When Microsoft patched the bug identified as CVE-2020-0796 again in March, considerably much more than a person 100,000 Windows equipment are having said that prone.
Significantly far more than 100,000 Windows procedures have not still been up to day to protect in opposition to a formerly-patched, critical and wormable flaw in Windows known as SMBGhost.
Microsoft patched the distant code-execution (RCE) flaw bug tracked as CVE-2020-0796 back once again in March it influences Windows 10 and Windows Server 2019, and ranks 10 out of 10 on the CVSS scale. It exists in version 3.1.1 of the Microsoft Server Concept Block (SMB) protocol, the exact same protocol that was certain by the infamous WannaCry ransomware in 2017.
✔ Permitted Seller by TheCyberSecurity
From Our Associates
Guard your on the net privateness and internet browsing by way of F-Safe Freedome VPN. F-Protected has proven to be a trusted firm but not staying connected to any federal government. F-Secure Freedome VPN encryptes all your connections to the internet in addition it hides your actual IP tackle so no one particular will know from which place you are browsing the web. F-Secure Freedome VPN is Netflix and Amazon Key pleasant which usually means you can conveniently watch the flicks and series that are intended for Amercian viewers. Get F-Safe Freedome VPN with 50% discount from our companion: SerialCart® (Confined Offer you).
➤ Activate Your Coupon Code
“I’m not guaranteed what system Shodan normally takes edge of to establish no matter of no matter whether a specified gear is inclined to SMBGhost, but if its detection mechanism is precise, it would seem that there are even so in excessive of 103,000 impacted devices obtainable from the internet,” Jan Kopriva, 1 of the researchers at the SANS Internet Storm Center, spelled out in a post on Wednesday.

According to Kopriva, numerous of these prone units (22 for every cent) are in Taiwan, Japan (20 p.c), Russia (11 p.c) and the U.S. (9 per cent).
Microsoft developed its accurate, KB4551762, as an update for Windows 10 (variations 1903 and 1909) and Windows Server 2019 (variations 1903 and 1909).
