A security shortcoming in Microsoft Azure Lively Directory (Advert) Open Authorization (OAuth) course of action could have been exploited to attain whole account takeover, scientists stated.
California-centered identity and obtain administration assistance Descope, which learned and described the issue in April 2023, dubbed it nOAuth.
“nOAuth is an authentication implementation flaw that can influence Microsoft Azure Ad multi-tenant OAuth applications,” Omer Cohen, chief security officer at Descope, claimed.
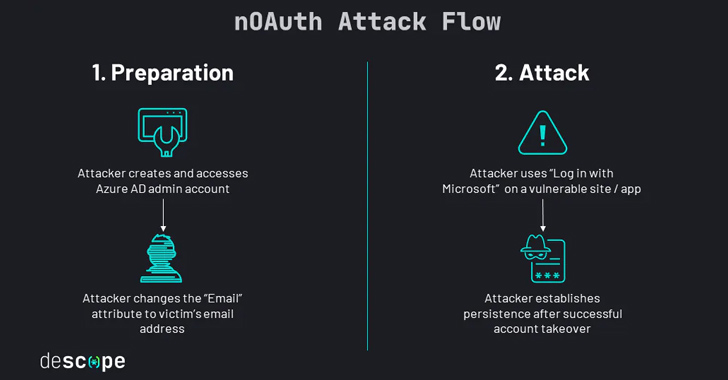
The misconfiguration has to do with how a destructive actor can modify email attributes below “Call Information” in the Azure Ad account and exploit the “Log in with Microsoft” element to hijack a sufferer account.

To pull off the attack, all an adversary has to do is to develop and accessibility an Azure Advert admin account and modify their email address to that of a sufferer and acquire gain of the one indicator-on scheme on a susceptible app or site.
“If the application merges consumer accounts without validation, the attacker now has comprehensive manage about the victim’s account, even if the sufferer doesn’t have a Microsoft account,” Cohen described.
Profitable exploitation grants the adversary an “open up area” to set up persistence, exfiltrate data, and have out other article-exploitation activities centered on the mother nature of the application.
This stems from the fact that an email address is the two mutable and unverified in Azure Advert, prompting Microsoft to issue a warning not to use email statements for authorization functions.
Approaching WEBINAR🔐 Mastering API Security: Comprehending Your Real Attack Floor
Find out the untapped vulnerabilities in your API ecosystem and choose proactive measures in direction of ironclad security. Be a part of our insightful webinar!
Sign up for the Session.wn-button,.wn-label,.wn-label:right afterdisplay screen:inline-block.verify_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px solid #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-leading-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-right-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-measurement:13pxmargin:20px 0font-excess weight:600letter-spacing:.6pxcolor:#596cec.wn-label:afterwidth:50pxheight:6pxcontent:”border-leading:2px strong #d9deffmargin: 8px.wn-titlefont-dimension:21pxpadding:10px 0font-weight:900text-align:leftline-top:33px.wn-descriptiontext-align:leftfont-sizing:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-color:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
The tech large characterized the issue as an “insecure anti-pattern applied in Azure Ad (AAD) apps” the place the use of the email assert from entry tokens for authorization can direct to an escalation of privilege.
“An attacker can falsify the email assert in tokens issued to programs,” it noted. “Furthermore, the threat of information leakage exists if apps use this sort of statements for email lookup.”
It also stated it determined and notified several multi-tenant applications with people that benefit from an email tackle with an unverified domain owner.
Uncovered this write-up exciting? Follow us on Twitter and LinkedIn to examine far more distinctive written content we submit.
Some parts of this article are sourced from:
thehackernews.com

 Chinese Hacker Group ‘Flea’ Targets American Ministries with Graphican Backdoor
Chinese Hacker Group ‘Flea’ Targets American Ministries with Graphican Backdoor