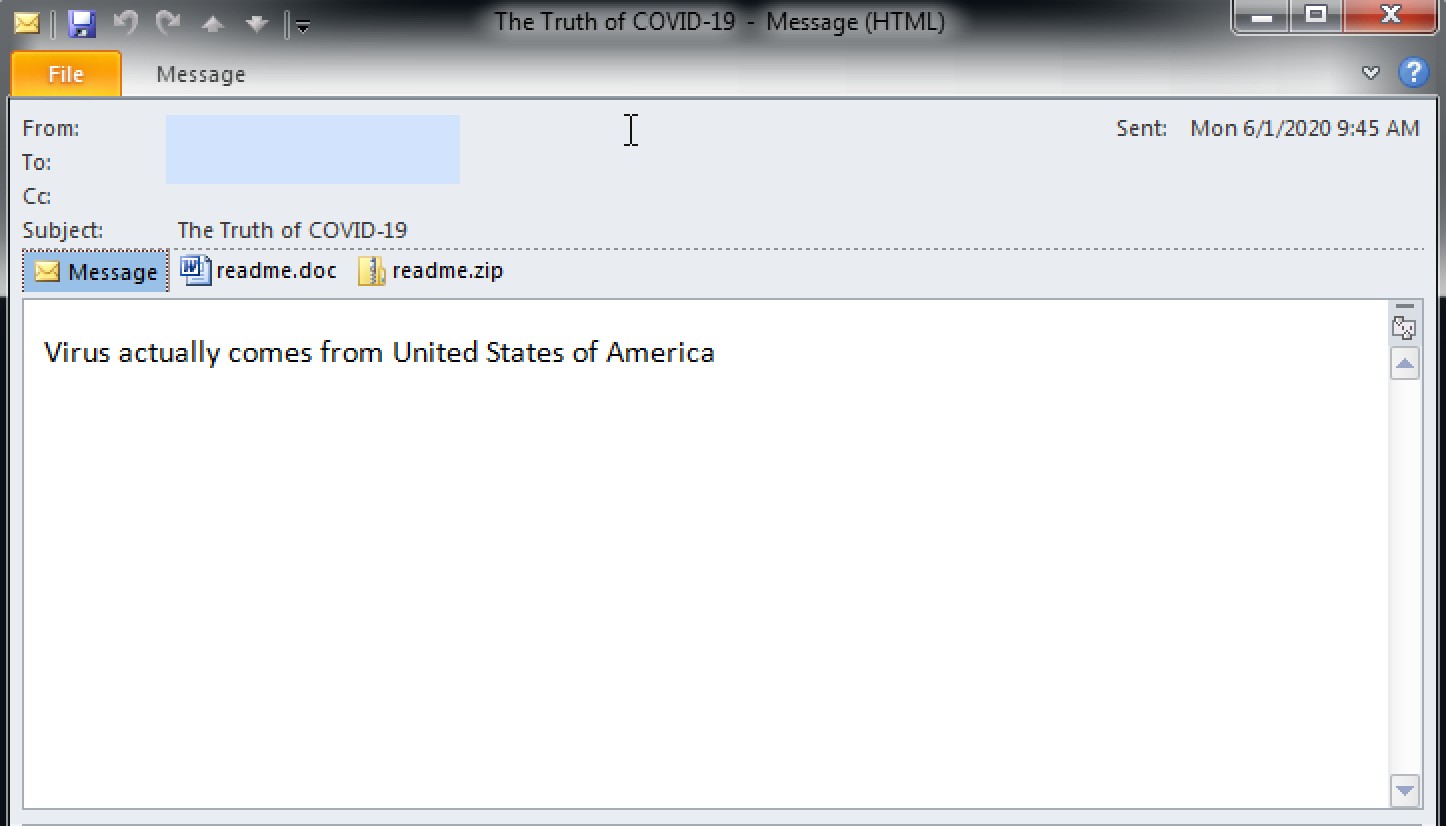
An illustration of an email despatched by the Lemon Duck module. Credit score record: Cisco Talos
Linux Section
Scientists also fall light-weight on a considerably considerably less documented Linux branch of the Lemon Duck malware. These Lemon Duck bash scripts are executed quickly following the attacker productive compromises a Linux host (by utilizing Redis, YARN or SSH). There are two principal bash scripts, talked about researchers: The to start off with collects some details about the contaminated host and helps make an try to attain a Linux variation of the XMRig miner, prior to making an attempt to delete several procedure logs. The 2nd tries to terminate and do away with competing cryptocurrency miners now latest on the software.
“The script also attempts to terminate and uninstall processes linked to Alibaba and Tencent cloud security brokers. The script would look to be shared involving rather a couple of Linux-based mostly largely cryptomining botnets,” said researchers.
Lemon Duck was earlier noticed in 2020 in a internet marketing marketing campaign concentrating on printers, intelligent TVs and automatic guided cars that depend on Windows 7. Researchers in February warned that the processor-intensive mining endeavours are getting their toll on products and triggering devices malfunctions together with exposing gear to security issues, disruption of supply chains and specifics drop.
Defenders can stomp out the risk of cryptocurrency assaults by examining technique habits to area any valuable useful resource-sucking threats.
“Cryptocurrency-mining botnets can be high priced in problems of the stolen computing cycles and electrical power use expenditures,” they stated. “While organizations will want to be centered on guarding their most effective possessions, they must truly not ignore threats that are not notably focused toward their infrastructure.”
On October 14 at 2 PM ET Get the most up-to-day facts on the soaring threats to retail e-commerce security and how to cease them. Register today for this No expense Threatpost webinar, “Retail Security: Magecart and the Boost of e-Commerce Threats.” Magecart and other threat actors are driving the soaring wave of on the web retail use and racking up important quantities of consumer victims. Find out how web web-sites can avoid finding to be the following compromise as we go into the holiday getaway getaway 12 months. Be part of us Wednesday, Oct. 14, 2-3 PM ET for this LIVE webinar.
Some aspects of this posting are sourced from:
threatpost.com


 Apple revives MagSafe with new wireless chargers and cases for iPhone
Apple revives MagSafe with new wireless chargers and cases for iPhone