A subtle stealer-as-a-ransomware menace dubbed RedEnergy has been noticed in the wild focusing on energy utilities, oil, fuel, telecom, and machinery sectors in Brazil and the Philippines as a result of their LinkedIn pages.
The malware “possesses the potential to steal info from different browsers, enabling the exfiltration of sensitive data, though also incorporating distinct modules for carrying out ransomware routines,” Zscaler scientists Shatak Jain and Gurkirat Singh stated in a the latest assessment.
The goal, the scientists noted, is to pair facts theft with encryption with the aim of inflicting greatest injury to the victims.
The starting position for the multi-phase attack is a FakeUpdates (aka SocGholish) marketing campaign that methods people into downloading JavaScript-centered malware less than the guise of web browser updates.
What would make it novel is the use of dependable LinkedIn web pages to focus on victims, redirecting consumers clicking on the web page URLs to a bogus landing website page that prompts them to update their web browsers by clicking on the proper icon (Google Chrome, Microsoft Edge, Mozilla Firefox, or Opera), performing so which effects in the obtain a destructive executable.
Adhering to a productive breach, the malicious binary is applied as a conduit to set up persistence, complete the real browser update, and also fall a stealer able of covertly harvesting sensitive information and facts and encrypting the stolen files, leaving the victims at risk of likely information loss, publicity, or even the sale of their important info.
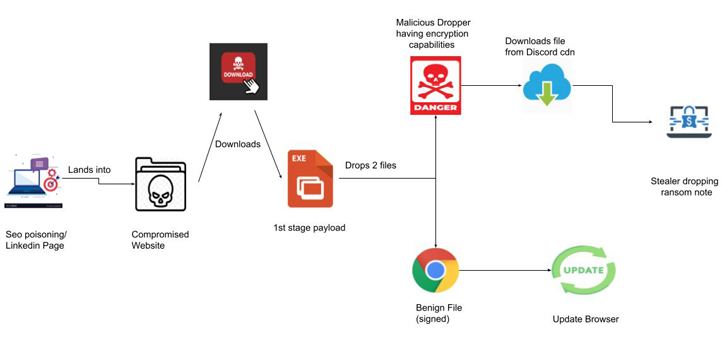
Zscaler reported it found out suspicious interactions getting spot in excess of a File Transfer Protocol (FTP) relationship, elevating the risk that valuable details is becoming exfiltrated to actor-managed infrastructure.
In the closing phase, RedEnergy’s ransomware component proceeds to encrypt the user’s data, suffixing the “.FACKOFF!” extension to each encrypted file, deleting present backups, and dropping a ransom observe in each folder.
Approaching WEBINAR🔐 Privileged Accessibility Administration: Understand How to Conquer Crucial Challenges
Explore distinctive ways to conquer Privileged Account Administration (PAM) difficulties and degree up your privileged accessibility security tactic.
Reserve Your Place
Victims are envisioned to make a payment of .005 BTC (about $151) to a cryptocurrency wallet described in the note to get back entry to the data files. RedEnergy’s twin functions as a stealer and ransomware represent an evolution of the cybercrime landscape.
The enhancement also follows the emergence of a new RAT-as-a-ransomware threat group in which remote access trojans this kind of as Venom RAT and Anarchy Panel RAT have been geared up with ransomware modules to lock several file extensions at the rear of encryption limitations.
“It is very important for people today and companies to exercise utmost caution when accessing websites, particularly these linked from LinkedIn profiles,” the scientists said. “Vigilance in verifying the authenticity of browser updates and staying wary of unanticipated file downloads is paramount to safeguard from such destructive campaigns.”
Discovered this write-up exciting? Abide by us on Twitter and LinkedIn to read additional exclusive written content we publish.
Some parts of this article are sourced from:
thehackernews.com

 Secrets, Secrets Are No Fun. Secrets, Secrets (Stored in Plain Text Files) Hurt Someone
Secrets, Secrets Are No Fun. Secrets, Secrets (Stored in Plain Text Files) Hurt Someone