Assaults on critical infrastructure and other OT techniques are on the rise as digital transformation and OT/IT convergencecontinue to speed up. H2o treatment method amenities, electrical power suppliers, factories, and chemical vegetation — the infrastructure that undergirds our day by day lives could all be at risk. Disrupting or manipulating OT programs stands to pose genuine actual physical harm to citizens, environments, and economies.
Still the landscape of OT security resources is significantly much less produced than its data technology (IT) counterpart. In accordance to a modern report from Takepoint Investigation and Cyolo, there is a notable absence of confidence in the applications typically utilized to safe remote access to industrial environments.
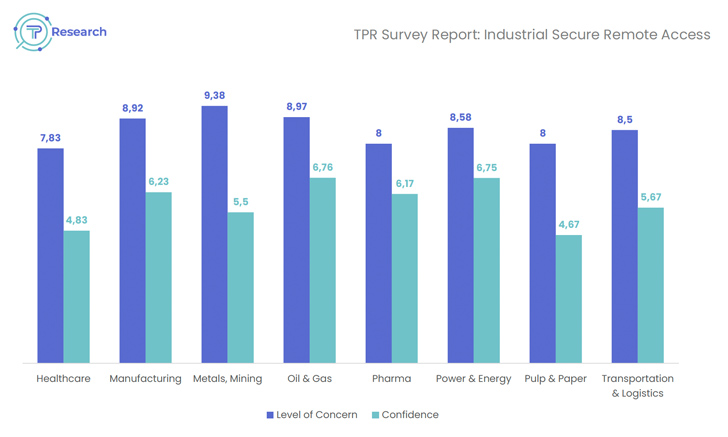 Determine 1: New investigate reveals a massive hole across industries between the level of issue about security dangers and the amount of self confidence in existing options for industrial safe remote access (I-SRA).
Determine 1: New investigate reveals a massive hole across industries between the level of issue about security dangers and the amount of self confidence in existing options for industrial safe remote access (I-SRA).
The standard security method of industrial environments was isolation – isolation not just from the internet but also from other inside programs. But now, with OT programs opening to the entire world and cyberthreats surging, the lack of OT-precise security resources has emerged as an urgent dilemma. In this void, IT solutions are usually cobbled together in an attempt to fulfill OT needs but, as you may well assume, the outcomes are normally lackluster.
Security alternatives created for IT environments merely won’t be able to fulfill the calls for of OT and industrial realities, for various key good reasons.
Purpose 1: OT prioritizes availability in excess of confidentiality
Although IT and OT both request to make sure confidentiality (the defense of sensitive knowledge and belongings), integrity (the fidelity of data around its lifecycle), and availability (the accessibility and responsiveness of resources and infrastructure), they prioritize unique parts of this CIA triad.
- It really is maximum priority is confidentiality. IT discounts in data, and the stakeholders of IT problem them selves with protecting that details — from trade secrets to the private info of end users and shoppers.
- OT’s highest precedence is availability. OT procedures run heavy-duty equipment in the actual physical realm, and for them, availability usually means safety. Downtime is only untenable when shutting off a blast furnace or industrial boiler tank.
For the sake of availability and responsiveness, most OT elements weren’t developed to accommodate security implementations at all.
This marks a essential variance in the incredibly DNA of IT and OT environments, which right away renders IT security applications tough to employ.
Explanation 2: OT units operate on generally-up legacy methods
For somebody dwelling in the IT earth, it may be hard to envision an ecosystem that even now runs on Windows XP or an eighties-period mainframe, but that’s the simple truth of the OT world. Whether for income or basic safety, OT methods are generally up and working at entire ability. This is why OT components are intended for a lot for a longer time everyday living cycles.
Practically all IT-centered resources have to have downtime for installation, updates, and patching. These routines are typically a non-starter for industrial environments, no issue how considerable a vulnerability may possibly be. Yet again, downtime for OT devices usually means putting basic safety at risk.
In addition, the legacy units that electrical power the OT environment normally cannot connect with contemporary security or authentication equipment, restricting the usefulness of these platforms from the very begin. Devoid of a security answer like Cyolo, which retrofits legacy applications to guidance modern-day security protocols, IT resources will be severely confined in their potential to safe OT methods.
Motive 3: IT resources pretty much constantly involve a link
IT security answers typically demand exterior relationship mainly because servers and applications ought to exchange info with just about every other (and with customers) to accomplish their important features. OT programs, by distinction, typically have certain specifications for how and when they can be connected to the internet (certainly, even in our age of digital transformation). IT equipment are not able to constantly be configured to fulfill these needs.
The nuance is that IT and OT programs can interface with each and every other with no forming a lasting connection. This way, OT environments can be positioned to achieve the rewards of automation, generation data, and other electronic transformation attempts without producing unnecessary accessibility points for destructive actors.
Motive 4: OT programs are remarkably variable
The IT earth has mostly standardized all over the TCP/IP protocol, but the OT environment lacks these consensus. OT systems use a huge wide range of communication protocols, which are frequently decided by the first products company.
For example, if an OT operator purchases programmable logic controllers (PLC) from quite a few unique providers, every company has most likely taken a diverse technique to conference IEC-61131 standards. Consequently, OT engineers have to discover and preserve as lots of sorts of computer software and protocols as they have suppliers.
Even inside OT, protocols are frequently incompatible with every other, and they are undoubtedly incompatible with common protocols utilised in IT-based mostly security equipment. It is uncertain that any IT device will go over the full spectrum of OT use cases for a supplied ecosystem.
Reason 5: OT units are sensitive
As a function of their variability and always-on nature, OT devices are effortlessly disrupted by the most fundamental IT procedures and security best procedures.
- Even passive scanning can knock fragile OT units offline, and by the time scanning is scaled down and restricted to offline techniques, security protection shrinks down below an acceptable stage.
- Logon banners that generally run on endpoints will crack the vehicle-login process for critical OT programs.
Since visibility is more difficult to obtain in OT environments, it can be tough to forecast the effects of deploying a new resource. For this explanation, OT methods frequently need extra intensive screening and validation prior to a new software is carried out.
OT environments have earned OT solutions
It truly is usually mentioned that tactic precedes tooling — and this is accurate. IT and security teams working in OT spaces should just take the time to recognize and embrace OT philosophies and desires, and collaborate with OT stakeholders to define finest techniques.
That explained, the ideal instruments nevertheless issue in a big way. The cybersecurity marketplace can be noisy and misleading. Alongside one another, IT and OT stakeholders must talk to the correct inquiries just before committing to a particular instrument or vendor.
The OT earth warrants the added benefits of fashionable security controls with no risking the security of staff, operations, or bystanders. Not only will the correct alternatives harden security postures in opposition to tomorrow’s assaults, they will place security to lead to innovation alternatively than stand in its way.
To discover much more about the prime worries at this time dealing with OT security professionals, browse the comprehensive report from Takepoint Research and Cyolo.
Uncovered this report appealing? Observe us on Twitter and LinkedIn to study extra exclusive information we post.
Some parts of this article are sourced from:
thehackernews.com


 Zero-Day Alert: Google Issues Patch for New Chrome Vulnerability – Update Now!
Zero-Day Alert: Google Issues Patch for New Chrome Vulnerability – Update Now!