The North Korean country-state risk actor recognized as Kimsuky has been joined to a social engineering campaign focusing on industry experts in North Korean affairs with the intention of thieving Google qualifications and delivering reconnaissance malware.
“More, Kimsuky’s goal extends to the theft of membership qualifications from NK News,” cybersecurity company SentinelOne said in a report shared with The Hacker News.
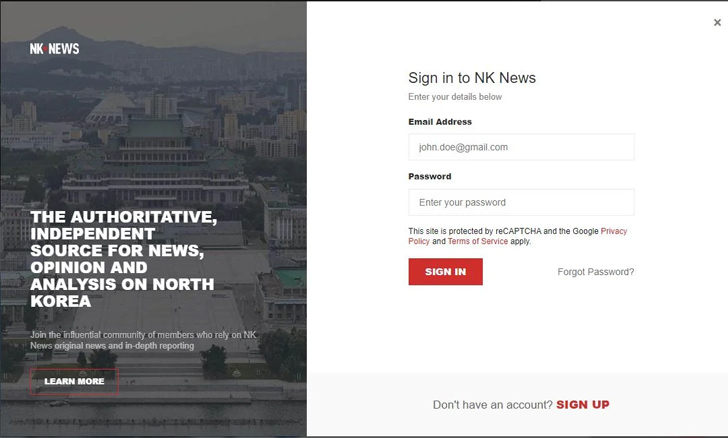
“To accomplish this, the team distributes email messages that lure qualified individuals to log in on the destructive website nknews[.]pro, which masquerades as the reliable NK News web site. The login variety that is presented to the concentrate on is developed to capture entered credentials.”
NK News, proven in 2011, is an American subscription-primarily based information website that supplies tales and examination about North Korea.
The disclosure arrives days after U.S. and South Korean intelligence companies issued an notify warning of Kimsuky’s use of social engineering practices to strike consider tanks, academia, and information media sectors. Past week, the risk team was sanctioned by South Korea’s Ministry of International Affairs.

Energetic considering that at the very least 2012, Kimsuky is identified for its spear-phishing techniques and its tries to build trust and rapport with intended targets prior to offering malware, a reconnaissance tool referred to as ReconShark.
The best aim of the campaigns is to collect strategic intelligence, geopolitical insights, and entry sensitive info that are of benefit to North Korea.
“Their solution highlights the group’s determination to developing a feeling of rapport with the folks they focus on, perhaps expanding the success rate of their subsequent destructive actions,” security researcher Aleksandar Milenkoski claimed.
The conclusions also adhere to new revelations from the South Korean federal government that far more than 130 North Korean watchers have been singled out as part of a phishing marketing campaign orchestrated by the governing administration-backed hacking team.
What is additional, with North Korea earning a significant chunk of its overseas-forex profits from cyber assaults and cryptocurrency heists, risk actors running on behalf of the regime’s passions have been observed spoofing monetary institutions and enterprise cash corporations in Japan, the U.S., and Vietnam.
Cybersecurity company Recorded Potential linked the action to a group tracked as TAG-71, a subgroup of Lazarus which is also identified as APT38, BlueNoroff, Nickel Gladstone, Sapphire Sleet, Stardust Chollima, and TA444.
Approaching WEBINAR🔐 Mastering API Security: Knowing Your Real Attack Surface
Find out the untapped vulnerabilities in your API ecosystem and consider proactive measures towards ironclad security. Sign up for our insightful webinar!
Be part of the Session.wn-button,.wn-label,.wn-label:followingdisplay screen:inline-block.verify_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px good #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-top rated-remaining-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-correct-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.wn-label:soon afterwidth:50pxheight:6pxcontent:”border-top rated:2px sound #d9deffmargin: 8px.wn-titlefont-size:21pxpadding:10px 0font-excess weight:900textual content-align:leftline-top:33px.wn-descriptiontextual content-align:leftfont-dimension:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-shade:#4469f5font-measurement:15pxcolor:#fff!importantborder:0line-top:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-excess weight:500letter-spacing:.2px
The adversarial collective has an founded observe document of mounting fiscally motivated intrusion strategies targeting cryptocurrency exchanges, business financial institutions, and e-commerce payment systems across the planet to illegally extract funds for the sanctions-strike region.
“The compromise of fiscal and expenditure corporations and their prospects may expose delicate or private details, which may result in authorized or regulatory action, jeopardize pending enterprise negotiations or agreements, or expose details detrimental to a firm’s strategic expense portfolio,” the corporation noted.
The chain of proof so considerably indicates that Lazarus Group’s motives are both of those espionage and fiscally pushed, what with the risk actor blamed for the the latest Atomic Wallet hack that led to the theft of crypto belongings worth $35 million, creating it the newest in a lengthy checklist of crypto businesses to be stung by hacks in excess of the previous number of several years.
“The laundering of the stolen crypto assets follows a series of ways that accurately match people utilized to launder the proceeds of earlier hacks perpetrated by Lazarus Team,” the blockchain analytics enterprise stated.
“The stolen property are remaining laundered making use of specific providers, together with the Sinbad mixer, which have also been utilized to launder the proceeds of earlier hacks perpetrated by the Lazarus Group.”
Identified this short article exciting? Stick to us on Twitter and LinkedIn to read through extra exceptional information we submit.
Some parts of this article are sourced from:
thehackernews.com


 Barracuda Urges Immediate Replacement of Hacked ESG Appliances
Barracuda Urges Immediate Replacement of Hacked ESG Appliances