Even though Microsoft patched the bug acknowledged as CVE-2020-0796 again in March, extra than one 100,000 Windows devices are however vulnerable.
Extra than 100,000 Windows devices have not but been current to secure against a formerly-patched, critical and wormable flaw in Windows termed SMBGhost.
Microsoft patched the remote code-execution (RCE) flaw bug tracked as CVE-2020-0796 back in March it impacts Windows 10 and Windows Server 2019, and ranks 10 out of 10 on the CVSS scale. It exists in variation 3.1.1 of the Microsoft Server Information Block (SMB) protocol, the very same protocol that was focused by the notorious WannaCry ransomware in 2017.
“I’m unsure what method Shodan makes use of to determine no matter whether a specific equipment is vulnerable to SMBGhost, but if its detection mechanism is exact, it would surface that there are nonetheless more than 103,000 impacted equipment obtainable from the internet,” Jan Kopriva, a person of the researchers at the SANS Internet Storm Center, stated in a post on Wednesday.
In accordance to Kopriva, lots of of these vulnerable methods (22 p.c) are in Taiwan, Japan (20 %), Russia (11 percent) and the U.S. (9 %).
Microsoft unveiled its repair, KB4551762, as an update for Windows 10 (variations 1903 and 1909) and Windows Server 2019 (versions 1903 and 1909).
In lieu of a patch, Microsoft in March experienced pointed out that directors can use PowerShell to disable SMBv3 compression, which will block unauthenticated attackers from exploiting the vulnerability against an SMBv3 server. To guard customers from outdoors assaults, it is important to block TCP port 445 at the company perimeter firewall. Kopriva for his component also tracked a share of all IPs with an open up port 445 by way of Shodan, and uncovered that all round about 8 p.c of all IPs have port 445 open.
The chart down below demonstrates the quantity of susceptible units that are open to SMBGhost. Kopriva mentioned in a concept to Threatpost that the “dips” in the details are presumably prompted by Shodan re-scanning a large quantity of IP ranges.
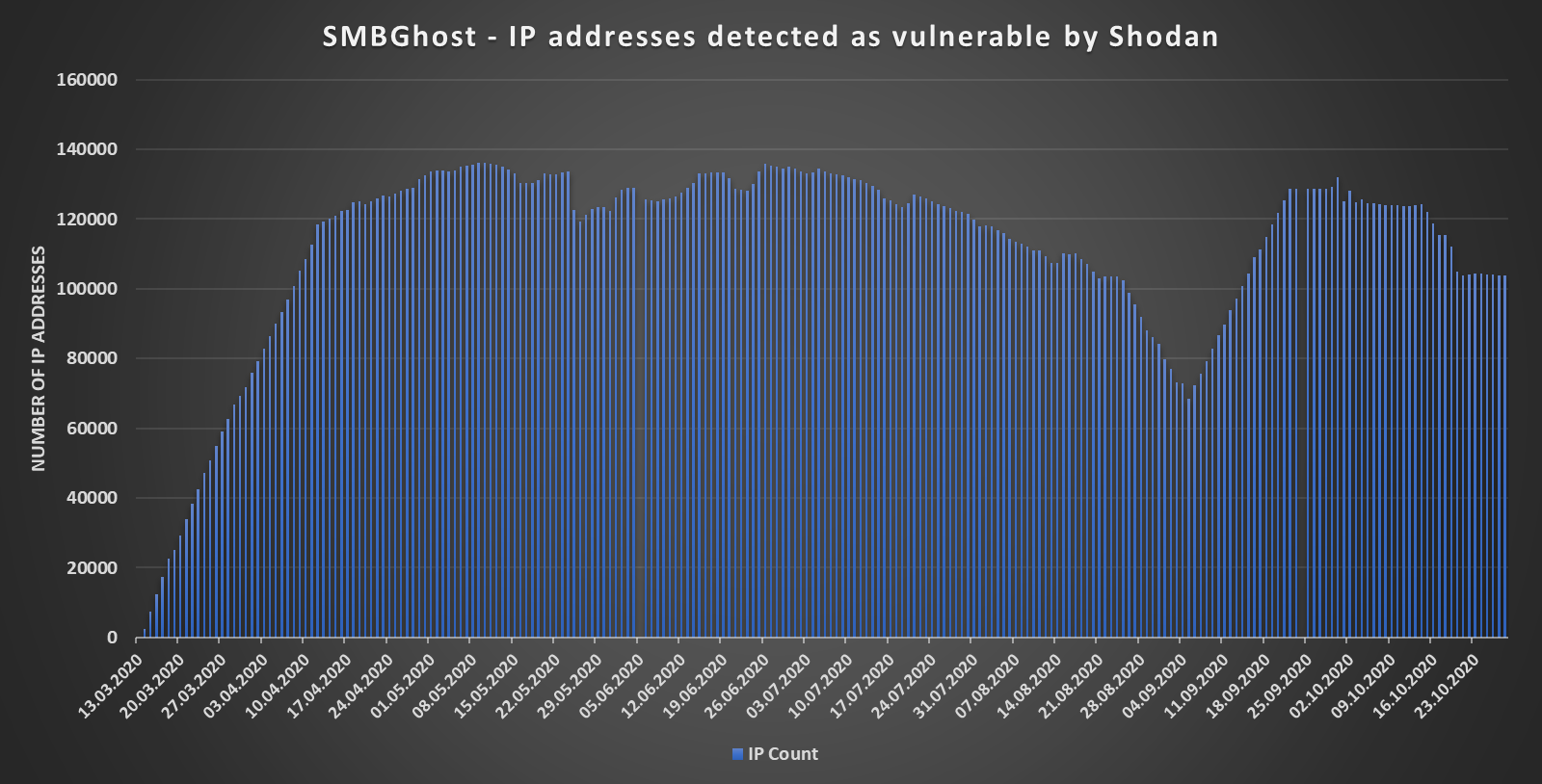
IP addresses detected as susceptible to SMBGhost by Shodan. Credit history: Jan Kopriva
The stress is on for process directors to patch their methods from SMBGhost, with many proof of principles (PoCs) for the flaw becoming introduced about the previous number of months. Even though numerous makes an attempt to exploit SMBGhost resulted only in denial of provider or area privilege escalation, a PoC released in June by an individual who goes by “Chompie,” who announced his exploit to accomplish RCE on Twitter.
“Since release of this PoC was again achieved with wide consideration from the media, a person could possibly reasonably count on that by now, most of the vulnerable devices would have been patched – specifically people available from the internet,” according to Kopriva.
These PoCs have also spurred the Division of Homeland Security to urge organizations to update in June, indicating that cybercriminals are targeting the unpatched methods: The company “strongly recommends applying a firewall to block server message block ports from the internet and to utilize patches to critical- and higher-severity vulnerabilities as soon as attainable.”
Some parts of this article are sourced from:
threatpost.com


 [Webinar and eBook] Learn How to Get the Best Value From Your EDR Solution
[Webinar and eBook] Learn How to Get the Best Value From Your EDR Solution