An active monetarily motivated marketing campaign is focusing on vulnerable SSH servers to covertly ensnare them into a proxy network.
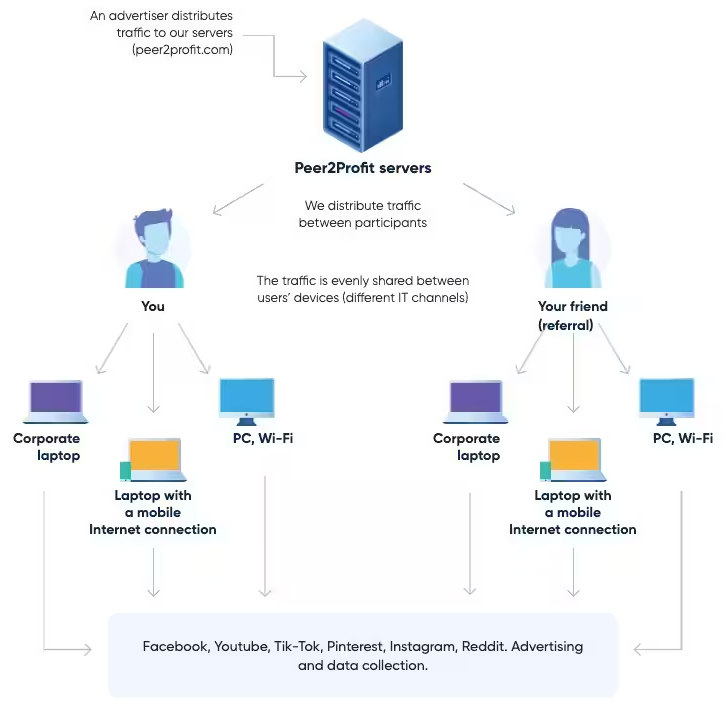
“This is an active campaign in which the attacker leverages SSH for remote access, functioning destructive scripts that stealthily enlist victim servers into a peer-to-peer (P2P) proxy network, these as Peer2Income or Honeygain,” Akamai researcher Allen West explained in a Thursday report.
Unlike cryptojacking, in which a compromised system’s sources are employed to illicitly mine cryptocurrency, proxyjacking presents the skill for threat actors to leverage the victim’s unused bandwidth to covertly operate diverse providers as a P2P node.
This presents two-fold gains: It not only enables the attacker to monetize the more bandwidth with a appreciably diminished source load that would be necessary to carry out cryptojacking, it also lessens the possibilities of discovery.

“It is a stealthier alternative to cryptojacking and has severe implications that can raise the headaches that proxied Layer 7 attacks currently serve,” West explained.
To make issues even worse, the anonymity furnished by proxyware products and services can be a double-edged sword in that they could be abused by malicious actors to obfuscate the supply of their attacks by routing site visitors through intermediary nodes.
Akamai, which found the hottest campaign on June 8, 2023, said the activity is designed to breach prone SSH servers and deploy an obfuscated Bash script that, in flip, is outfitted to fetch necessary dependencies from a compromised web server, which includes the curl command-line instrument by camouflaging it as a CSS file (“csdark.css”).
The stealthy script more actively searches for and terminates competing circumstances working bandwidth-sharing products and services, right before launching Docker products and services that share the victim’s bandwidth for income.
A even further evaluation of the web server has unveiled that it is really also remaining utilised to host a cryptocurrency miner, suggesting that the threat actors are dabbling in equally cryptojacking and proxyjacking assaults.

Although proxyware is not inherently nefarious, Akamai famous that “some of these providers do not correctly verify the sourcing of the IPs in the network, and even occasionally recommend that people install the computer software on their operate pcs.”
But these kinds of operations transcend into the realm of cybercrime when the programs are mounted without having the users’ know-how or consent, therefore allowing the risk actor to control numerous units and produce illegitimate income.
“Outdated tactics stay helpful, particularly when paired with new outcomes,” West reported. “Typical security methods continue to be an productive prevention system, like powerful passwords, patch administration, and meticulous logging.”
Discovered this posting exciting? Comply with us on Twitter and LinkedIn to examine more unique content material we submit.
Some parts of this article are sourced from:
thehackernews.com

 MITRE Unveils Top 25 Most Dangerous Software Weaknesses of 2023: Are You at Risk?
MITRE Unveils Top 25 Most Dangerous Software Weaknesses of 2023: Are You at Risk?