A security flaw has been uncovered in the WooCommerce Stripe Gateway WordPress plugin that could lead to the unauthorized disclosure of delicate information and facts.
The flaw, tracked as CVE-2023-34000, impacts versions 7.4. and down below. It was addressed by the plugin maintainers in model 7.4.1, which delivered on May possibly 30, 2023.
WooCommerce Stripe Gateway will allow e-commerce websites to straight settle for numerous payment solutions by way of Stripe’s payment processing API. It features of more than 900,000 active installations.
According to Patch security researcher Rafie Muhammad, the plugin suffers from what is actually identified as an unauthenticated Insecure direct object references (IDOR) vulnerability, which permits a bad actor to bypass authorization and obtain resources.

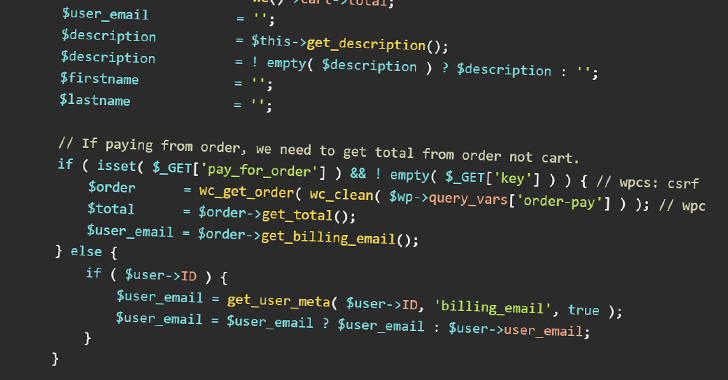
Specifically, the difficulty stems from the insecure handling of order objects and a absence of adequate obtain control system in the plugin’s ‘javascript_params’ and ‘payment_fields’ capabilities of the plugin.
“This vulnerability makes it possible for any unauthenticated consumer to look at any WooCommnerce order’s PII facts together with email, user’s name, and whole address,” Muhammad reported.
The growth comes months immediately after the WordPress main crew introduced 6.2.1 and 6.2.2 to handle five security issues, including an unauthenticated listing traversal vulnerability and an unauthenticated cross-web-site scripting flaw, three of which had been uncovered during a 3rd-bash security audit.
Observed this short article fascinating? Follow us on Twitter and LinkedIn to read additional unique articles we post.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft Releases Updates to Patch Critical Flaws in Windows and Other Software
Microsoft Releases Updates to Patch Critical Flaws in Windows and Other Software