Slapdash set up of Trump site collecting reviews of Maricopa County in-particular person vote irregularities exposed 163,000 voter info information to fraud, through SQL injection.
A security flaw on a internet site established up to acquire evidence of in-human being voter fraud in Arizona would have opened the door for SQL injection and other attacks.
The bug, uncovered on a web site set up by Trump marketing campaign known as dontpressthegreenbutton.com, was uncovered by cybersecurity pro Todd Rossin, virtually by accident.
The researcher noticed a news tale about alleged voter fraud in Maricopa County, which is dwelling to Phoenix, Scottsdale and the most important bulk of Arizona’s populace. The write-up explained that the Trump campaign has filed a lawsuit alleging that voters ended up tricked by poll employees into submitting ballots with mistakes, overriding the process by urgent a inexperienced button. The information post joined to the web site affiliated with the match, dontpressthegreenbutton.com, which mentioned it is collecting lawful, sworn declarations of these fraud to be employed as proof.
Rossin clicked on the internet site and started off poking close to.
“I went to the Green Button web-site and designed up a title, and [then] saw all these other voters’ names and addresses pop up,” Rossin told Threapost. “I wasn’t seeking for it but was amazed to see it.”
Rossin shared his findings on Reddit below his username BattyBoomDaddy, and the write-up promptly received traction, racking up practically 250 reviews and more than 7,600 upvotes so much.
“Someone…ran a script to exam out how straightforward it would be to pull the info and transform the parameters to start off with the letter ‘A’ and to prevent at the first 5,000 entries – and bam, the initial 5,000 names and addresses,” Rossin discussed. “Someone else applied a SQL injection to pull names, addresses, dates-of-start (DOBs) and previous four of Social Security figures.”
Lots of voter info is general public in Arizona – but Social Security numbers and dates of birth are intended to be retained confidential.
API and SQL Injection
Rossin advised Threatpost that he, along with other people, documented the breach to the Maricopa County Elections Department.
“This is a fantastic illustration of ‘rushing to market’ as it is very clear that this internet site was rushed with small to no thought given to security,” Ray Kelly, principal security engineer at WhiteHat Security, explained to Threatpost. “For instance, a very simple automatic security scan would undoubtedly have uncovered the SQL-injection vulnerability in minutes and prevented the delicate information from getting pulled from their databases.”
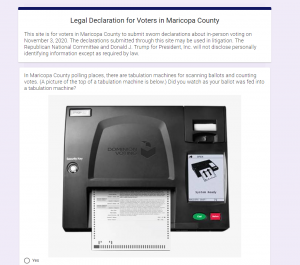
The Environmentally friendly Button internet site.
Infosec expert Richey Ward noticed Rossin’s publish and determined to do a little digging of his own. Ward shared his results on Twitter, where he described that he was able to obtain full names and addresses of 163,000 voters, tagging the Maricopa County Elections Section. Even though this information and facts is created publicly obtainable to strategies, Arizona regulation prohibits it from becoming shared by using he web.
“Tracing this to a Algolia API contact is trivial together with API keys,” Ward wrote. “This makes it possible for any individual with the keys to question the info exterior the web page.”
Just hrs later, Ward observed that the API was taken down and no for a longer period available.
“I was delighted that people today recognized it was a large deal,” Rossin additional. “I also looked up Ariz. legislation on it and the law exclusively claims that the data is not to be distributed and specially suggests not on the internet.”
And though the evident security vulnerabilities related with the Eco-friendly Button site have been resolved, Rossin, explained the web page is nevertheless far from safe.
“Yes, they pulled the API down,” Rossin advised Threatpost. “It nevertheless has incredibly lax security.”
Turned down Voter Lawsuit
Threatpost hasn’t been thriving in a number of tries to speak to the attorney at the rear of the Inexperienced Button lawsuit, Alexander Kolodin or his organization, Kolodin Law group.
The security issue will come to light-weight amid assaults focusing on voters and voter knowledge. Just a month back, in the guide up to the election, voters ended up victimized by a phishing lure making an attempt to influence them to give up their facts. And election cybersecurity far more normally is a crucial stage of emphasis for campaigns and regulation-enforcement officials. It’s up to campaigns to make sure their keeping their eye on security in all phases of their outreach.
“Looking at the evidence so far, it does in fact look like an issue for voter details exposure,” Brandon Hoffman, CISO at Netenrich, explained about the web site. “These political strategies, in their haste, are carrying out much more hurt to people today than the excellent they can hope to produce. Even though every person understands the wish and need for transparency and a fair result for all, they also have the utmost duty to voter to continue to keep our info protected if they plan to use it.”
Regardless of the documented security vulnerabilities, the dontouchthegreenbutton.com web-site assures readers, “The Republican Countrywide Committee and Donald J. Trump for President, Inc. will not disclose personally determining details apart from as necessary by law.”
Netenrich extra although this breach is related with the Trump campaign, neither political bash is correctly defending voter data. In September, the official application of the Joe Biden campaign was identified to have a privacy issue.
The Vote Joe app allows buyers to share details about on their own and their contacts with a voter database run by Focus on Wise. The App Analyst mentioned at the time that “an issue happens when the contact in the phone does not correspond with the voter, but the data continues to enrich the voter database entry. By adding faux contacts to the unit, a user is capable to sync these with actual voters.”
“Both strategies have now supplied exposures of info for voters with no clear ramifications,” Netenrich explained. “If a lay particular person set up a web site leaking Social Security quantities and addresses of persons, they would likely be in jail and below litigation. The businesses and strategies that are making use of individually identifiable information and facts of Us citizens ought to choose the time and diligence to shield that facts.”
Hackers Put Bullseye on Healthcare: On Nov. 18 at 2 p.m. EDT find out why hospitals are obtaining hammered by ransomware assaults in 2020. Save your location for this Free of charge webinar on healthcare cybersecurity priorities and listen to from leading security voices on how info security, ransomware and patching want to be a precedence for each and every sector, and why. Be a part of us Wed., Nov. 18, 2-3 p.m. EDT for this LIVE, limited-engagement webinar.
Some parts of this article are sourced from:
threatpost.com

 Cyberattack on UVM Health Network Impedes Chemotherapy Appointments
Cyberattack on UVM Health Network Impedes Chemotherapy Appointments