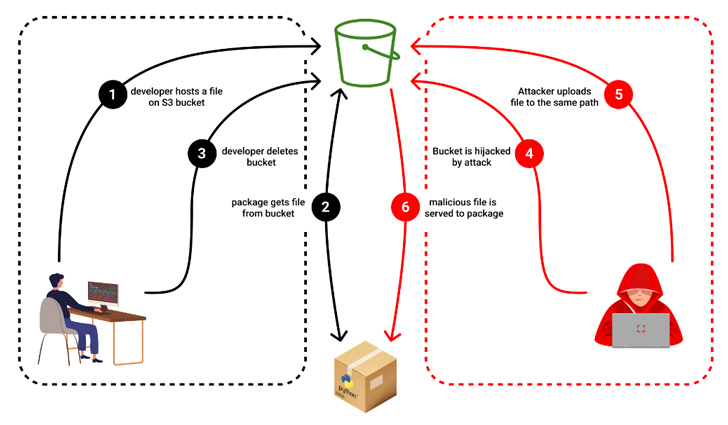
In what’s a new form of computer software source chain attack aimed at open up supply projects, it has emerged that threat actors could seize regulate of expired Amazon S3 buckets to serve rogue binaries with no altering the modules by themselves.
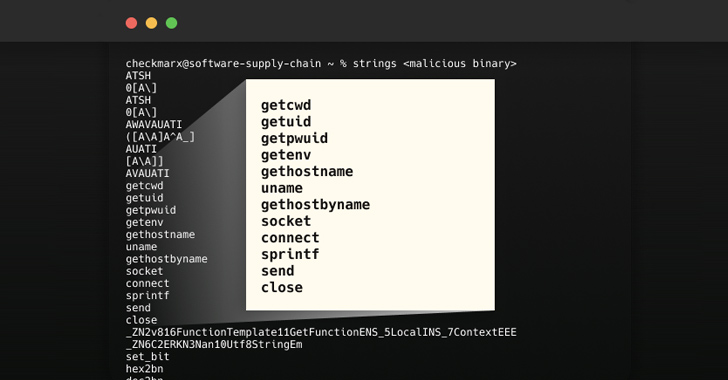
“Malicious binaries steal the user IDs, passwords, regional equipment natural environment variables, and regional host identify, and then exfiltrates the stolen info to the hijacked bucket,” Checkmarx researcher Guy Nachshon stated.
The attack was 1st observed in the case of an npm bundle known as bignum, which, till variation .13., relied on an Amazon S3 bucket to down load pre-created binary variations of an addon named node-pre-gyp all through set up.

“These binaries were being revealed on a now-expired S3 bucket which has since been claimed by a destructive third party which is now serving binaries made up of malware that exfiltrates info from the user’s pc,” according to a GitHub advisory posted on May perhaps 24, 2023.
An unknown menace actor is stated to have seized on the possibility that the S3 bucket was once energetic to deliver malware when unsuspecting users downloaded the package in dilemma.
“If a deal pointed to a bucket as its resource, the pointer would continue to exist even after the bucket’s deletion,” Nachshon described. “This abnormality permitted the attacker to reroute the pointer towards the taken-around bucket.”
A reverse engineering of the malware sample has unveiled that it can be capable of plundering consumer qualifications and setting specifics, and transmitting the information and facts to the exact same hijacked bucket.
Checkmarx said it observed many packages making use of abandoned S3 buckets, building them vulnerable to the novel attack vector. If anything, the enhancement is a indicator that risk actors are frequently on the lookout for various methods to poison the computer software source chain.
Forthcoming WEBINAR🔐 Mastering API Security: Knowledge Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and get proactive actions toward ironclad security. Be part of our insightful webinar!
Join the Session.wn-button,.wn-label,.wn-label:just afterdisplay screen:inline-block.examine_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px good #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-major-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-correct-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-measurement:13pxmargin:20px 0font-excess weight:600letter-spacing:.6pxcolor:#596cec.wn-label:just afterwidth:50pxheight:6pxcontent:”border-best:2px good #d9deffmargin: 8px.wn-titlefont-dimension:21pxpadding:10px 0font-pounds:900textual content-align:leftline-top:33px.wn-descriptiontext-align:leftfont-size:15.6pxline-height:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-colour:#4469f5font-size:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
“This new twist in the realm of subdomain takeovers serves as a wake-up call to developers and organizations,” Nachshon reported. “An deserted hosting bucket or an out of date subdomain is not just a overlooked artifact in the improper palms, it can grow to be a strong weapon for facts theft and intrusion.”
The development also comes virtually a 7 days right after Cyble unearthed 160 malicious python offers that are estimated to have been downloaded above 45,000 periods and featured capabilities to extract login qualifications and credit history card particulars.
Identified this posting attention-grabbing? Stick to us on Twitter and LinkedIn to study additional exceptional content we post.
Some parts of this article are sourced from:
thehackernews.com

 #InfosecurityEurope: New Study Takes a Deep Dive Into Lookalike Attacks
#InfosecurityEurope: New Study Takes a Deep Dive Into Lookalike Attacks