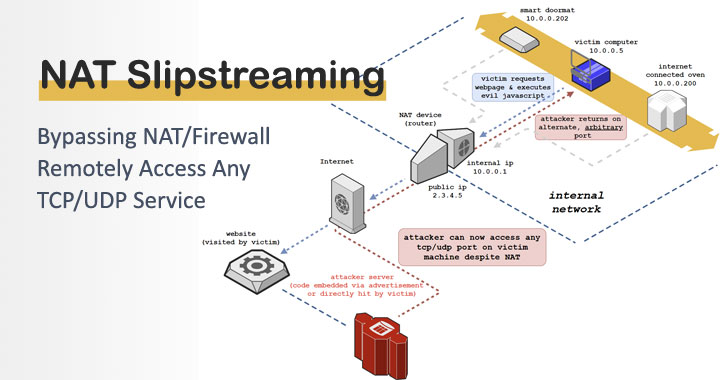
A new investigate has shown a strategy that allows an attacker to bypass firewall safety and remotely accessibility any TCP/UDP assistance on a sufferer equipment.
Named NAT Slipstreaming, the method requires sending the concentrate on a hyperlink to a malicious internet site (or a respectable web site loaded with malicious adverts) that, when frequented, ultimately triggers the gateway to open any TCP/UDP port on the target, thereby circumventing browser-dependent port restrictions.
The findings were being exposed by privateness and security researcher Samy Kamkar over the weekend.
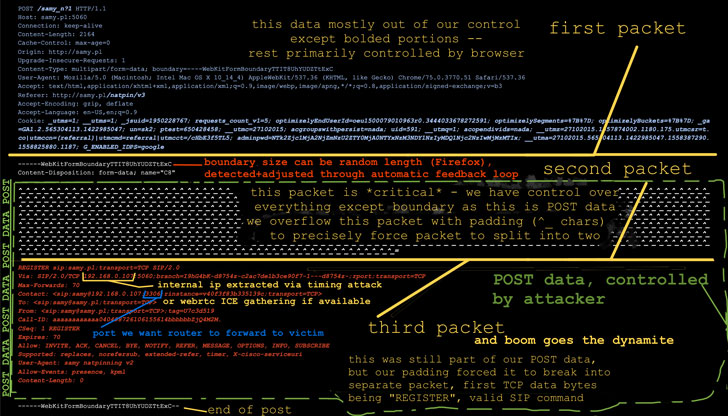
“NAT Slipstreaming exploits the user’s browser in conjunction with the Application Level Gateway (ALG) link monitoring mechanism built into NATs, routers, and firewalls by chaining inner IP extraction via timing attack or WebRTC, automatic distant MTU and IP fragmentation discovery, TCP packet dimensions massaging, Flip authentication misuse, precise packet boundary control, and protocol confusion as a result of browser abuse,” Kamkar claimed in an assessment.
The technique was carried out working with a NetGear Nighthawk R7000 router functioning Linux kernel variation 2.6.36.4.
Pinpointing Packet Boundaries
Network handle translation (NAT) is the course of action exactly where a network product, such as a firewall, remaps an IP handle house into another by modifying network tackle details in the IP header of packets even though they are in transit.
The major advantage is that it restrictions the selection of general public IP addresses made use of in an organization’s inner network and improves security by allowing a one general public IP deal with to be shared amongst various units.
NAT Slipstreaming functions by getting gain of TCP and IP packet segmentation to remotely modify the packet boundaries and making use of it to produce a TCP/UDP packet setting up with a SIP method this kind of as Register or INVITE.
SIP (short for Session Initiation Protocol) is a communications protocol utilised for initiating, sustaining, and terminating authentic-time multimedia periods for voice, video clip, and messaging programs.
In other words, a blend of packet segmentation and smuggling SIP requests in HTTP can be made use of to trick the NAT ALG into opening arbitrary ports for inbound connections to the shopper.
To attain this, a large HTTP Post request is despatched with an ID and a hidden web variety that details to an attack server working a packet sniffer, which is utilized to capture the MTU dimensions, facts packet dimensions, TCP and IP header measurements, among other folks, and subsequently transmitting the sizing info back to the sufferer shopper over a separate Article message.
What is actually a lot more, it also abuses an authentication perform in Convert (Traversal Working with Relays all-around NAT) — a protocol that’s used in conjunction with NATs to relay media from any peer to a further client in the network — to have out a packet overflow and induce IP packets to fragment.
The plan, in a nutshell, is to overflow a TCP or UDP packet by padding (with “^” figures) and pressure it to break up into two so that the SIP info packet is at the extremely start off of the next packet boundary.
Join to TCP/UDP through Packet Alteration
In the upcoming phase, the victim’s interior IP tackle is extracted applying WebRTC ICE on fashionable browsers this kind of as Chrome or Firefox or by executing a timing attack on frequent gateways (192.168.*.1, 10…1, and neighborhood networks).
“After the consumer will get the packet sizes and inside IP handle, it constructs a specifically crafted web form that pads the Submit information up until we imagine the packet will turn out to be fragmented, at which stage our SIP Sign up made up of inside IP handle is appended,” Kamkar observed. “The sort is submitted through Javascript with no consent from the victim.”
Just as the packets get to the attack server and it is really identified that the SIP packet is just not rewritten with the public IP address, an automatic information is despatched back again to the shopper, inquiring it to alter its packet size to a new boundary based mostly on the data beforehand gleaned from the sniffer.
Armed with the appropriate packet boundary, the NAT is deceived into pondering, “this is a legit SIP registration and from a SIP consumer on the victim’s device,” at some point resulting in the NAT to open up the port in the primary packet sent by the target.
“The router will now ahead any port the attacker chooses back to the interior target, all from simply searching to a internet site,” Kamkar mentioned.
The complete proof-of-strategy code for NAT Slipstreaming can be uncovered in this article.
Observed this write-up exciting? Observe THN on Fb, Twitter and LinkedIn to read a lot more exclusive content we publish.
Some parts of this article are sourced from:
thehackernews.com

 Anker unveils iPhone 12 charging accessories, Doraemon versions coming on Wednesday
Anker unveils iPhone 12 charging accessories, Doraemon versions coming on Wednesday