An unfamiliar risk actor has been noticed leveraging a malicious Windows kernel driver in assaults most likely targeting the Middle East due to the fact at the very least May well 2020.
Fortinet Fortiguard Labs, which dubbed the artifact WINTAPIX (WinTapix.sys), attributed the malware with lower confidence to an Iranian threat actor.
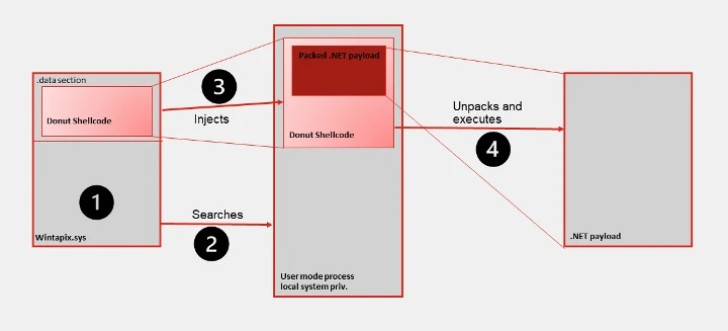
“WinTapix.sys is effectively a loader,” security scientists Geri Revay and Hossein Jazi stated in a report posted on Monday. “Thus, its major objective is to develop and execute the subsequent phase of the attack. This is accomplished employing a shellcode.”
Samples and telemetry facts analyzed by Fortinet clearly show that the campaign’s principal focus is on Saudi Arabia, Jordan, Qatar, and the United Arab Emirates. The activity has not been tied to a recognized menace actor or team.
By applying a destructive kernel manner driver, the idea is to subvert or disable security mechanisms and get entrenched accessibility to the qualified host.
This sort of drivers operate inside of the kernel memory and can, consequently, conduct any procedure, which includes altering critical security mechanisms and running arbitrary code with the greatest privileges.
In other words, it features a stealthy way to infiltrate deeper into the qualified system, retain persistence, and execute extra payloads or commands as aspect of the menace actor’s multi-stage attack.
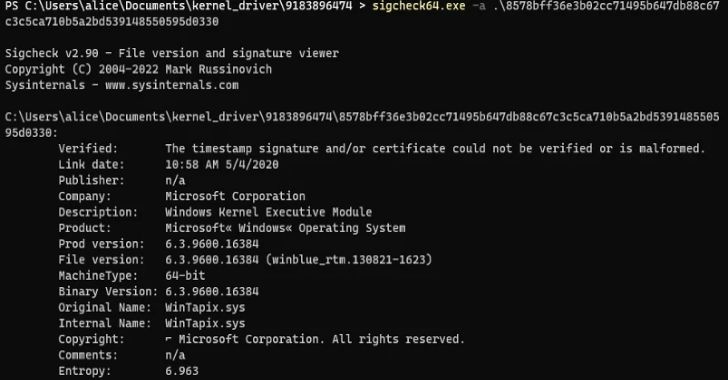
A essential security measure to mitigate in opposition to destructive motorists is Driver Signature Enforcement, which guarantees that only motorists signed by Microsoft can be loaded on the technique. The tech large also maintains driver block policies to protect from identified vulnerable motorists.
WinTapix.sys, on the other hand, comes with an invalid signature, indicating that the threat actor will have to initially load a authentic but vulnerable driver in order to start WINTAPIX.
Upcoming WEBINARZero Rely on + Deception: Discover How to Outsmart Attackers!
Learn how Deception can detect sophisticated threats, stop lateral motion, and improve your Zero Trust technique. Be a part of our insightful webinar!
Preserve My Seat!
But when it is really loaded in the kernel, WinTapix.sys is configured to inject an embedded shellcode into an ideal consumer manner process that, in flip, executes an encrypted .NET payload.
WINTAPIX, moreover embedding the shellcode produced utilizing the open up resource Donut challenge, establishes persistence by signifies of Windows Registry modifications that permits it to be loaded even when the device is booted in Safe and sound Manner.
For its component, the .NET malware is equipped with backdoor and proxy characteristics to execute commands, carry out file download and upload, and operate as a proxy to pass facts concerning two communication endpoints.
“Since Iranian risk actors are recognised to exploit Trade servers to deploy extra malware, it is also possible that this driver has been utilized along with Trade attacks,” the researchers mentioned.
“To that position, the compilation time of the drivers is also aligned with occasions when Iranian danger actors had been exploiting Exchange server vulnerabilities.”
The advancement arrives as the ALPHV (aka BlackCat or Noberus) ransomware team has been observed taking edge of a malicious signed driver to impair security defenses and escape detection for extended durations of time.
The driver in question, ktgn.sys, is an up to date model of POORTRY that’s signed using a stolen or leaked cross-signing certification, cybersecurity business Craze Micro claimed in a report.
POORTRY is the title assigned to a Windows kernel driver that arrives with abilities to terminate security software. Late very last yr, it was disclosed as employed by ransomware gangs and a threat actor recognised as UNC3944 (aka Roasted 0ktapus and Scattered Spider).
“Malicious actors that are actively seeking substantial-privilege obtain to the Windows operating technique use strategies that try to fight the elevated safety on users and processes by means of endpoint security system (EPP) and endpoint detection and response (EDR) technologies,” Pattern Micro mentioned.
“These malicious actors also are likely to have plenty of economic assets to both invest in rootkits from underground resources or to purchase code-signing certificates to establish a rootkit.”
Identified this post attention-grabbing? Comply with us on Twitter and LinkedIn to browse extra exceptional articles we put up.
Some parts of this article are sourced from:
thehackernews.com

 Two-Thirds of IT Leaders Say GDPR Has Reduced Consumer Trust
Two-Thirds of IT Leaders Say GDPR Has Reduced Consumer Trust