A critical vulnerability uncovered in Actual-Time Automation’s (RTA) 499ES EtherNet/IP (ENIP) stack could open up up the industrial command units to remote attacks by adversaries.
RTA’s ENIP stack is 1 of the greatly applied industrial automation gadgets and is billed as the “normal for factory ground I/O programs in North The us.”
“Prosperous exploitation of this vulnerability could result in a denial-of-support affliction, and a buffer overflow may possibly enable distant code execution,” the US cybersecurity and infrastructure company (CISA) mentioned in an advisory.
As of yet, no known public exploits have been discovered to goal this vulnerability. Nevertheless, “according to public research engines for Internet-connected devices (e.g. shodan.io) there are extra than 8,000 ENIP-compatible internet-facing gadgets.”
Tracked as CVE-2020-25159, the flaw is rated 9.8 out of 10 in severity by the field-typical Prevalent Vulnerability Scoring Technique (CVSS) and impacts all versions of EtherNet/IP Adapter Resource Code Stack prior to 2.28, which was produced on November 21, 2012.
The stack overflow vulnerability was disclosed to CISA very last thirty day period by Sharon Brizinov, a security researcher for operational technology security organization Claroty.
Even though it appears that RTA taken off the attackable code from its program as early as 2012, it is suspected that several vendors may have bought vulnerable versions of this stack prior to the 2012 update and built-in it into their individual firmware, thereby placing a number of equipment at risk.
“Eleven gadgets had been discovered to be jogging RTA’s ENIP stack in solutions from six special suppliers,” the researchers reported.
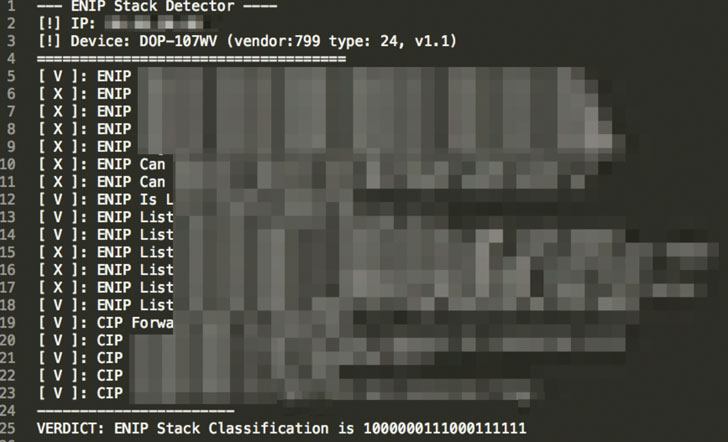
The flaw in alone problems an improper examine in the route parsing system employed in Frequent Industrial Protocol (CIP) — a interaction protocol used for arranging and sharing knowledge in industrial gadgets — enabling an attacker to open a CIP request with a significant link route size (greater than 32) and cause the parser to write to a memory tackle outside the preset-duration buffer, consequently leading to the potential execution of arbitrary code.
“The more mature code in the RTA system attempted to cut down RAM usage by restricting the measurement of a unique buffer made use of in an EtherNet/IP Ahead Open up request,” RTA claimed in its disclosure. “By restricting the RAM, it made it possible for an attacker to try to overrun the buffer and use that to try out to get management of the product.”
Claroty scientists scanned 290 various ENIP-suitable modules, of which 11 devices from 6 different sellers ended up uncovered to be using RTA’s ENIP stack. There are at the moment more than 8,000 ENIP-appropriate internet-struggling with units, in accordance to a search on Shodan.
“Likewise to preceding disclosures, these kinds of as Ripple20 or Urgent/11, this is a different scenario of a vulnerable 3rd-occasion main library putting goods from [Industrial Control System] vendors at risk,” Brizinov observed in an assessment.
It can be suggested that operators update to present variations of the ENIP stack to mitigate the flaw. CISA also suggested consumers to decrease network exposure for all control method units and be certain that they are not obtainable from the Internet.
“Identify regulate method networks and remote products powering firewalls, and isolate them from the enterprise network,” CISA explained in its inform. “When distant access is needed, use safe strategies, these kinds of as Digital Non-public Networks (VPNs), recognizing that VPNs may have vulnerabilities and need to be updated to the most present-day edition readily available.”
Observed this article interesting? Observe THN on Fb, Twitter and LinkedIn to read a lot more special content material we post.
Some parts of this article are sourced from:
thehackernews.com


 #ISC2Congress: Building a Resilient Cybersecurity Industry from #COVID19
#ISC2Congress: Building a Resilient Cybersecurity Industry from #COVID19