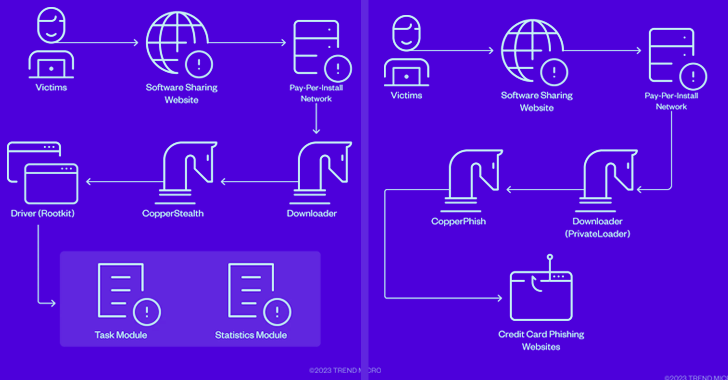
The risk actors at the rear of the CopperStealer malware resurfaced with two new campaigns in March and April 2023 that are built to supply two novel payloads dubbed CopperStealth and CopperPhish.
Pattern Micro is monitoring the financially determined team below the identify Water Orthrus. The adversary is also assessed to be at the rear of yet another campaign identified as Scranos, which was in-depth by Bitdefender in 2019.
Active considering that at the very least 2021, H2o Orthrus has a keep track of file of leveraging pay-for each-set up (PPI) networks to redirect victims landing on cracked software download internet sites to drop an information and facts stealer codenamed CopperStealer.
A different campaign spotted in August 2022 entailed the use of CopperStealer to distribute Chromium-centered web browser extensions that are capable of performing unauthorized transactions and transferring cryptocurrency from victims’ wallets to ones less than attackers’ control.

The latest attack sequences documented by Pattern Micro don’t mark a great deal of a deviation, propagating CopperStealth by packaging it as installers for absolutely free equipment on Chinese software program-sharing internet websites.
“CopperStealth’s infection chain includes dropping and loading a rootkit, which afterwards injects its payload into explorer.exe and yet another program procedure,” security scientists Jaromir Horejsi and Joseph C Chen explained in a complex report.
“These payloads are liable for downloading and operating more responsibilities. The rootkit also blocks obtain to blocklisted registry keys and prevents specified executables and motorists from managing.”
The driver denylist contains byte sequences pertaining to Chinese security software program organizations like Huorong, Kingsoft, and Qihoo 360.
CopperStealth also incorporates a job module that permits it to connect with out to a remote server and retrieve the command to be executed on the infected device, equipping the malware to drop more payloads.
File Sharing Web sites Act as Conduit for CopperPhish Phishing Package
The CopperPhish campaign, detected throughout the world in April 2023, takes advantage of an analogous system to deploy the malware via PPI networks driving free of charge anonymous file-sharing web-sites.
“Site visitors will be redirected to a obtain site intended by the PPI network immediately after clicking on its ads, which pretended to be a obtain link,” the scientists said. “The downloaded file is PrivateLoader, which downloads and operates many unique malware.”
The downloader assistance, which is also presented on a PPI foundation, is then employed to retrieve and launch CopperPhish, a phishing package which is responsible for harvesting credit score card info.
It achieves this by “starting up a rundll32 procedure and injecting a uncomplicated system with a browser window (prepared in Visible Primary) in it,” which masses a phishing page urging victims to scan a QR code in get to verify their id and enter a confirmation code to “restore your device’s network.”
“The window has no controls that can be utilized to lessen or close it,” the researchers described. “The target could shut the browser’s method in Activity Supervisor or Course of action Explorer, but they would also will need to terminate the major payload approach, if not the browser procedure will take place yet again owing to the persistence thread.”
The moment the sensitive aspects are entered in the page, the CopperPhish malware displays the concept “the identity verification has passed” along with a affirmation code that the target can enter on the aforementioned display.
Forthcoming WEBINARLearn to Halt Ransomware with True-Time Protection
Be a part of our webinar and discover how to halt ransomware assaults in their tracks with true-time MFA and services account defense.
Help save My Seat!
Providing the suitable affirmation code also causes the malware to uninstall itself and delete all the dropped phishing files from the equipment.
“The credential verification and confirmation code are two valuable options that make this phishing kit more successful, as the target can’t merely near the window or enter phony information just to get rid of the window,” the scientists explained.
The attribution to Drinking water Orthrus is dependent on the simple fact that the two CopperStealth and CopperPhish share equivalent source code characteristics as that of CopperStealer, increasing the likelihood that all 3 strains might have been created by the exact author.
The disparate aims of the campaigns depict the evolution of the danger actor’s techniques, indicating an try to include new capabilities to its arsenal and extend its economic horizons.
The conclusions occur as malicious Google advertisements are being applied to entice consumers into downloading fake installers for AI equipment like Midjourney and OpenAI’s ChatGPT that eventually drop stealers these as Vidar and RedLine.
They also comply with the discovery of a new site visitors-monetizing company referred to as TrafficStealer that leverages misconfigurations containers to redirect targeted visitors to websites and generate phony ad clicks as section of an illicit revenue-generating scheme.
Uncovered this short article attention-grabbing? Follow us on Twitter and LinkedIn to study much more distinctive content material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Researchers Uncover New “RA Group” Ransomware
Researchers Uncover New “RA Group” Ransomware