The U.S. Cybersecurity and Infrastructure Security Company (CISA) and Federal Bureau of Investigation (FBI) have released a joint advisory relating to the lively exploitation of a a short while ago disclosed critical flaw in Development Software’s MOVEit Transfer application to drop ransomware.
“The Cl0p Ransomware Gang, also recognised as TA505, reportedly began exploiting a previously mysterious SQL injection vulnerability in Progress Software’s managed file transfer (MFT) alternative identified as MOVEit Transfer,” the businesses explained.
“Internet-going through MOVEit Transfer web apps ended up contaminated with a web shell named LEMURLOOT, which was then used to steal data from fundamental MOVEit Transfer databases.”
The prolific cybercrime gang has considering that issued an ultimatum to a number of impacted organizations, urging them to get in touch by June 14, 2023, or risk acquiring all their stolen knowledge revealed.

Microsoft is monitoring the exercise below the moniker Lace Tempest (aka Storm-0950), which has also been implicated in the exploitation of a critical security vulnerability in PaperCut servers.
Energetic considering the fact that at the very least February 2019, the adversary has been connected to a huge vary of routines in the cybercrime ecosystem, together with functioning a ransomware-as-a-service (RaaS) and performing as an affiliate for other RaaS techniques.
It has also been noticed performing as an first obtain broker (IAB) to earnings off entry to compromised enterprise networks and also as a client of other IABs, underscoring the interconnected character of the danger landscape.
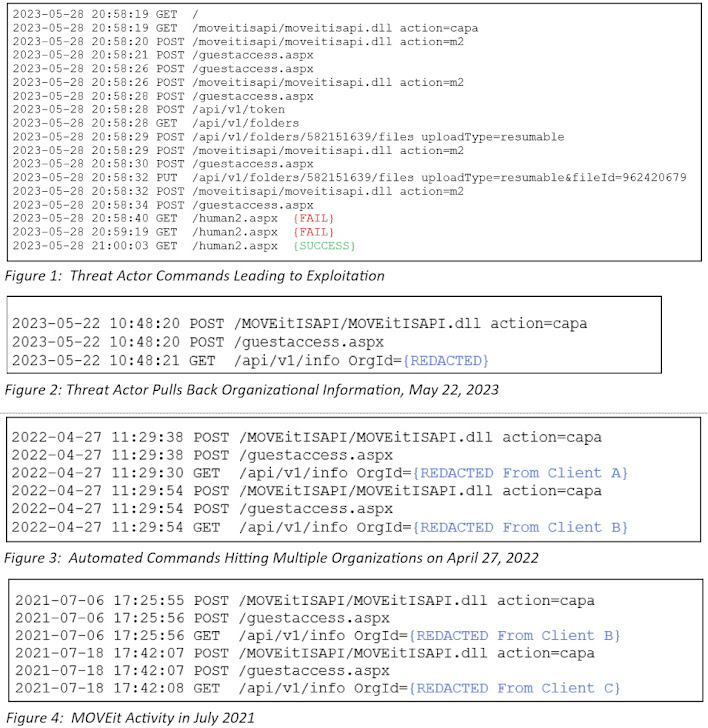 Resource: Kroll
Resource: Kroll
The abuse of CVE-2023-34362, an SQL injection flaw in MOVEit Transfer, is a indicator of the adversary consistently in search of zero-day exploits in internet-going through programs and utilizing them to their advantage in buy to extort victims.
It truly is truly worth noting that Cl0p carried out equivalent mass exploitation attacks on other managed file transfer programs this kind of as Accellion FTA and GoAnywhere MFT over the previous calendar year.
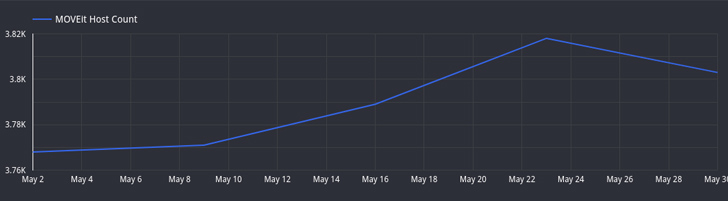
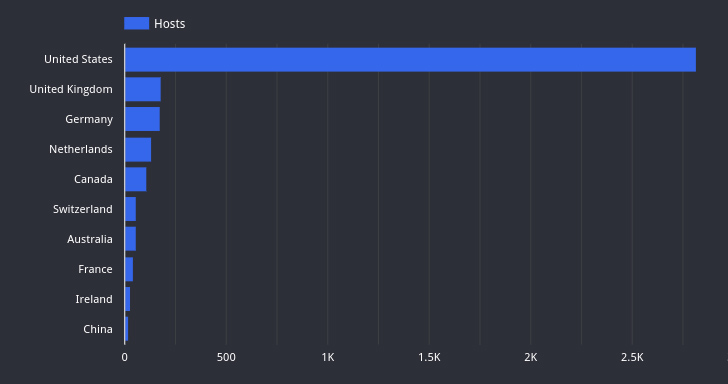
Attack area administration business Censys reported it has observed a drop in the quantity of hosts operating exposed MOVEit Transfer scenarios from more than 3,000 hosts to very little additional than 2,600.
“A number of of these hosts are involved with higher-profile businesses, which includes a number of Fortune 500 businesses and both condition and federal government organizations,” Censys famous, highlighting finance, technology, and healthcare as the sectors with the most exposures.
Future WEBINAR🔐 Mastering API Security: Knowledge Your Accurate Attack Surface area
Find the untapped vulnerabilities in your API ecosystem and take proactive actions towards ironclad security. Sign up for our insightful webinar!
Be part of the Session.wn-button,.wn-label,.wn-label:immediately aftershow:inline-block.look at_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px solid #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-major-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-appropriate-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-fat:600letter-spacing:.6pxcolor:#596cec.wn-label:afterwidth:50pxheight:6pxcontent:”border-best:2px stable #d9deffmargin: 8px.wn-titlefont-size:21pxpadding:10px 0font-weight:900textual content-align:leftline-top:33px.wn-descriptiontextual content-align:leftfont-measurement:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-color:#4469f5font-sizing:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-body weight:500letter-spacing:.2px
Kroll, in an evaluation shared with The Hacker Information, mentioned it identified action indicating that the Clop danger actors have been very likely experimenting with means to exploit this certain flaw in April 2022 and as far back again as July 2021.
The acquiring is particularly significant as it serves to illustrate the attacker’s specialized expertise and the planning that has gone into staging the intrusions substantially in advance of the current wave of exploitations started.
“Commands through the July 2021 time body appeared to be operate about a lengthier quantity of time, suggesting that testing could have been a manual system at that position before the group designed an automated option that it commenced tests in April 2022,” Kroll said.
The July 2021 exploitation is claimed to have originated from an IP tackle (45.129.137[.]232) that was beforehand attributed to the Cl0p actor in link with attempts to exploit flaws in SolarWinds Serv-U product or service around the exact same time.
“This is the third time Cl0p ransomware group have made use of a zero working day in webapps for extortion in 3 years,” security researcher Kevin Beaumont mentioned. “In all 3 situations they ended up items with security in the branding.”
Uncovered this article appealing? Observe us on Twitter and LinkedIn to go through a lot more distinctive content we publish.
Some parts of this article are sourced from:
thehackernews.com


 Interpol: Human Trafficking is Fueling Fraud Epidemic
Interpol: Human Trafficking is Fueling Fraud Epidemic