In lieu of a patch, Microsoft in March seasoned popular that directors can use PowerShell to disable SMBv3 compression, which will block unauthenticated attackers from exploiting the vulnerability in opposition to an SMBv3 server. To guard clientele from outside the house the house attacks, it is important to block TCP port 445 at the business perimeter firewall. Kopriva for his component also tracked a percentage of all IPs with an open up up port 445 through Shodan, and uncovered that in general someplace all around 8 p.c of all IPs have port 445 open up up.
The chart beneath demonstrates the array of vulnerable units that are open up to SMBGhost. Kopriva famous in a information to Threatpost that the “dips” in the info are presumably brought on by Shodan re-scanning a significant variety of IP ranges.
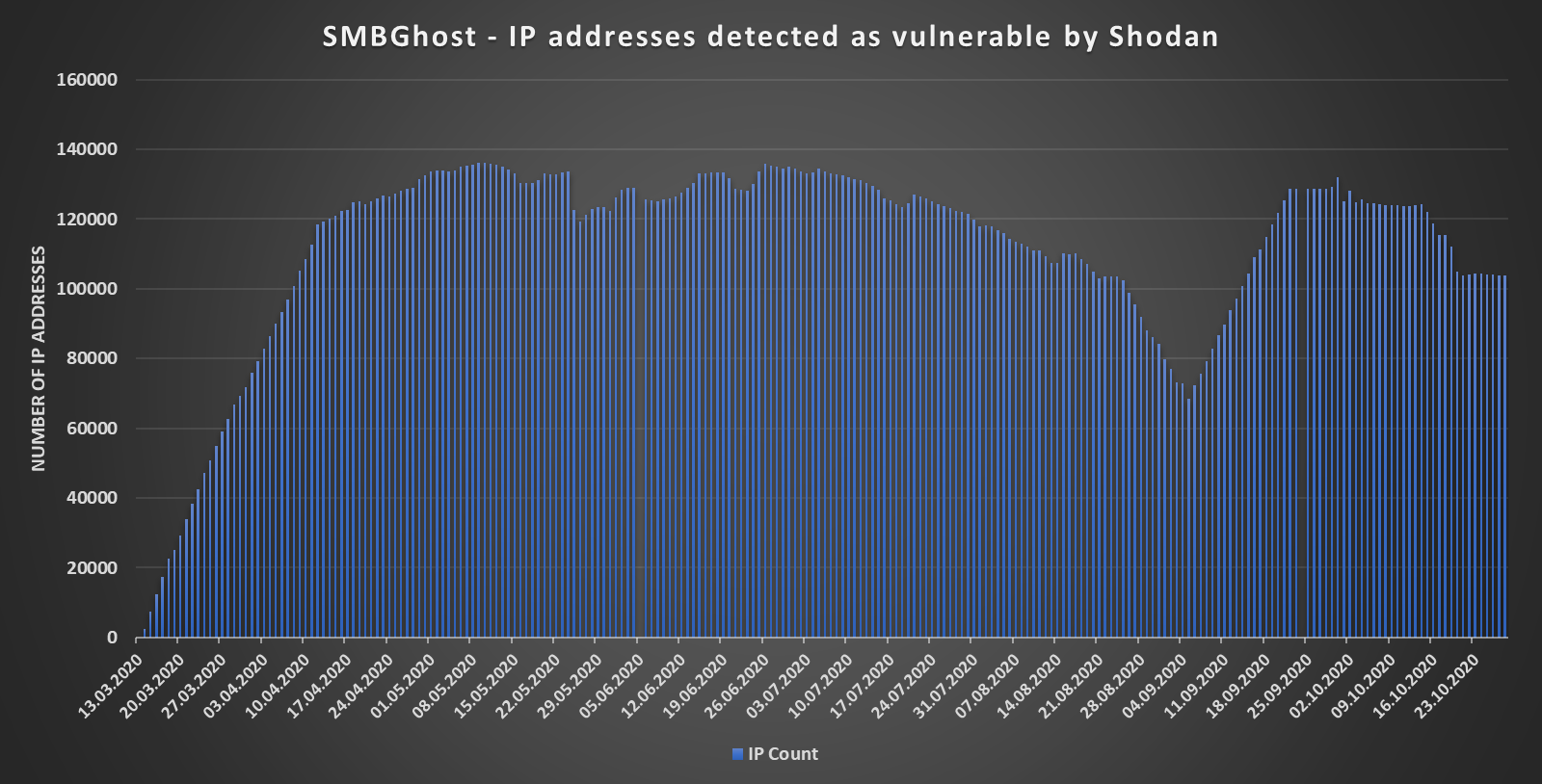
IP addresses detected as vulnerable to SMBGhost by Shodan. Credit history ranking: Jan Kopriva
The stress is on for approach directors to patch their systems from SMBGhost, with a number of evidence of rules (PoCs) for the flaw acquiring made higher than the before several months. When lots of tries to exploit SMBGhost resulted only in denial of assistance or local privilege escalation, a PoC manufactured in June by somebody who goes by “Chompie,” who announced his exploit to achieve RCE on Twitter.
“Since launch of this PoC was all above again fulfilled with enormous awareness from the media, a particular person may well possibly moderately count on that by now, most of the susceptible machines would have been patched – particularly persons available from the internet,” in accordance to Kopriva.
These PoCs have also spurred the Section of Homeland Security to urge companies to update in June, expressing that cybercriminals are concentrating on the unpatched strategies: The company “strongly endorses performing with a firewall to block server thought block ports from the internet and to make use of patches to critical- and better-severity vulnerabilities as immediately as attainable.”
Some pieces of this posting are sourced from:
threatpost.com


 Apple iPhone 12 mini handled on video
Apple iPhone 12 mini handled on video