Cybersecurity researchers have available a nearer look at the RokRAT distant entry trojan that’s used by the North Korean state-sponsored actor recognised as ScarCruft.
“RokRAT is a advanced distant entry trojan (RAT) that has been observed as a critical part in just the attack chain, enabling the menace actors to achieve unauthorized access, exfiltrate delicate facts, and potentially retain persistent management above compromised techniques,” ThreatMon said.
ScarCruft, lively given that at minimum 2012, is a cyber espionage group that operates on behalf of the North Korean government, completely focusing on targets in its southern counterpart.
The group is thought to be a subordinate element in North Korea’s Ministry of Condition Security (MSS). Attack chains mounted by the group have leaned seriously on social engineering to spear-phish victims and deliver payloads onto target networks.
This consists of exploiting vulnerabilities in Hancom’s Hangul Phrase Processor (HWP), a efficiency software package commonly utilized by community and private companies in South Korea, to deliver its signature malware dubbed RokRAT.
The Windows backdoor, also identified as DOGCALL, is actively created and preserved, and has considering that been ported to other operating systems these types of as macOS and Android.
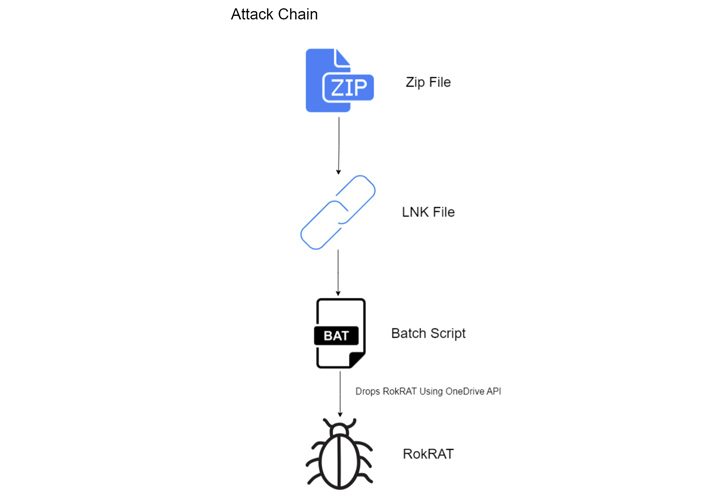
Modern spear-phishing assaults, as evidenced by the AhnLab Security Emergency reaction Center (ASEC) and Verify Level, have applied LNK files to trigger multi-stage infection sequences that at some point final result in the deployment of the RokRAT malware.
Approaching WEBINAR Zero Believe in + Deception: Understand How to Outsmart Attackers!
Find out how Deception can detect superior threats, halt lateral motion, and increase your Zero Believe in approach. Join our insightful webinar!
Help save My Seat!.ad-button,.advert-label,.advert-label:soon afterexhibit:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px sound #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-prime-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-proper-radius:25px-moz-border-radius-bottomright:25px.ad-labelfont-sizing:13pxmargin:20px 0font-pounds:600letter-spacing:.6pxcolor:#596cec.ad-label:afterwidth:50pxheight:6pxcontent:”border-best:2px stable #d9deffmargin: 8px.ad-titlefont-size:21pxpadding:10px 0font-pounds:900textual content-align:leftline-peak:33px.advertisement-descriptiontext-align:leftfont-dimension:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.advert-buttonpadding:6px 12pxborder-radius:5pxbackground-color:#4469f5font-sizing:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
RokRAT makes it possible for the adversary to harvest technique metadata, acquire screenshots, execute arbitrary instructions received from a remote server, enumerate directories, and exfiltrate information of desire.
The development arrives as ASEC disclosed a ScarCruft attack that leverages a Windows executable masquerading as a Hangul document to drop malware that is configured to get in touch with an external URL every 60 minutes.
“The URL registered in the undertaking scheduler seems to be a normal homepage, but it contains a web shell,” ASEC noted.
Found this article interesting? Comply with us on Twitter and LinkedIn to examine much more unique information we put up.
Some parts of this article are sourced from:
thehackernews.com


 Microsoft releases a temporary fix for Surface Pro X camera bug
Microsoft releases a temporary fix for Surface Pro X camera bug