A cyberespionage campaign aimed at aerospace and defense sectors in purchase to set up knowledge gathering implants on victims’ equipment for reasons of surveillance and information exfiltration may well have been far more advanced than beforehand considered.
The assaults, which specific IP-addresses belonging to internet service companies (ISPs) in Australia, Israel, Russia, and protection contractors dependent in Russia and India, involved a earlier undiscovered spyware instrument known as Torisma stealthily check its victims for continued exploitation.
Tracked beneath the codename of “Operation North Star” by McAfee scientists, preliminary findings into the campaign in July exposed the use of social media web-sites, spear-phishing, and weaponized documents with pretend occupation features to trick staff performing in the protection sector to achieve a foothold on their organizations’ networks.
The attacks have been attributed to infrastructure and TTPs (Procedures, Tactics, and Processes) formerly connected with Concealed Cobra — an umbrella expression made use of by the US authorities to describe all North Korean condition-sponsored hacking teams.
The advancement carries on the craze of North Korea, a seriously sanctioned place, leveraging its arsenal of danger actors to assistance and fund its nuclear weapons method by perpetrating destructive assaults on US protection and aerospace contractors.
Though the original analysis recommended the implants had been supposed to assemble basic sufferer information and facts so as to evaluate their value, the newest investigation into Operation North Star reveals a “diploma of technological innovation” built to continue to be concealed on compromised techniques.
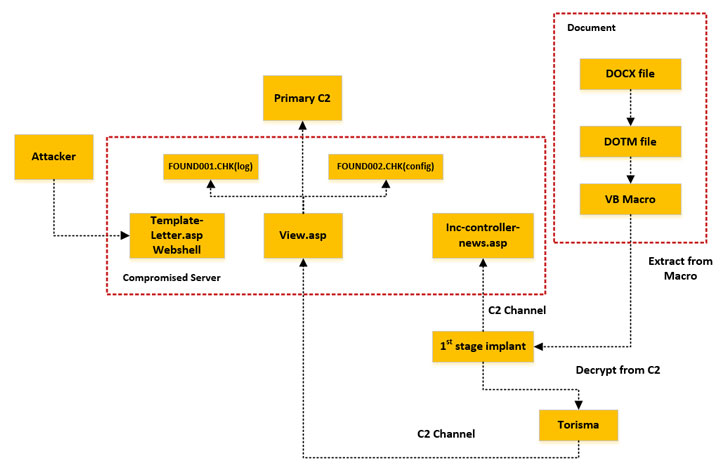
Not only did the campaign use genuine occupation recruitment material from preferred US protection contractor websites to lure specific victims into opening destructive spear-phishing email attachments, the attackers compromised and applied genuine web-sites in the US and Italy — an auction house, a printing firm, and an IT training company — to host their command-and-manage (C2) capabilities.
“Utilizing these domains to conduct C2 functions possible allowed them to bypass some organizations’ security actions for the reason that most companies do not block trustworthy websites,” McAfee scientists Christiaan Beek and Ryan Sherstibitoff reported.
What is actually much more, the very first-phase implant embedded in the Word documents would go on to evaluate the sufferer process facts (date, IP Deal with, Consumer-Agent, etc.) by cross-checking with a predetermined listing of concentrate on IP addresses to put in a 2nd implant referred to as Torisma, all the though reducing the risk of detection and discovery.
This specialized checking implant is made use of to execute customized shellcode, in addition to actively monitoring for new drives additional to the process as very well as remote desktop connections.
“This campaign was fascinating in that there was a individual listing of targets of desire, and that checklist was confirmed before the decision was made to mail a second implant, either 32 or 64 bits, for even more and in-depth checking,” the researchers said.
“Progress of the implants sent by the C2 was monitored and prepared in a log file that gave the adversary an overview of which victims were successfully infiltrated and could be monitored even more.”
Located this post exciting? Abide by THN on Facebook, Twitter and LinkedIn to read through a lot more distinctive material we put up.
Some parts of this article are sourced from:
thehackernews.com


 US Seizes More IRGC Domains
US Seizes More IRGC Domains