Two “perilous” security vulnerabilities have been disclosed in Microsoft Azure Bastion and Azure Container Registry that could have been exploited to have out cross-web site scripting (XSS) assaults.
“The vulnerabilities allowed unauthorized obtain to the victim’s session within the compromised Azure support iframe, which can guide to extreme consequences, like unauthorized information obtain, unauthorized modifications, and disruption of the Azure services iframes,” Orca security researcher Lidor Ben Shitrit said in a report shared with The Hacker Information.
XSS attacks choose place when menace actors inject arbitrary code into an if not reliable web-site, which then gets executed every time when unsuspecting people check out the web site.
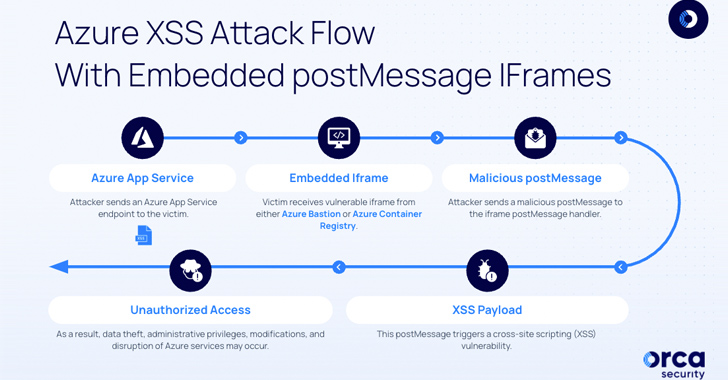
The two flaws discovered by Orca leverage a weakness in the postMessage iframe, which allows cross-origin conversation in between Window objects.

This intended that the shortcoming could be abused to embed endpoints in remote servers employing the iframe tag and eventually execute malicious JavaScript code, top to the compromise of delicate data.
Nonetheless, in get to exploit these weaknesses, a threat actor would have to conduct reconnaissance on distinct Azure providers to single out susceptible endpoints embedded in the Azure portal that may have missing X-Body-Selections headers or weak Content material Security Policies (CSPs).
“Once the attacker effectively embeds the iframe in a remote server, they move forward to exploit the misconfigured endpoint,” Ben Shitrit stated. “They concentration on the postMessage handler, which handles distant occasions these as postMessages.”
By examining the legit postMessages sent to the iframe from portal.azure[.]com, the adversary could subsequently craft correct payloads by embedding the susceptible iframe in an actor-managed server (e.g., ngrok) and producing a postMessage handler that provides the malicious payload.
So when a victim is lured into viewing the compromised endpoint, the “destructive postMessage payload is shipped to the embedded iframe, triggering the XSS vulnerability and executing the attacker’s code inside of the victim’s context.”
Forthcoming WEBINAR🔐 Mastering API Security: Being familiar with Your Accurate Attack Surface
Explore the untapped vulnerabilities in your API ecosystem and consider proactive steps toward ironclad security. Join our insightful webinar!
Join the Session.wn-button,.wn-label,.wn-label:immediately afterexhibit:inline-block.look at_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px stable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-best-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-ideal-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-sizing:13pxmargin:20px 0font-pounds:600letter-spacing:.6pxcolor:#596cec.wn-label:just afterwidth:50pxheight:6pxcontent:”border-prime:2px solid #d9deffmargin: 8px.wn-titlefont-measurement:21pxpadding:10px 0font-weight:900textual content-align:leftline-peak:33px.wn-descriptiontextual content-align:leftfont-sizing:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-dimension:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-pounds:500letter-spacing:.2px
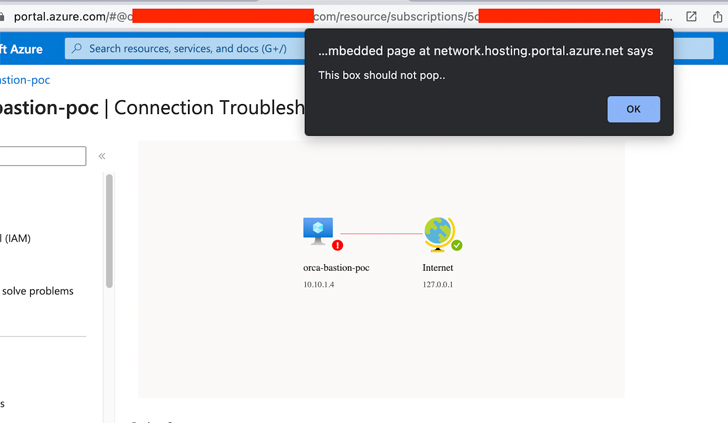
In a evidence-of-notion (PoC) shown by Orca, a specifically crafted postMessage was discovered to be able to manipulate the Azure Bastion Topology Check out SVG exporter or Azure Container Registry Swift Start to execute an XSS payload.
Subsequent liable disclosure of the flaws on April 13 and May 3, 2023, Microsoft rolled out security fixes to remediate them. No more action is demanded on the component of Azure customers.
The disclosure comes extra than a month immediately after Microsoft plugged three vulnerabilities in the Azure API Administration company that could be abused by destructive actors to acquire entry to sensitive info or backend products and services.
Located this post fascinating? Observe us on Twitter and LinkedIn to read through much more unique material we post.
Some parts of this article are sourced from:
thehackernews.com

 Researchers Uncover XSS Vulnerabilities in Azure Services
Researchers Uncover XSS Vulnerabilities in Azure Services