A monetarily motivated danger actor of Indonesian origin has been noticed leveraging Amazon Web Products and services (AWS) Elastic Compute Cloud (EC2) scenarios to carry out illicit crypto mining functions.
Cloud security firm’s Permiso P0 Labs, which initial detected the team in November 2021, has assigned it the moniker GUI-vil (pronounced Goo-ee-vil).
“The group shows a preference for Graphical Person Interface (GUI) tools, especially S3 Browser (edition 9.5.5) for their initial operations,” the company mentioned in a report shared with The Hacker Information. “On gaining AWS Console access, they perform their functions instantly as a result of the web browser.”
Attack chains mounted by GUI-vil entail getting original access by weaponizing AWS keys in publicly exposed supply code repositories on GitHub or scanning for GitLab occasions that are vulnerable to remote code execution flaws (e.g., CVE-2021-22205).
A prosperous ingress is adopted by privilege escalation and an inside reconnaissance to assessment all readily available S3 buckets and ascertain the providers that are accessible via the AWS web console.
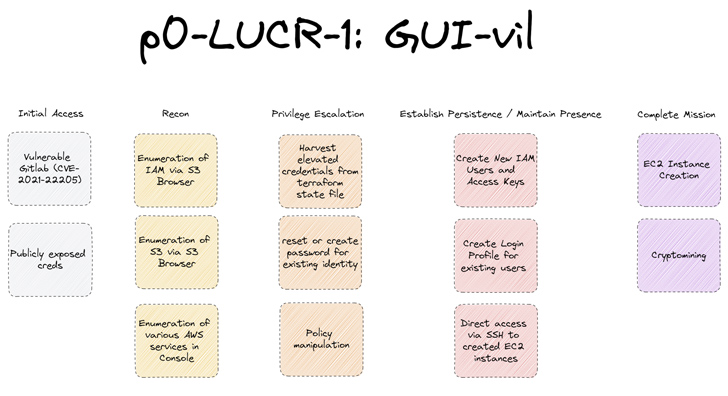
A noteworthy aspect of the threat actor’s modus operandi is its endeavor to mix in and persist within just the victim atmosphere by generating new buyers that conform to the same naming conference and finally meet up with its objectives.
“GUI-vil will also produce entry keys for the new identities they are creating so they can proceed use of S3 Browser with these new users,” the organization stated.
Impending WEBINARZero Have faith in + Deception: Master How to Outsmart Attackers!
Discover how Deception can detect state-of-the-art threats, cease lateral motion, and increase your Zero Have faith in technique. Sign up for our insightful webinar!
Preserve My Seat!
Alternatively, the team has also been spotted building login profiles for existing customers that do not have them so as to permit obtain to the AWS console without having elevating purple flags.
GUI-vil’s backlinks to Indonesia stem from the fact that the supply IP addresses affiliated with the functions are joined to two Autonomous System Quantities (ASNs) situated in the Southeast Asian state.
“The group’s principal mission, monetarily driven, is to develop EC2 occasions to aid their crypto mining functions,” researchers mentioned. “In quite a few instances the revenue they make from crypto mining are just a sliver of the price the target corporations have to pay out for jogging the EC2 occasions.”
Located this report appealing? Adhere to us on Twitter and LinkedIn to read through far more unique content material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Bad Magic’s Extended Reign in Cyber Espionage Goes Back Over a Decade
Bad Magic’s Extended Reign in Cyber Espionage Goes Back Over a Decade