Many security flaws have been disclosed in Emerson Rosemount fuel chromatographs that could be exploited by malicious actors to obtain sensitive facts, induce a denial-of-provider (DoS) ailment, and even execute arbitrary instructions.
The flaws affect GC370XA, GC700XA, and GC1500XA and reside in versions 4.1.5 and prior.
According to operational technology (OT) security firm Claroty, the vulnerabilities consist of two command injection flaws and two independent authentication and authorization vulnerabilities that could be weaponized by unauthenticated attackers to accomplish a huge vary of malicious steps ranging from authentication bypass to command injection.
“Profitable exploitation of these vulnerabilities could make it possible for an unauthenticated attacker with network accessibility to operate arbitrary instructions, accessibility delicate facts, trigger a denial-of-services issue, and bypass authentication to acquire admin abilities,” the U.S. Cybersecurity and Infrastructure Security Agency (CISA) stated in an advisory introduced in January.
The chromatograph, which is utilised for carrying out critical gasoline measurements, can be configured and managed by suggests of a software identified as MON. The software program can also be employed to retail outlet critical data and generate stories these as chromatograms, alarm history, party logs, and routine maintenance logs.
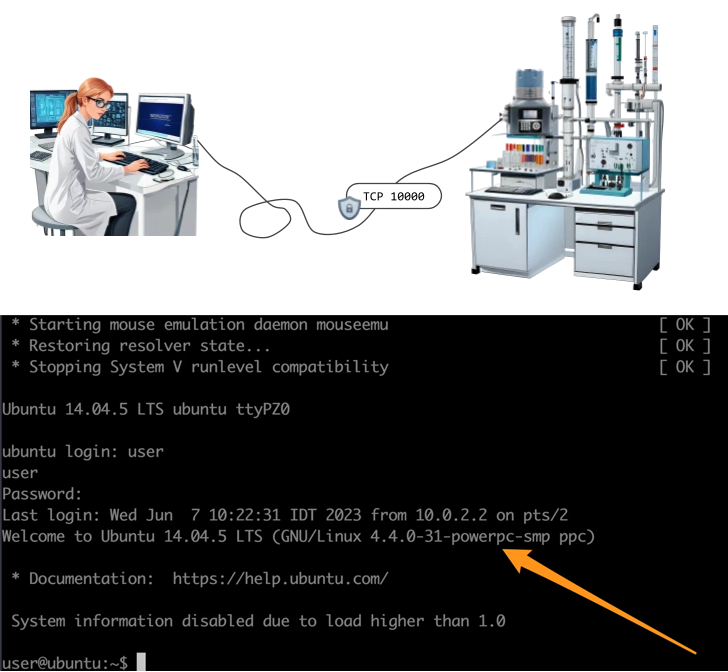
Claroty’s examination of the firmware and the proprietary protocol made use of for communications among the machine and the Windows shopper named MON2020 has discovered the pursuing shortcomings –
- CVE-2023-46687 (CVSS score: 9.8) – An unauthenticated person with network obtain could execute arbitrary instructions in root context from a remote computer
- CVE-2023-49716 (CVSS rating: 6.9) – An authenticated person with network obtain could operate arbitrary commands from a distant personal computer
- CVE-2023-51761 (CVSS score: 8.3) – An unauthenticated user with network accessibility could bypass authentication and purchase admin capabilities by resetting the associated password
- CVE-2023-43609 (CVSS rating: 6.9) – An unauthenticated user with network entry could get hold of accessibility to delicate data or induce a denial-of-support condition
Adhering to liable disclosure, Emerson has launched [PDF] an up to date variation of the firmware that addresses the vulnerabilities. The business is also recommending conclusion consumers to follow cybersecurity best techniques and make certain that the impacted products and solutions are not right uncovered to the internet.

The disclosure comes as Nozomi Networks specific various flaws in AiLux RTU62351B that could be abused to entry delicate methods on the system, change its configuration, and even realize execution of arbitrary instructions as root. The vulnerabilities have been collectively dubbed I11USION.
Flaws have also been determined in Proges As well as temperature monitoring devices and their connected computer software, particularly Sensor Net Hook up and Thermoscan IP, that could allow admin privileges above critical health-related systems, therefore making it attainable for a destructive actor to manipulate system configurations, put in malware, and exfiltrate knowledge.
These vulnerabilities, which continue to be unpatched, could also end result in a DoS issue of professional medical monitoring infrastructure, foremost to spoilage of temperature-sensitive medications and vaccines.
Discovered this write-up appealing? Observe us on Twitter and LinkedIn to read through far more exclusive written content we post.
Some parts of this article are sourced from:
thehackernews.com

 TeamViewer Detects Security Breach in Corporate IT Environment
TeamViewer Detects Security Breach in Corporate IT Environment