Economical establishments in Latin America are currently being threatened by a banking trojan named Mekotio (aka Melcoz).
That is according to conclusions from Craze Micro, which stated it just lately noticed a surge in cyber assaults distributing the Windows malware.
Mekotio, regarded to be actively put to use because 2015, is identified to goal Latin American nations around the world like Brazil, Chile, Mexico, Spain, Peru, and Portugal with an aim to steal banking credentials.
Initial documented by ESET in August 2020, it really is element of a tetrade of banking trojans concentrating on the location Guildma, Javali, and Grandoreiro, the latter of which was dismantled by legislation enforcement before this year.
“Mekotio shares popular traits for this variety of malware, these types of as remaining penned in Delphi, making use of bogus pop-up windows, made up of backdoor performance and targeting Spanish- and Portuguese-talking international locations,” the Slovakian cybersecurity agency claimed at the time.
The malware procedure endured a blow in July 2021 when Spanish law enforcement agencies arrested 16 folks belonging to a prison network in relationship with orchestrating social engineering campaigns targeting European customers that shipped Grandoreiro and Mekotio.
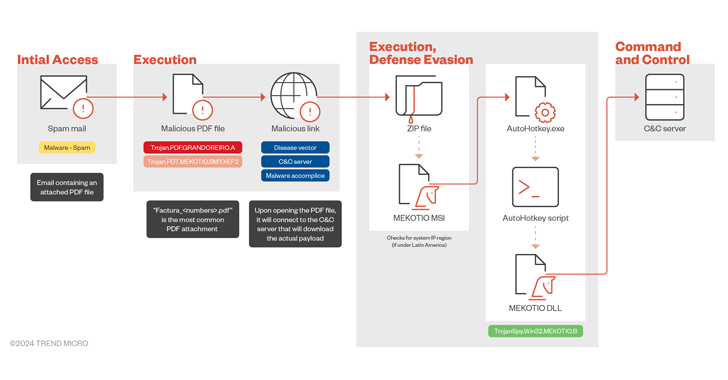
Attack chains require the use of tax-themed phishing e-mail that intention to trick recipients into opening malicious attachments or clicking on bogus one-way links that lead to the deployment of an MSI installer file, which, in change, helps make use of an AutoHotKey (AHK) script to start the malware.
It can be really worth noting that the infection system marks a slight deviation from the just one beforehand in-depth by Verify Position in November 2021, which created use of an obfuscated batch script that runs a PowerShell script to download a next-stage ZIP file that contains the AHK script.
After installed, Mekotio harvests system facts and establishes make contact with with a command-and-command (C2) server to get even more directions.
It is most important objective is to siphon banking credentials by displaying fake pop-ups that impersonate legit banking internet sites. It can also seize screenshots, log keystrokes, steal clipboard details, and create persistence on the host employing scheduled tasks.

The stolen information and facts can then be applied by the menace actors to acquire unauthorized obtain to users’ lender accounts and perform fraudulent transactions.
“The Mekotio banking trojan is a persistent and evolving threat to economic methods, primarily in Latin American nations,” Craze Micro stated. “It employs phishing e-mail to infiltrate devices, with the intention of thieving sensitive data although also protecting a solid foothold on compromised machines.”
The progress arrives as Mexican cybersecurity business Scitum disclosed information of a new Latin American banking trojan codenamed Red Mongoose Daemon that, identical to Mekotio, makes use of MSI droppers distributed by means of phishing email messages masquerading as invoices and tax notes.
“The principal objective of Pink Mongoose Daemon is to steal victims’ banking information by spoofing PIX transactions by overlapping windows,” the company said. “This trojan is aimed at Brazilian stop end users and workforce of corporations with banking info.”
“Purple Mongoose Daemon has capabilities for manipulating and generating windows, executing instructions, controlling the laptop remotely, manipulating web browsers, hijacking clipboards, and impersonating Bitcoin wallets by replacing copied wallets with the types utilised by cybercriminals.”
Observed this write-up fascinating? Follow us on Twitter and LinkedIn to read a lot more exceptional information we publish.
Some parts of this article are sourced from:
thehackernews.com

 Critical Unpatched Flaws Disclosed in Popular Gogs Open-Source Git Service
Critical Unpatched Flaws Disclosed in Popular Gogs Open-Source Git Service