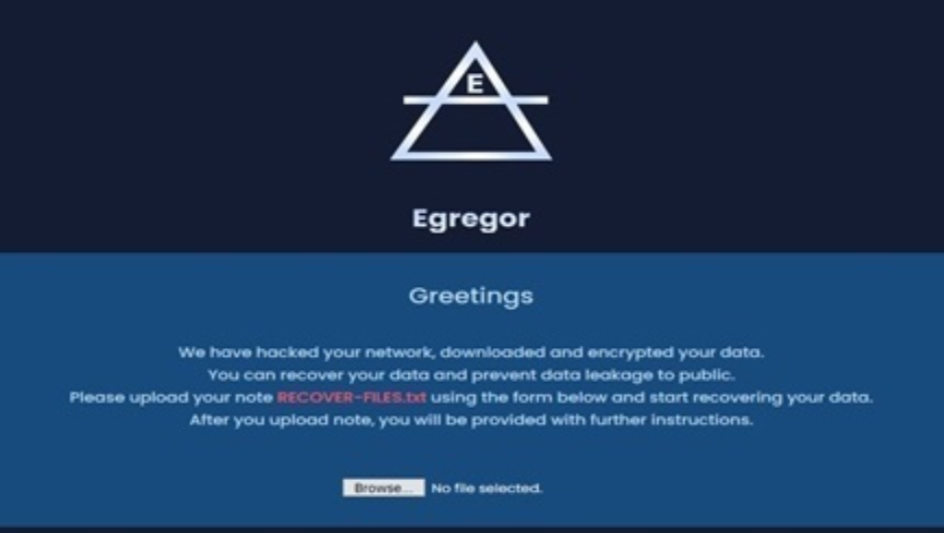
The Indian Computer Unexpected emergency Response Workforce (CERT-In) is alerting organisations to be thorough about a new ransomware referred to as Egregor. As for each CERT-In, the Egregor ransomware breaks into organisations IT systems, steals delicate data, and operates the malware to encrypt their information and threatens “Mass-Media” release of corporate information if ransom is not compensated in owing time.
“It works by using double extortion ways generally made use of by NetWalker ransomware families. First Infection vector and propagation system is continue to unidentified, it is anticipated that Egregor ransomware may perhaps infiltrate by way of spam email attachments or maliciously crafted hyperlink shared via email/immediate messaging chats,” it stated.
The ransomware employs quite a few kinds of anti-evaluation procedures, such as code obfuscation and packed payloads, which signifies the malicious code “unpacks” by itself in memory as a way to steer clear of detection by security equipment, it added.
Also, it will not exhibit its functionalities whilst analysing it right up until the specific exact command line that the attackers made use of to run the ransomware. This makes it challenging for analysts to analyse samples manually or in a sandbox surroundings. “It appends a string or random figures as the new extension of each encrypted file and creates the “Get well-Information.txt” text file/ransom observe in all folders that contain encrypted documents,” alerted CERT-In.
CERT-In is recommending typical protocols that utilize to safeguard in opposition to most ransomware out there. This features setting up Area-based mostly Information Authentication, Reporting, and Conformance (DMARC), DomainKeys Determined Mail (DKIM) and Sender Policy Framework (SPF) for your domain and other widespread security protocols.
Some parts of this article are sourced from:
gadgetsnow.com

 DJI's Mavic Mini 2 brings 4K video, RAW photos and double the range
DJI's Mavic Mini 2 brings 4K video, RAW photos and double the range