A team of teachers from the College of California and Tsinghua University has uncovered a sequence of critical security flaws that could guide to a revival of DNS cache poisoning attacks.
Dubbed “Unhappy DNS attack” (shorter for Aspect-channel AttackeD DNS), the approach would make it achievable for a destructive actor to have out an off-path attack, rerouting any site visitors initially destined to a particular domain to a server below their manage, thereby letting them to eavesdrop and tamper with the communications.
“This represents an important milestone — the initially weaponizable network facet channel attack that has significant security impacts,” the researchers explained. “The attack permits an off-path attacker to inject a malicious DNS file into a DNS cache.”
Tracked as CVE-2020-25705, the findings have been introduced at the ACM Conference on Computer system, and Communications Security (CCS ’20) held this week.
The flaw has an effect on operating units Linux 3.18-5.10, Windows Server 2019 (model 1809) and more recent, macOS 10.15 and more recent, and FreeBSD 12.1. and newer.
DNS Forwarders Grow to be New Attack Surface area
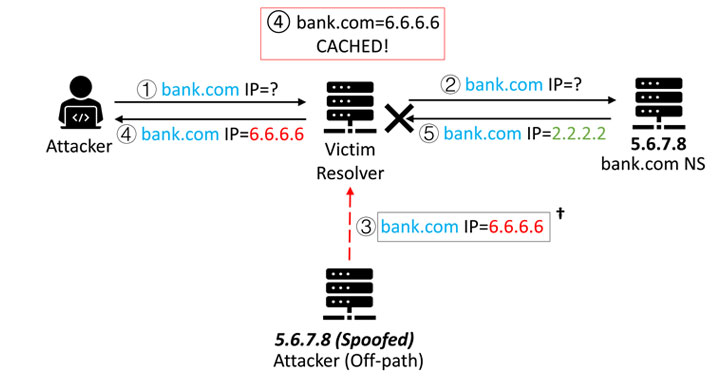
DNS resolvers normally cache responses to IP handle queries for a unique interval as a means to strengthen response overall performance in a network. But this incredibly mechanism can be exploited to poison the caches by impersonating the IP address DNS entries for a given site and redirect customers making an attempt to go to that web page to one more site of the attacker’s selection.
Even so, the performance of this sort of attacks has taken a hit in element due to protocols such as DNSSEC (Area Title Method Security Extensions) that makes a protected area title system by including cryptographic signatures to current DNS data and randomization-dependent defenses that allow for the DNS resolver to use a distinctive supply port and transaction ID (TxID) for every question.
Noting that the two mitigation measures are even now significantly from currently being greatly deployed owing to “incentives and compatibility” factors, the researchers said they devised a aspect-channel attack that can be effectively made use of from the most well known DNS software stacks, consequently rendering community DNS resolvers like Cloudflare’s 1.1.1.1 and Google’s 8.8.8.8 susceptible.
A Novel Side-Channel Attack
The Unhappy DNS attack will work by building use of a compromised equipment in any network that’s capable of triggering a ask for out of a DNS forwarder or resolver, these kinds of as a general public wireless network managed by a wireless router in a espresso shop, a purchasing mall, or an airport.
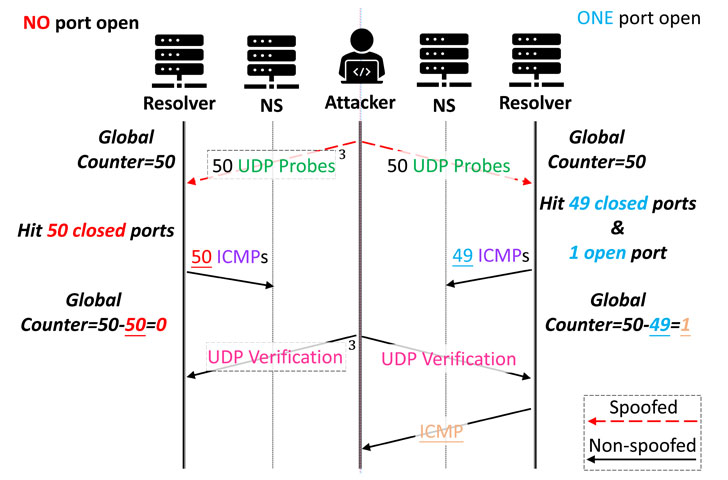
It then leverages a facet channel in the network protocol stack to scan and explore which source ports are employed to initiate a DNS query and subsequently inject a massive selection of spoofed DNS replies by brute-forcing the TxIDs.
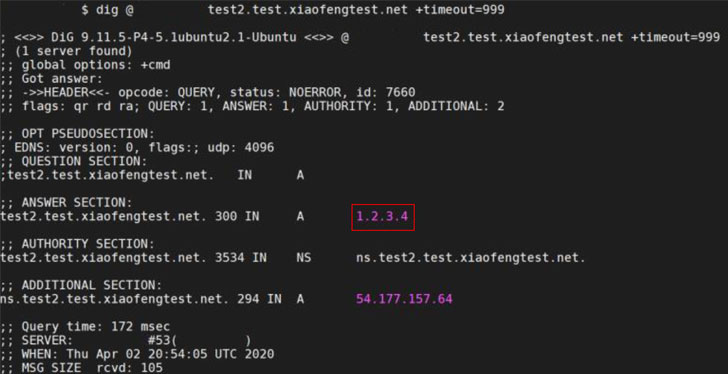
Additional especially, the researchers employed a channel utilised in the domain title requests to slim down the precise source port amount by sending spoofed UDP packets, every with diverse IP addresses, to a victim server and infer whether the spoofed probes have strike the correct resource port based mostly on the ICMP responses obtained (or deficiency thereof).
This port scan process achieves a scanning velocity of 1,000 ports per second, cumulatively getting a minor above 60 seconds to enumerate the total port array consisting of 65536 ports. With the supply port as a result derandomized, all an attacker has to do is to insert a destructive IP address to redirect web site targeted visitors and successfully pull off a DNS cache poisoning attack.
Mitigating Unhappy DNS Assaults
Apart from demonstrating strategies to extend the attack window that permits an attacker to scan more ports and also inject extra rogue documents to poison the DNS cache, the analyze found that around 34% of the open up resolvers on the Internet are susceptible, 85% of which comprise of common DNS expert services like Google and Cloudflare.
To counter Unhappy DNS, the scientists endorse disabling outgoing ICMP responses and location the timeout of DNS queries additional aggressively.
The scientists have also put jointly a device to look at for DNS servers that are susceptible to this attack. In addition, the group labored with the Linux kernel security team for a patch that randomizes the ICMP worldwide amount limit to introduce noises to the facet channel.
The study “offers a novel and general aspect channel dependent on [the] worldwide ICMP fee restrict, universally executed by all modern working systems,” the scientists concluded. “This enables successful scans of UDP supply ports in DNS queries. Blended with strategies to lengthen the attack window, it qualified prospects to a effective revival of the DNS cache poisoning attack.”
Observed this article attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to read far more unique content material we article.
Some parts of this article are sourced from:
thehackernews.com

 Honor to launch a new midranger with 66W fast charging, looks suspiciously familiar
Honor to launch a new midranger with 66W fast charging, looks suspiciously familiar