Two malicious offers found out in the npm package deal repository have been observed to conceal an open supply facts stealer malware identified as TurkoRat.
The offers – named nodejs-encrypt-agent and nodejs-cookie-proxy-agent – had been collectively downloaded somewhere around 1,200 periods and ended up obtainable for more than two months in advance of they ended up discovered and taken down.
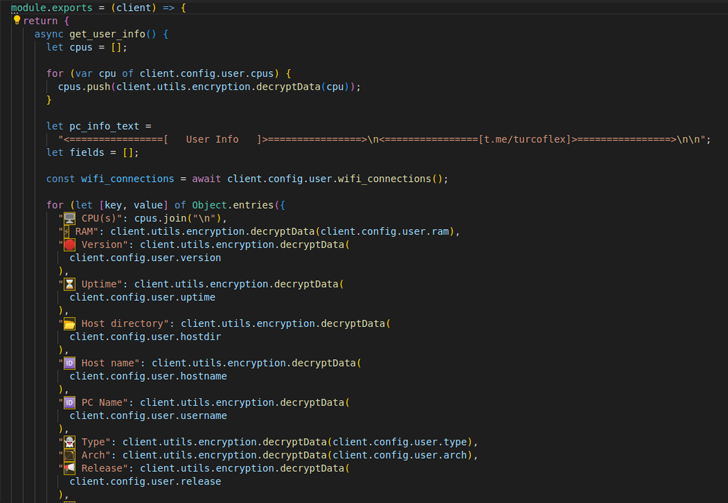
ReversingLabs, which broke down the facts of the campaign, explained TurkoRat as an information and facts stealer able of harvesting sensitive information these as login credentials, web-site cookies, and data from cryptocurrency wallets.
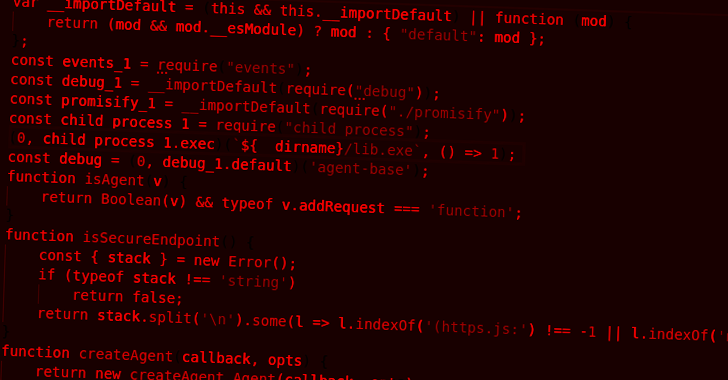
Whilst nodejs-encrypt-agent came equipped with the malware inside, nodejs-cookie-proxy-agent was located to disguise the trojan as a dependency less than the title axios-proxy.
nodejs-encrypt-agent was also engineered to masquerade as a different legitimate npm module known as agent-base, which has been downloaded in excess of 25 million moments to date.
The checklist of the rogue packages and their connected variations are detailed below –
- nodejs-encrypt-agent (versions 6..2, 6..3, 6..4, and 6..5)
- nodejs-cookie-proxy-agent (versions 1.1., 1.2., 1.2.1, 1.2.2, 1.2.3, and 1.2.4), and
- axios-proxy (variations 1.7.3, 1.7.4, 1.7.7, 1.7.9, 1.8.9, and 1.9.9)
“TurkoRat is just 1 of numerous open up source malware households that are provided for ‘testing’ applications, but can commonly be downloaded and modified for destructive use, as very well,” Lucija Valentić, risk researcher at ReversingLabs, explained.
The findings at the time once again underscore the ongoing risk of threat actors orchestrating offer chain attacks by means of open source offers and baiting builders into downloading possibly untrusted code.
“Enhancement businesses need to have to scrutinize the capabilities and behaviors of the open source, 3rd-bash and industrial code they are relying on in buy to keep track of dependencies and detect opportunity malicious payloads in them,” Valentić explained.
The developing use of destructive npm packages matches in with a broader sample of surging attacker interest in open up source computer software offer chains, not to point out highlighting the escalating sophistication of threat actors.
Even extra worryingly, scientists from Checkmarx revealed new research this month that confirmed how risk actors could impersonate reliable npm deals by “making use of lowercase letters to mimic uppercase letters in the unique bundle names” (e.g., memoryStorageDriver vs memorystoragedriver).
“This malicious package impersonation will take the standard ‘Typosquatting,’ attack technique to a new level, wherever attackers sign-up package deal names that consist of the correct identical letters as the legit kinds, with the only difference remaining capitalization,” scientists Instruct Zornstein and Yehuda Gelb reported.
“This tends to make it even more difficult for users to detect the deception because it can be straightforward to forget the refined differences in capitalization.”
The provide chain security company located that 1,900 out of 3,815 deals with money letters in their titles could have been at risk of copycat attacks if not for a correct pushed by the npm maintainers to handle the trouble, which, Checkmarx reported, has existed considering the fact that December 2017.
The disclosure also follows an additional advisory from Look at Position, which determined a few malicious extensions hosted on the VS Code extensions market. They have been purged as of May possibly 14, 2023.
The include-ons, named prettiest java, Darcula Dark, and python-vscode, had been cumulatively downloaded more than 46,000 occasions and included attributes that authorized the danger actors to steal credentials, process facts, and set up a remote shell on the victim’s machine.
Impending WEBINARZero Have confidence in + Deception: Discover How to Outsmart Attackers!
Learn how Deception can detect innovative threats, quit lateral motion, and enhance your Zero Have faith in system. Be a part of our insightful webinar!
Help save My Seat!
It is not just npm and VS Code marketplace, for a comparable set of rogue libraries have been unearthed from the Python Package deal Index (PyPI) software program repository as effectively.
Some of these packages have been designed to distribute a cryptocurrency clipper malware dubbed KEKW, even though other typosquatted variations of the common flask framework integrated backdoor features to get instructions from a remote server.
One more Python package uncovered by Israeli firm Phylum this 7 days was found to have a destructive dependency that harbored an encrypted payload to seize Discord tokens and steal clipboard written content in order to hijack cryptocurrency transactions.
The deal, referred to as chatgpt-api by its developer Patrick Pogoda and obtainable as a result of GitHub, sent on the features it advertised (i.e., interacting with OpenAI’s ChatGPT device) in an endeavor to finish the ruse. The repository is continue to offered as of crafting.
“For now this actor seems to be preying on the new explosive rise in recognition of [Large Language Models] with this chatgpt-api package,” Phylum mentioned, introducing the menace actor has an automatic mechanism to add new iterations of the destructive dependency each time it truly is taken down and “sustain a persistent infection.”
Located this short article attention-grabbing? Stick to us on Twitter and LinkedIn to go through more distinctive content material we post.
Some parts of this article are sourced from:
thehackernews.com

 Teen Charged in DraftKings Credential Stuffing Case
Teen Charged in DraftKings Credential Stuffing Case