The most precious asset in today’s details age is the secret safeguarded below lock and key. Regrettably, retaining secrets has turn out to be progressively challenging, as highlighted by the 2023 Condition of Secrets Sprawl report, the premier evaluation of general public GitHub exercise.
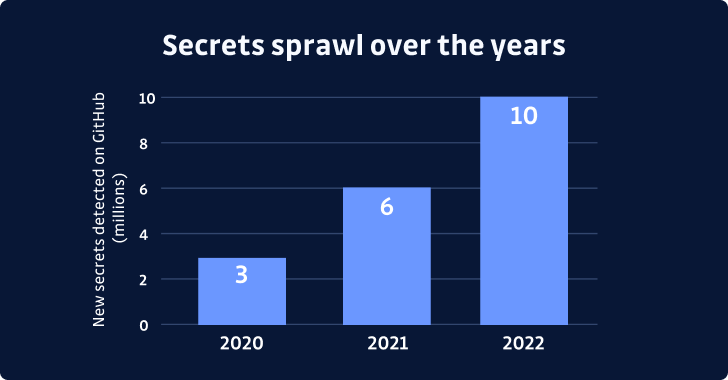
The report shows a 67% year-more than-calendar year raise in the selection of techniques identified, with 10 million tricky-coded techniques detected in 2022 on your own. This alarming surge in techniques sprawl highlights the have to have for motion and underscores the importance of secure application enhancement.
Secrets and techniques sprawl refers to insider secrets showing in plaintext in different sources, these types of as supply code, develop scripts, infrastructure as code, logs, etcetera. Whilst insider secrets like API tokens and personal keys securely link the parts of the modern-day program provide chain, their widespread distribution among developers, machines, apps, and infrastructure methods heightens the chance of leaks.
Cybersecurity Incidents Highlight the Risks of Tricky-Coded Insider secrets
Two superior-profile cybersecurity incidents involving Uber and Toyota have underlined the urgent have to have to handle the issue of strategies sprawl and prioritize code security. As awareness all-around this issue grows, it is critical for companies to prioritize the safety of tricks and make investments in modern solutions that detect and remediate possible threats.
Uber suffered an attack in which an attacker gained access to critical methods applying hard-coded admin credentials uncovered in a PowerShell script. In distinction, Toyota inadvertently uncovered qualifications granting entry to purchaser data in a community GitHub repository for nearly 5 several years. Both incidents serve as glaring reminders of the pitfalls related with secrets sprawl. Also, as the report points out, most security incidents require, at some place, techniques: it may perhaps be keys leveraged by attackers or exposed through leaked resource code, for occasion.
A Major Blind Spot in Software Security
With 1 out of each 10 code authors exposing a mystery in 2022, it is really evident that this issue transcends working experience degrees and afflicts developers across the board.
Secrets administration is getting increased awareness as extra companies scrutinize their software source chain processes next a string of high-profile security breaches. Cybersecurity teams have customarily centered on figuring out vulnerabilities instead than uncovering poorly secured credentials. As a final result, countless purposes working in output environments might have undiscovered secrets management issues.
In a great state of affairs, adopting DevSecOps most effective procedures would deal with this rising issue. Yet, with the continuous enlargement of code repositories, far more standard mistakes seem. Recognizing application source chain vulnerabilities, cybercriminals proactively scan repositories to come across tricks that could aid software breaches.
The issue will probable worsen as assaults on software package provide chains are predicted to escalate. As technology advances and code gets to be extra entwined with our daily lives, the challenges affiliated with secrets sprawl turn into additional pressing.
The intensified aim on securing application supply chains, especially in gentle of the Biden administration’s Nationwide Cybersecurity Technique, is anticipated to travel more IT businesses to put into action finish-to-stop security steps in just their program advancement daily life cycles. As a result, DevOps teams must anticipate anincreased aim on strategies management from cybersecurity gurus.
Embracing Proactive Measures to Mitigate Techniques Sprawl Threats
To beat this escalating danger, businesses have to prioritize the defense of their techniques and invest in remedies for detecting and addressing potential vulnerabilities.
The continued development of the anything-as-code paradigm and the commoditization of electronic infrastructure and products and services means that software program, code, and secrets and techniques will only develop into extra critical in their day-to-day company operations.
The risk of techniques publicity cannot completely be eradicated, even with centralized top secret administration programs. But it can be mitigated by addressing lousy secrets hygiene methods and implementing remediation playbooks.
To measure how considerably a techniques detection and remediation program could carry to your firm, you can use our no cost Price Calculator to estimate the probable price tag of not dealing with a security debt consisting of 1000’s of difficult-coded strategies now.
By mastering to live with this issue and placing the suitable tools and assets in spot, businesses can considerably reduce the risks linked with leaked and exploited secrets and techniques.
In conclusion, tricks sprawl is a developing menace requiring organizations’ rapid attention. With the suitable equipment and strategies in put, providers can mitigate the risks associated with leaked and exploited secrets. It is time to prioritize secrets administration and commit in modern remedies to ensure our secrets stay safe and protected.
In a world the place facts is electric power, it’s time to take action and guarantee our tricks keep on being securely beneath lock and important.
Observed this posting interesting? Follow us on Twitter and LinkedIn to browse much more unique content material we put up.
Some parts of this article are sourced from:
thehackernews.com


 New WinTapix.sys Malware Engages in Multi-Stage Attack Across Middle East
New WinTapix.sys Malware Engages in Multi-Stage Attack Across Middle East