The id of the 2nd risk actor guiding the Golden Chickens malware has been uncovered courtesy of a fatal operational security blunder, cybersecurity company eSentire said.
The particular person in concern, who lives in Bucharest, Romania, has been presented the codename Jack. He is just one of the two criminals running an account on the Russian-language Exploit.in forum underneath the identify “badbullzvenom,” the other being “Chuck from Montreal.”
eSentire characterized Jack as the genuine mastermind powering Golden Chickens. Evidence unearthed by the Canadian organization displays that he is also shown as the proprietor of a vegetable and fruit import and export organization.
“Like ‘Chuck from Montreal,’ ‘Jack’ employs various aliases for the underground boards, social media, and Jabber accounts, and he also has absent to fantastic lengths to disguise himself,” eSentire researchers Joe Stewart and Keegan Keplinger claimed.
“‘Jack’ has taken good pains to obfuscate the Golden Chickens malware, trying to make it undetectable by most [antivirus] organizations, and strictly allowing for only a smaller range of buyers to obtain access to the Golden Chickens MaaS.”
Golden Chickens (aka Far more_eggs) is a malware suite employed by economically-enthusiastic cybercrime actors these kinds of as Cobalt Team and FIN6. The threat actors at the rear of the malware, also identified as Venom Spider, run underneath a malware-as-a-assistance (MaaS) product.
The JavaScript malware is distributed by means of phishing campaigns and will come with quite a few parts to harvest financial information, carry out lateral motion, and even fall a ransomware plugin for PureLocker known as TerraCrypt.
Jack’s online routines, in accordance to eSentire, go all the way again to 2008, when he was just 15 several years aged and signed up for many cybercrime community forums as a amateur member. All his aliases are becoming collectively tracked as Blessed.
The investigation, in putting alongside one another his digital trail, traces Jack’s progression from a teenager interested in creating malicious courses to a longtime hacker involved in building password stealers, crypters, and Much more_eggs.
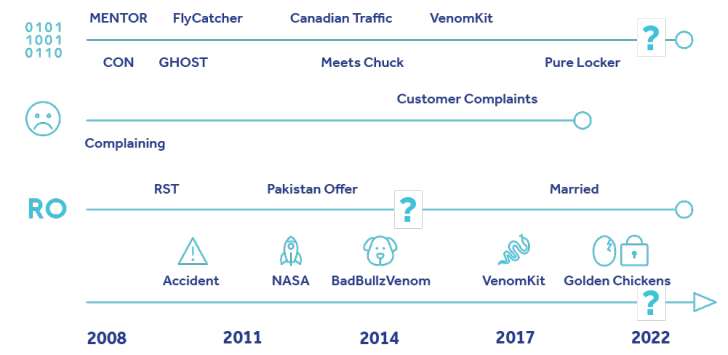
Some of the earliest malware resources made by Jack in 2008 consisted of Voyer, which is able of harvesting a user’s Yahoo instantaneous messages, and an information and facts stealer christened FlyCatcher that can document keystrokes.
A yr afterwards, Jack introduced a new password stealer dubbed CON which is made to siphon qualifications from unique web browsers, VPN, and FTP purposes as properly as now-defunct messaging applications like MSN Messenger and Yahoo! Messenger.
Jack, afterwards that similar year, started promoting a crypter referred to as GHOST to support other actors encrypt and obfuscate malware with the purpose of evading detection. The unanticipated demise of his father in a automobile accident is considered to have induced him to pause enhancement of the device in 2010.
Rapid ahead to 2012, Jack began to achieve a reputation in the cybercriminal local community as a scammer for failing to deliver satisfactory support to clients buying the merchandise from him.
He also cited “major everyday living issues” in a discussion board write-up on April 27, 2012, stating he is contemplating going to Pakistan to operate for the governing administration as a security specialist and that a single among his crypter prospects “works at pakistan guv” [read government].
Forthcoming WEBINARZero Belief + Deception: Study How to Outsmart Attackers!
Learn how Deception can detect highly developed threats, halt lateral movement, and boost your Zero Belief approach. Be a part of our insightful webinar!
Preserve My Seat!
It truly is not quickly distinct if Jack finished up going to Pakistan, but eSentire explained it noticed tactical overlaps amongst a 2019 marketing campaign carried out by a Pakistani risk actor recognised as SideCopy and Jack’s VenomLNK malware, which capabilities as the preliminary entry vector for the More_eggs backdoor.
Jack is suspected to have crossed paths with “Chuck from Montreal” someday between late 2012 and Oct 4, 2013, the day on which a concept was posted from Chuck’s badbullz account on the Lampeduza forum made up of get in touch with info – a Jabber address – linked with Fortunate.
It’s speculated that Jack brokered a offer with Chuck that would allow for him to write-up underneath Chuck’s aliases “badbullz” and “badbullzvenom” on many underground forums as a way to get all over his notoriety as a ripper.
Lending credence to this hypothesis is the point that 1 of LUCKY’s new resources, a kit for building macros identified as MULTIPLIER, was launched in 2015 by means of the badbullzvenom account, while the menace actor driving the Blessed account ceased posting as a result of that tackle.
“By working with the badbullzvenom and badbullz accounts, and unbeknownst to discussion board associates, he is in essence commencing with a clean slate, and he can continue to make his reliability below the account aliases: badbullz and badbullzvenom,” the researcher stated.
Subsequently in 2017, badbullzvenom (aka Lucky) unveiled a individual tool named VenomKit, which has since advanced into the Golden Chickens MaaS. The malware’s ability to evade detection also caught the focus of Cobalt Team, a Russia-based mostly cybercrime gang that leveraged it to deploy Cobalt Strike in attacks aimed at money entities.
Two decades afterwards, one more fiscally inspired threat actor labeled FIN6 (aka ITG08 or Skeleton Spider) was noticed employing the Golden Chickens provider to anchor its intrusions targeting stage-of-sale (POS) devices utilised by retailers in Europe and the U.S.
The cybersecurity business said it also found the identities of his wife, mother, and two sisters. He and his spouse are explained to reside in an upscale section of Bucharest, with his wife’s social media accounts documenting their outings to cities like London, Paris, and Milan. The pics further more show them putting on designer clothing and components.
“The danger actor who went by the alias Fortunate and who also shares the badbullz and badbullzvenom accounts with the Montreal-based cybercriminal ‘Chuck,’ created his deadly error when he used the Jabber account,” the scientists said.
Uncovered this article fascinating? Observe us on Twitter and LinkedIn to read extra unique material we article.
Some parts of this article are sourced from:
thehackernews.com


 Notorious Cyber Gang FIN7 Returns Cl0p Ransomware in New Wave of Attacks
Notorious Cyber Gang FIN7 Returns Cl0p Ransomware in New Wave of Attacks