The DoNot APT danger group is leveraging the legit Google Firebase Cloud Messaging server as a command-and-manage (C2) conversation system.
An APT group is beginning fires with a new Android malware loader, which takes advantage of a respectable Google messaging support to bypass detection.
The malware, dubbed “Firestarter,” is utilised by an APT threat team called “DoNot.” DoNot employs Firebase Cloud Messaging (FCM), which is a cross-platform cloud solution for messages and notifications for Android, iOS and web programs. The service is provided by Firebase, a subsidiary of Google, and has been formerly leveraged by cybercriminals.
In this scenario, the loader employs it as a conversation mechanism to hook up with DoNot’s command-and-management (C2) servers, encouraging the group’s actions avoid detection.
“Our investigation discovered that DoNot has been experimenting with new strategies to preserve a foothold on their target devices,” in accordance to scientists with Cisco Talos in a Thursday investigation. “These experiments, substantiated in the Firestarter loader, are a indicator of how decided they are to preserve their operations inspite of becoming uncovered, which tends to make them a specifically harmful actor working in the espionage location.”
The DoNot staff proceeds to concentration on India and Pakistan, and is acknowledged for concentrating on Pakistani govt officials and Kashmiri non-income businesses (Kashmiris are a Dardic ethnic group indigenous to the disputed Kashmir Valley).
People are lured to put in a destructive app on their cell unit, very likely done via immediate messages that utilize social engineering, researchers claimed. The filename of these Android purposes (kashmir_sample.apk or Kashmir_Voice_v4.8.apk) clearly show continued curiosity in India, Pakistan and the Kashmir disaster.
After the app — which purports to be a chat system — is downloaded and opened, people get a message that chats are regularly loading, and that the software is not supported, and that uninstallation is in progress. This is a lure to make the victim consider that there was no malicious install, researchers reported. Once the information of uninstallation is demonstrated, the icon is eradicated from the person interface (though it nonetheless demonstrates in the software record in the phone’s configurations).

The destructive application purports to uninstall after down load. Credit: Cisco Talos
In the track record, on the other hand, the destructive app is trying to down load a payload employing FCM.
In accordance to Firebase, an FCM implementation involves two key elements for sending and acquiring messages. These include an application server on which to establish, goal and ship messages and an iOS, Android, or web (JavaScript) client app that gets messages by way of the corresponding platform-distinct transportation service.
In this situation, the app sends the C2 server a Google FCM token with various system details – which include the geographic site, IP tackle, IMEI and email deal with from the victims – which then will allow operators to determine no matter if the sufferer really should obtain the payload. This makes sure that only quite distinct units are sent the destructive payload, researchers claimed.
The C2 then sends a Google FCM information that contains the URL for the malware to download the payload. When the malware gets this concept, it checks if it consists of a critical known as “link,” and if that exists, it checks if it starts off with “https.” It then employs the hyperlink to down load the payload from a hosting server.
Of observe, researchers mentioned that the Google FCM interaction channel is encrypted and combined between other communications performed by Android OS utilizing the Google infrastructure, which helps it escape discover.
“DoNot crew is hiding element of their visitors between legit targeted visitors,” claimed researchers. “Even even though the destructive actors nevertheless will need a [C2] infrastructure, the hardcoded one particular is only needed at set up time, afterwards it can be discarded and easily changed by another a person. So, if their C2 is taken down by law enforcement or deemed malicious, they can still entry the victim’s unit and instruct it to speak to a new C2.”
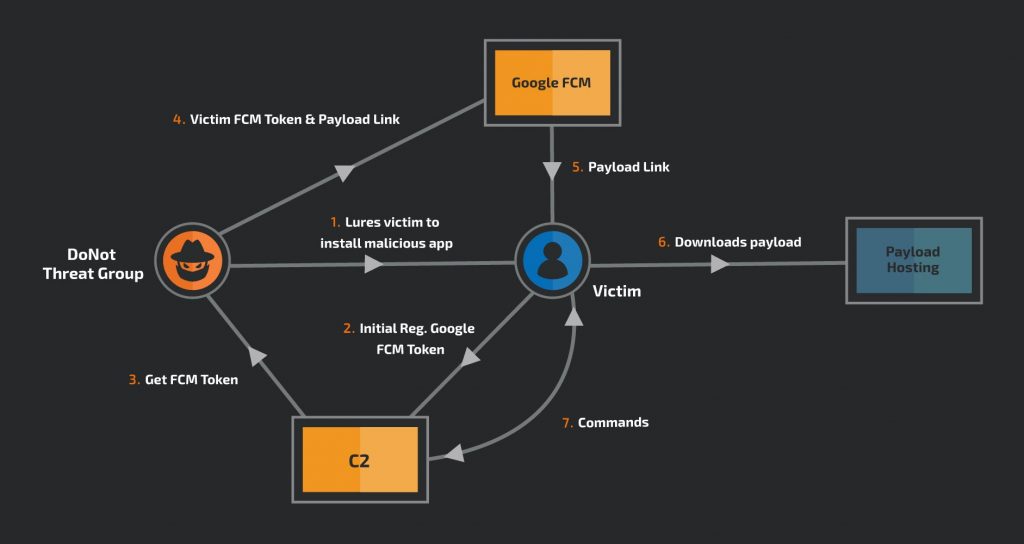
DoNot’s Firestarter malware attack vector. Credit history: Cisco Talos
The remaining payload, in the meantime, is not embedded in the Android software, producing it difficult for analysts to dissect it.
“This solution also can make detection a lot more difficult,” they reported. “The application is a loader with a faux person interface that manipulates the goal soon after putting in it.”
Hackers Put Bullseye on Health care: On Nov. 18 at 2 p.m. EDT find out why hospitals are getting hammered by ransomware assaults in 2020. Save your spot for this Free of charge webinaron healthcare cybersecurity priorities and listen to from foremost security voices on how info security, ransomware and patching need to be a precedence for just about every sector, and why. Sign up for us Wed., Nov. 18, 2-3 p.m. EDT for this LIVE, limited-engagement webinar.
Some parts of this article are sourced from:
threatpost.com


 Facebook pauses recommendations of political and social issues groups
Facebook pauses recommendations of political and social issues groups