Apple on Thursday introduced multiple security updates to patch three zero-working day vulnerabilities that have been discovered as remaining actively exploited in the wild.
Rolled out as portion of its iOS, iPadOS, macOS, and watchOS updates, the flaws reside in the FontParser element and the kernel, enabling adversaries to remotely execute arbitrary code and operate destructive plans with kernel-level privileges.
The zero-times had been uncovered and claimed to Apple by Google’s Challenge Zero security team.
“Apple is informed of experiences that an exploit for this issue exists in the wild,” the iPhone maker said of the 3 zero-days with out providing any added particulars so as to permit a extensive the vast majority of buyers to install the updates.
The list of impacted products features iPhone 5s and later, iPod touch 6th and 7th era, iPad Air, iPad mini 2 and later, and Apple Enjoy Collection 1 and later on.
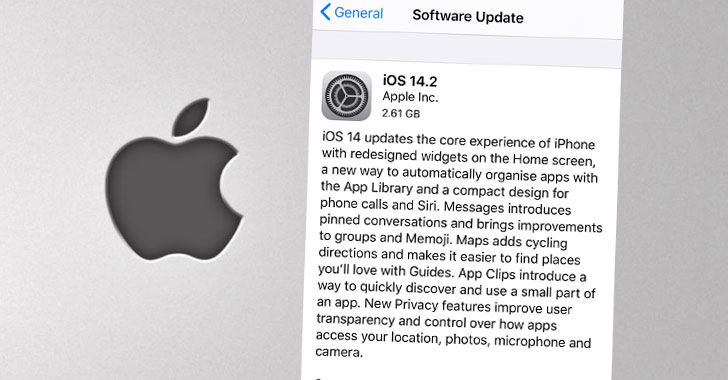
The fixes are obtainable in variations iOS 12.4.9 and 14.2, iPadOS 14.2, watchOS 5.3.9, 6.2.9, and 7.1, and as a supplemental update for macOS Catalina 10.15.7.
According to Apple’s security bulletin, the flaws are:
- CVE-2020-27930: A memory corruption issue in the FontParser library that permits for distant code execution when processing a maliciously crafted font.
- CVE-2020-27932: A memory initialization issue that lets a malicious application to execute arbitrary code with kernel privileges.
- CVE-2020-27950: A sort-confusion issue that would make it possible for a destructive software to disclose kernel memory.
“Targeted exploitation in the wild comparable to the other not long ago noted 0days,” said Shane Huntley, Director of Google’s Menace Examination Team. “Not relevant to any election focusing on.”
The disclosure is the most recent in the string of zero-days Undertaking Zero has noted considering that October 20. To start with came the Chrome zero-day in Freetype font rendering library (CVE-2020-15999), then a Windows zero-working day (CVE-2020-17087), followed by two far more in Chrome and its Android variant (CVE-2020-16009 and CVE-2020-16010).
A patch for the Windows zero-working day is expected to be introduced on November 10 as part of this month’s Patch Tuesday.
Whilst far more specifics are awaited on irrespective of whether the zero-times ended up abused by the similar threat actor, it truly is advisable that buyers update their devices to the hottest variations to mitigate the risk associated with the flaws.
Identified this post fascinating? Observe THN on Facebook, Twitter and LinkedIn to examine a lot more exceptional material we article.
Some parts of this article are sourced from:
thehackernews.com

 The PS5 will only be sold online on launch day
The PS5 will only be sold online on launch day