The recently found malware makes use of GitHub and Pastebin to house element code, and harbors 12 various first attack vectors.
Scientists have uncovered a new worm targeting Linux based x86 servers, as properly as Linux internet of things (IoT) equipment (that are based on ARM and MIPS CPUs).
Of take note, the malware utilizes GitHub and Pastebin for housing destructive element code, and has at minimum 12 distinctive attack modules offered – main scientists to connect with it “Gitpaste-12.” It was to start with detected by Juniper Threat Labs in assaults on Oct. 15, 2020.
“No malware is good to have, but worms are especially aggravating,” said scientists with Juniper Menace Labs in a Thursday publish. “Their capacity to distribute in an automatic style can lead to lateral distribute in just an group or to your hosts making an attempt to infect other networks throughout the internet, resulting in poor reputation for your firm.”

The initially phase of the attack is the first system compromise. The malware’s several attack modules incorporate 11 previously-disclosed vulnerabilities. That consists of flaws in Apache Struts (CVE-2017-5638), Asus routers (CVE-2013-5948), Webadmin plugin for opendreambox (CVE-2017-14135) and Tenda routers (CVE-2020-10987).
The malware will attempt to use recognised exploits for these flaws to compromise devices and may possibly also try to brute pressure passwords, said researchers. Immediately after compromising a method, a primary shell script is then uploaded to the sufferer device, and commences to down load and execute other components of Gitpaste-12.
The Malware
This script sets up a cron position it downloads from Pastebin. A cron job is a time-dependent position scheduler in Unix-like computer system running devices. The cron task calls a script and executes it once more just about every minute researchers consider that this script is presumably just one system by which updates can be pushed to the botnet.
It then downloads a script from GitHub (https://uncooked[.]githubusercontent[.]com/cnmnmsl-001/-/master/shadu1) and executes it. The script includes reviews in the Chinese language and has multiple commands accessible to attackers to disable various security capabilities. These incorporate stripping the system’s defenses, which include firewall principles, selinux (a security architecture for LinuxR programs), apparmor (a Linux kernel security module that lets the process administrator to restrict programs’ capabilities), as effectively as frequent attack avoidance and monitoring software.
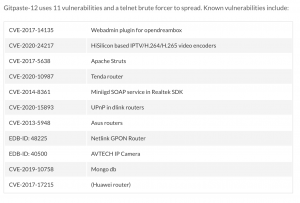
The 11 vulnerabilities utilized for Gitpaste-12’s initial attack vectors. Credit score: Juniper Labs
The malware also has some instructions that disable cloud security brokers, “which obviously signifies the danger actor intends to target public cloud computing infrastructure delivered by Alibaba Cloud and Tencent,” explained researchers.
Gitpaste-12 also attributes instructions allowing for it to run a cryptominer that targets the Monero cryptocurrency.
“It also helps prevent administrators from accumulating information and facts about operating processes by intercepting ‘readdir’ procedure phone calls and skip directories for procedures like tcpdump, sudo, openssl, etcetera. in ‘/proc’,” claimed researchers. “The ‘/proc’ directory in Linux incorporates information about jogging procedures. It is utilized, for example, by the ‘ps’ command to exhibit info about functioning procedures. But sad to say for this threat actor, this implementation does not do what they hope it to do.”
Eventually, the malware also has a library (cover.so) that is loaded as LD_PRELOAD, which downloads and executes Pastebin files )https://pastebin[.]com/uncooked/Tg5FQHhf) that host further more malicious code.
Researchers claimed they noted the Pastebin URL, as perfectly as the Git repo outlined higher than that downloads malicious scripts for the malware. The Git repo was closed on Oct. 30, 2020. “This need to cease the proliferation of this botnet,” stated researchers.
Wormable Characteristics
In phrases of its worming capabilities, Gitpaste-12 also has a script that launches attacks versus other equipment, in an try to replicate and unfold the malware.
“The malware chooses a random /8 CIDR for attack and will consider all addresses within just that selection,” according to scientists. Classless Inter-Domain Routing (CIDR) is a approach for allocating IP addresses and for IP routing – that means that the attack targets all IP addresses in the random CIDR’s range.
Another model of the script also opens ports 30004 and 30005 for reverse shell commands, claimed researchers. Port 30004 works by using the Transmission Handle Protocol (TCP), which is a single of the main protocols in TCP/IP networks while port 30005 is a bidirectional Soap/HTTP-based protocol, which supplies conversation in between equipment like routers or network switches, and auto-configuration servers.
Worms can have a widespread effects, as witnessed in a 2019 campaign that exploited a vulnerability in the Exim mail transportation agent (MTA) to achieve distant command-execution on victims’ Linux techniques, applying a wormable exploit. Researchers claimed that now additional than 3.5 million servers have been at risk from the attacks.
Various new worms have popped up in 2020 so considerably, together with the Golang worm, which is aimed at installing cryptominers, and a short while ago modified up its methods to insert assaults on Windows servers and a new pool of exploits to its bag of tips.
In August, a cryptomining worm from the team identified as TeamTNT was uncovered spreading by the Amazon Web Products and services (AWS) cloud and gathering qualifications. The moment the logins are harvested, the malware logs in and deploys the XMRig mining software to mine Monero cryptocurrency.
Hackers Place Bullseye on Health care: On Nov. 18 at 2 p.m. EDT find out why hospitals are getting hammered by ransomware attacks in 2020. Save your place for this No cost webinar on healthcare cybersecurity priorities and hear from leading security voices on how data security, ransomware and patching want to be a priority for each and every sector, and why. Be a part of us Wed., Nov. 18, 2-3 p.m. EDT for this LIVE, confined-engagement webinar.
Some parts of this article are sourced from:
threatpost.com


