JM Bullion fell victim to a payment-card skimmer, which was in location for five months.
A well-liked valuable-metals dealer, JM Bullion, has been the victim of a payment-skimmer attack. The company’s response was less than good gold — it took months to notify its end users of the breach.
The Dallas-primarily based company sells gold, platinum, silver, copper and palladium bullion, in the variety of bars, coins and pure metallic coins called rounds. As aspect of its business model JM Bullion explains it “enables traders to order bullion they physically maintain, as opposed to merely proudly owning on paper.”
In a notice despatched to its on the internet buyers, the enterprise mentioned that it grew to become conscious of suspicious activity on its website on July 6. An investigation uncovered third-occasion, malicious code existing on the web-site, which “had the means to capture purchaser facts entered into the internet site in minimal scenarios while making a invest in,” in accordance to an email, shared on Reddit on Sunday.
The company statements on its web page that it employs 256-little bit SSL encryption, licensed by DigiCert/Norton. On top of that, “We in no way have accessibility to your credit score/debit card facts, as it is processed securely by CyberSource, the dad or mum enterprise of Authorize.net, adhering to the most stringent PCI-compliant standards.”
Having said that, payment-card skimmers, which are code-injections into vulnerable site components, only record regardless of what shoppers enter into the fields on checkout webpages, creating the encryption and other protections a moot level.
So, the cyberattackers were being able to seize name, tackle and payment-card specifics, JM Bullion verified.
It also reported that the skimmer was active for 5 months, from February 18 right until its forensics crew was able to eliminate it on July 17. The Reddit member reported that the recognize went out on Halloween, which means that the corporation waited three and a half months to warn users of the issue. The dates also demonstrate that there ended up 11 days that the skimmer was active immediately after the organization grew to become mindful of suspicious action on the site.
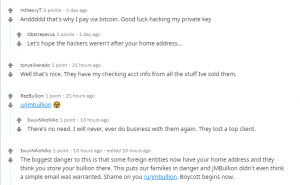
Shoppers took to Reddit to complain. Click to enlarge.
It’s unclear how numerous clients are affected. The business stated that the skimmer was in action in a “small portion” of transactions. In accordance to its site, it ships more than 30,000 orders for every month.
When arrived at by phone, a shopper provider man or woman informed Threatpost that only people affected gained the email notices.
JM Bullion didn’t promptly respond to a ask for for additional information on the breach.
There’s no word on who could be behind the attack, but payment skimmers are at the heart of ongoing Magecart attacks. Magecart is an umbrella term encompassing quite a few unique threat groups who all use the exact modus operandi: They compromise web-sites (largely created on the Magento e-commerce system) in order to inject card-skimming scripts on checkout webpages, employing exploits for unpatched vulnerabilities.
“Magecart attacks are notoriously challenging to detect simply because they goal the client-aspect of websites,” Ameet Naik, security evangelist at PerimeterX, explained to Threatpost, noting that taking five months to recognize the skimmer is not unusual. “Hackers inject malicious shadow code into the internet site scripts which runs on the users’ browsers. Common server-facet checking and security options really do not have visibility into this client-facet exercise and are unable to stop this kind of electronic skimming assaults that lead to the theft of own data from site people. This not only hurts the online business, but also exposes them to compliance penalties and legal responsibility.”
Getting benefit of unpatched and out-of-date web sites, Magecart carries on to be energetic. In Oct, a Magecart spinoff group named Fullz House compromised Increase! Mobile’s U.S. internet site and made off with a raft of personal identification.
Hackers Place Bullseye on Healthcare: On Nov. 18 at 2 p.m. EDT find out why hospitals are acquiring hammered by ransomware attacks in 2020. Save your location for this No cost webinar on healthcare cybersecurity priorities and listen to from leading security voices on how knowledge security, ransomware and patching will need to be a precedence for each sector, and why. Be part of us Wed., Nov. 18, 2-3 p.m. EDT for this LIVE, constrained-engagement webinar.
Some parts of this article are sourced from:
threatpost.com


 Pick up a 2TB Samsung T7 portable SSD for only $250
Pick up a 2TB Samsung T7 portable SSD for only $250