New conclusions have discovered connections involving an Android adware named DragonEgg and an additional complex modular iOS surveillanceware resource named LightSpy.
DragonEgg, along with WyrmSpy (aka AndroidControl), was initially disclosed by Lookout in July 2023 as a pressure of malware able of collecting delicate facts from Android units. It was attributed to the Chinese country-point out team APT41.
On the other hand, aspects about LightSpy arrived to gentle in March 2020 as section of a campaign dubbed Operation Poisoned Information in which Apple iPhone users in Hong Kong have been targeted with watering hole assaults to install the adware.

Now, in accordance to Dutch cell security business ThreatFabric, the attack chains include the use of a trojanized Telegram app which is made to obtain a second-phase payload (smallmload.jar), which, in transform, is configured to obtain a 3rd element codenamed Main.
Even more analysis of the artifacts has discovered that the implant has been actively maintained considering the fact that at minimum December 11, 2018, with the most current model released on July 13, 2023.
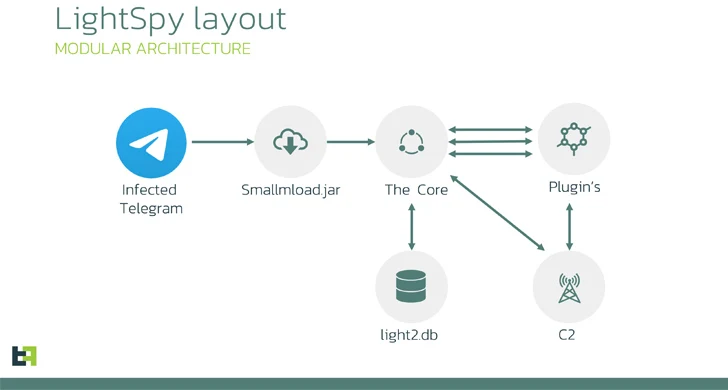
The main module of LightSpy (i.e., DragonEgg) capabilities as an orchestrator plugin dependable for collecting the device fingerprint, creating get in touch with with a remote server, awaiting further more directions, and updating itself as perfectly as the plugins.
“LightSpy Main is really versatile in terms of configuration: operators can exactly regulate the spyware utilizing the updatable configuration,” ThreatFabric said, noting that WebSocket is employed for command delivery and HTTPS is used for info exfiltration.
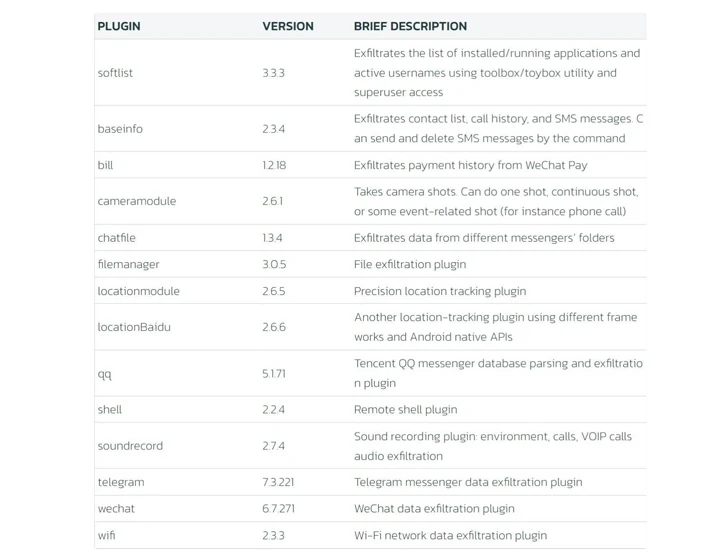
Some of the notable plugins contain a locationmodule that tracks victims’ precise spots, soundrecord that can capture ambient audio as properly as from WeChat VOIP audio conversations, and a invoice module to acquire payment background from WeChat Pay back.
LightSpy’s command-and-handle (C2) contains quite a few servers located in Mainland China, Hong Kong, Taiwan, Singapore, and Russia, with the malware and WyrmSpy sharing the same infrastructure.

ThreatFabric explained it also identified a server hosting facts from 13 exclusive phone numbers belonging to Chinese mobile phone operators, elevating the risk that the facts both signifies the testing numbers of LightSpy developers or victims’.
The backlinks concerning DragonEgg and LightSpy stem from similarities in configuration designs, runtime construction and plugins, and the C2 communication structure.
“The way the threat actor team dispersed the first malicious phase inside of popular messenger was a clever trick,” the company reported.
“There have been numerous gains of that: the implant inherited all the accessibility permissions that the provider software experienced. In the scenario of messenger, there have been a lot of non-public permissions this kind of as digicam and storage accessibility.”
Discovered this article appealing? Comply with us on Twitter and LinkedIn to browse far more special articles we publish.
Some parts of this article are sourced from:
thehackernews.com

 Wing Disrupts the Market by Introducing Affordable SaaS Security
Wing Disrupts the Market by Introducing Affordable SaaS Security